Constant Encryption Bytehide
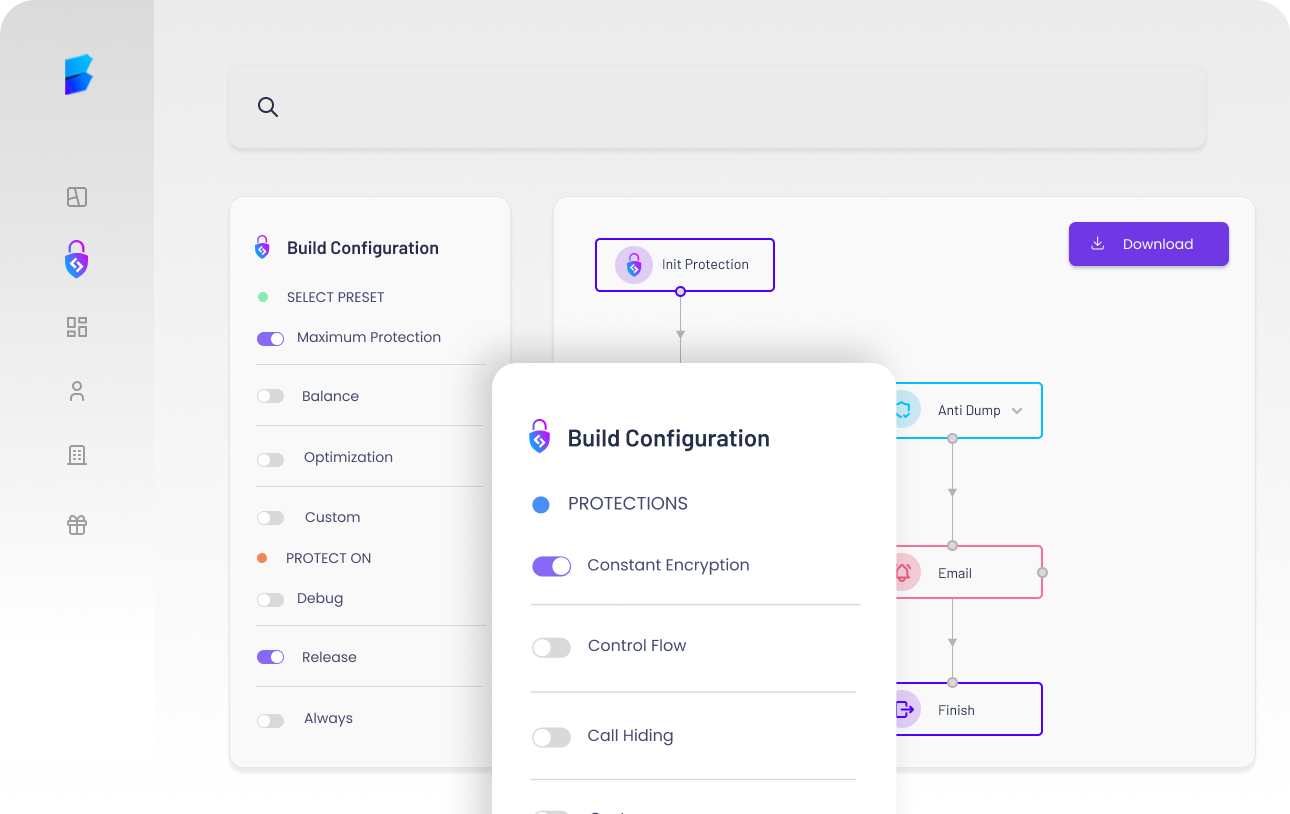
Constant Encryption Bytehide Enhance your application’s security with bytehide shield’s constant encryption. start safeguarding your constants today – efficient, effective, and essential for your application’s integrity!. Bytehide shield is the most advanced and up to date obfuscator, which will assist you in protecting your applications most efficiently. once you have shield in your system, you will never have to worry about the manipulation or theft of your data on the applications.

Bytehide Focus On Development And Forget About Security Encrypt constants, strings, and literals in applications using bytehide shield. protect sensitive data, api keys, and configuration values from static analysis. Bytehide shield is the most advanced and up to date obfuscator, which will assist you in protecting your applications most efficiently. once you have shield in your system, you will never have to worry about the manipulation or theft of your data on the applications. Advanced constant encryption is an enhanced protection feature in obfuscation that provides stronger encoding and compression for constants in your code. this protection offers an additional layer of security for sensitive constant values. Var key =" bytehide ";string password ="admin";console.writeline($"key: {key}, password: {password}");console.readkey();.

Bytehide Focus On Development And Forget About Security Advanced constant encryption is an enhanced protection feature in obfuscation that provides stronger encoding and compression for constants in your code. this protection offers an additional layer of security for sensitive constant values. Var key =" bytehide ";string password ="admin";console.writeline($"key: {key}, password: {password}");console.readkey();. Bytehide shield is the most advanced and up to date obfuscator, which will assist you in protecting your applications most efficiently. once you have shield in your system, you will never have to worry about the manipulation or theft of your data on the applications. It applies code obfuscation, string encryption, control flow flattening, and resource encryption to make reverse engineering as difficult as possible. it also includes basic runtime checks like anti debug and tamper detection built into the protected binary. Protect your applications with advanced obfuscation, anti debugging, and code encryption. secure your , javascript, android, and ios code against reverse engineering and tampering with 20 protection techniques. Server applications benefit from renaming, constant encryption, and control flow obfuscation. since the assemblies run on your own infrastructure, anti debugger protection is less critical but still useful for preventing analysis of on premise installations.

Bytehide Focus On Development And Forget About Security Bytehide shield is the most advanced and up to date obfuscator, which will assist you in protecting your applications most efficiently. once you have shield in your system, you will never have to worry about the manipulation or theft of your data on the applications. It applies code obfuscation, string encryption, control flow flattening, and resource encryption to make reverse engineering as difficult as possible. it also includes basic runtime checks like anti debug and tamper detection built into the protected binary. Protect your applications with advanced obfuscation, anti debugging, and code encryption. secure your , javascript, android, and ios code against reverse engineering and tampering with 20 protection techniques. Server applications benefit from renaming, constant encryption, and control flow obfuscation. since the assemblies run on your own infrastructure, anti debugger protection is less critical but still useful for preventing analysis of on premise installations.
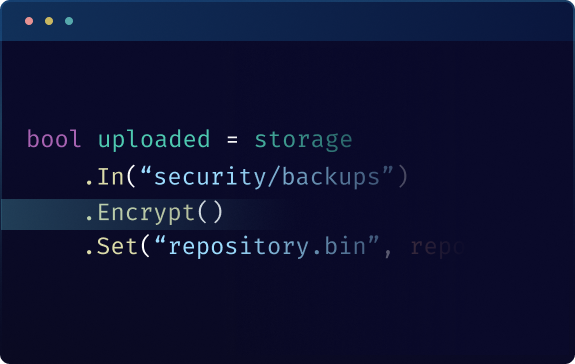
Bytehide Storage Try It Free Now Protect your applications with advanced obfuscation, anti debugging, and code encryption. secure your , javascript, android, and ios code against reverse engineering and tampering with 20 protection techniques. Server applications benefit from renaming, constant encryption, and control flow obfuscation. since the assemblies run on your own infrastructure, anti debugger protection is less critical but still useful for preventing analysis of on premise installations.
Comments are closed.