Context Aware Access Documentation Center
Network Access And Context Aware Settings Amplified It This document describes how you can use context aware access to secure different types of apps and resources. context aware access is a security approach where you control users' access. Afi provides context aware access policies that let you enforce access restrictions based on a user’s ip address, country, or identity provider. these access policies are managed on the configuration → access policies tab in the afi portal and apply to all users accessing the corresponding afi organization account.
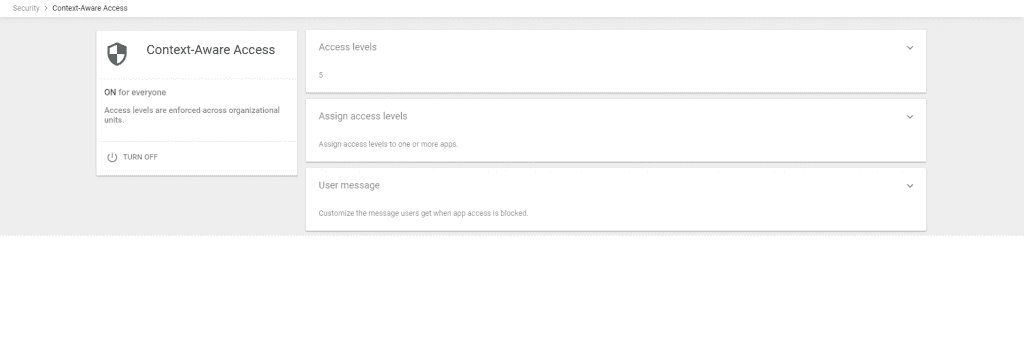
Network Access And Context Aware Settings Amplified It Visit the help center to learn more about context aware access, creating context aware access levels, and assigning access levels to third party apps. end users: if enabled by your admin, you can access certain apps when authenticating using your google sign in. This example defines a custom access level that requires the user to use a cloud managed chrome browser (cbcm) or be logged into a cloud managed chrome profile. What is context aware access? context aware access is a security setting that checks for minimum security standards on a device before allowing it to access certain data. Learn how to deploy context aware access in google workspace to enhance security by enforcing adaptive policies based on user identity, location, and more.
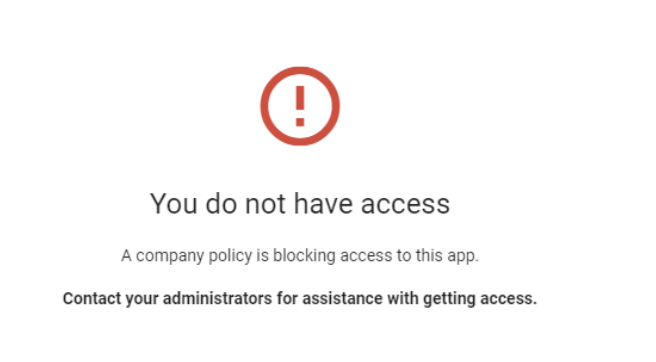
Network Access And Context Aware Settings Amplified It What is context aware access? context aware access is a security setting that checks for minimum security standards on a device before allowing it to access certain data. Learn how to deploy context aware access in google workspace to enhance security by enforcing adaptive policies based on user identity, location, and more. Discover how modern iam platforms leverage context—like location, device, time, and risk signals—to power adaptive, risk based access. explore the benefits, implementation strategies, and common pitfalls of context aware access controls for smarter security. Enforce context aware access policies for web apps hosted on gcp, on your premises, or other public clouds, including amazon web services (aws) and microsoft azure. Using context aware access, we can protect access to the google cloud console, apis, vms, workspace, and many other resources in a way that not only takes the user’s identity into account, but also other factors such as their location, browser, and device posture. In this paper, we propose a fog based adaptive context aware access control (fb acaac) framework for iot devices, dynamically adjusting access policies based on contextual information to prevent unauthorised resource access.

Context Aware Discover how modern iam platforms leverage context—like location, device, time, and risk signals—to power adaptive, risk based access. explore the benefits, implementation strategies, and common pitfalls of context aware access controls for smarter security. Enforce context aware access policies for web apps hosted on gcp, on your premises, or other public clouds, including amazon web services (aws) and microsoft azure. Using context aware access, we can protect access to the google cloud console, apis, vms, workspace, and many other resources in a way that not only takes the user’s identity into account, but also other factors such as their location, browser, and device posture. In this paper, we propose a fog based adaptive context aware access control (fb acaac) framework for iot devices, dynamically adjusting access policies based on contextual information to prevent unauthorised resource access.
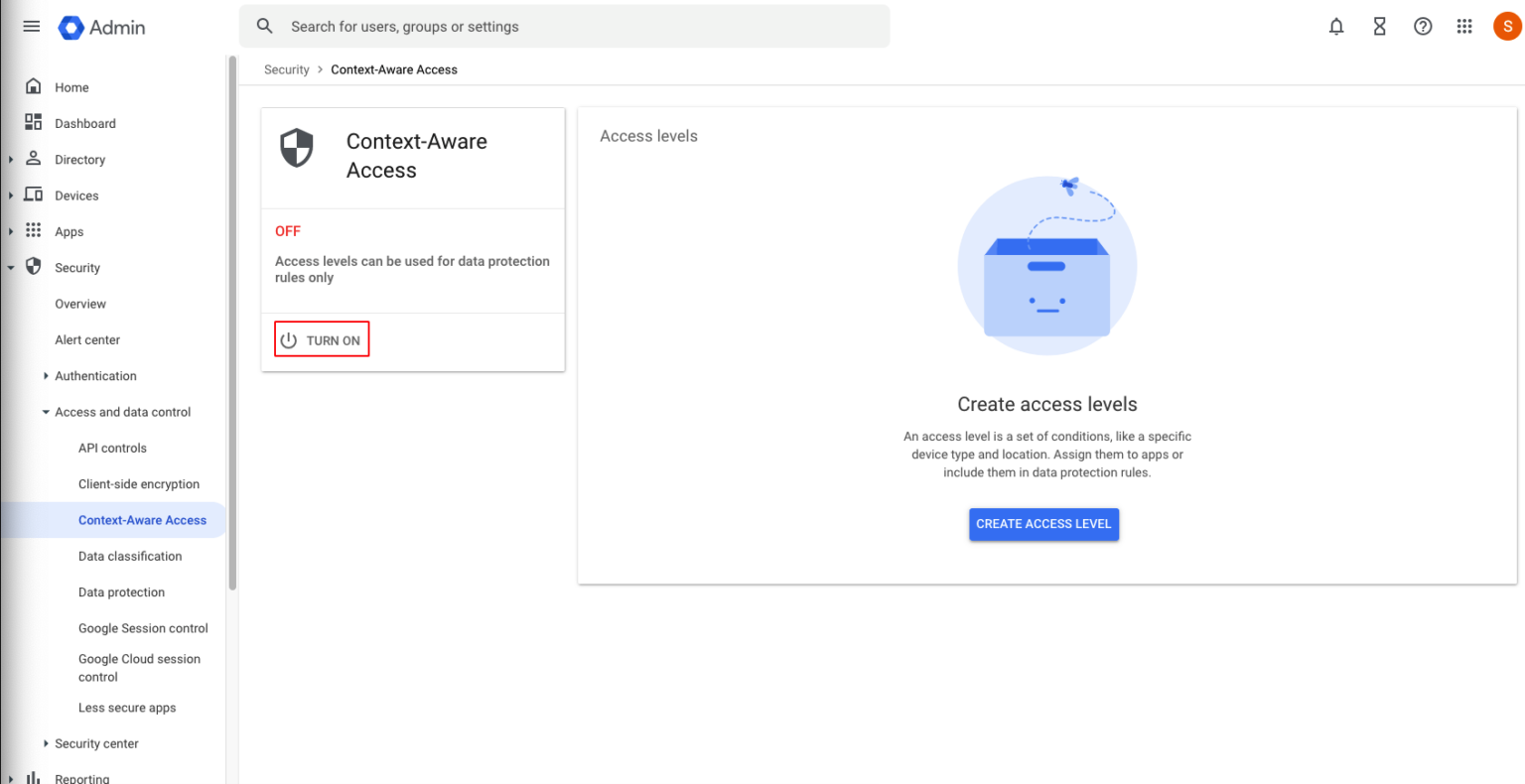
Create Context Aware Access Policies Netskope Knowledge Portal Using context aware access, we can protect access to the google cloud console, apis, vms, workspace, and many other resources in a way that not only takes the user’s identity into account, but also other factors such as their location, browser, and device posture. In this paper, we propose a fog based adaptive context aware access control (fb acaac) framework for iot devices, dynamically adjusting access policies based on contextual information to prevent unauthorised resource access.
Comments are closed.