Computing And Information Technology Pdf Cloud Computing Malware
Navigating The Cloud A Comprehensive Study On Information Security In This systematic literature review aims to determine the latest information regarding cloud computing security, with a specific emphasis on threats and mitigation strategies. Despite all the benefits and potentials, cloud computing infrastructure is highly vulnerable to many security challenges, including malware. therefore, research towards detecting these malware as well as safeguarding the cloud architecture against malware attacks are increasing.

Premium Photo Cloud Computing And Malware Concept Identify and assess key cybersecurity threats in cloud computing. examine the unique challenges in cloud security. explore mitigation strategies and future security trends. The importance of user awareness and the impact of emerging technologies on cloud security have also been discussed in detail to mitigate security risks. a literature re view of previous research and scholarly articles has also been conducted to provide insights regarding cloud computing security. Abstract cloud computing remains a cornerstone of modern it infrastructure in 2025, yet it is plagued by persistent and evolving security issues. Review of virtualisation technologies: it reviews different types of virtualisation (computation, storage, network) and their role in cloud native design and deployment [7].
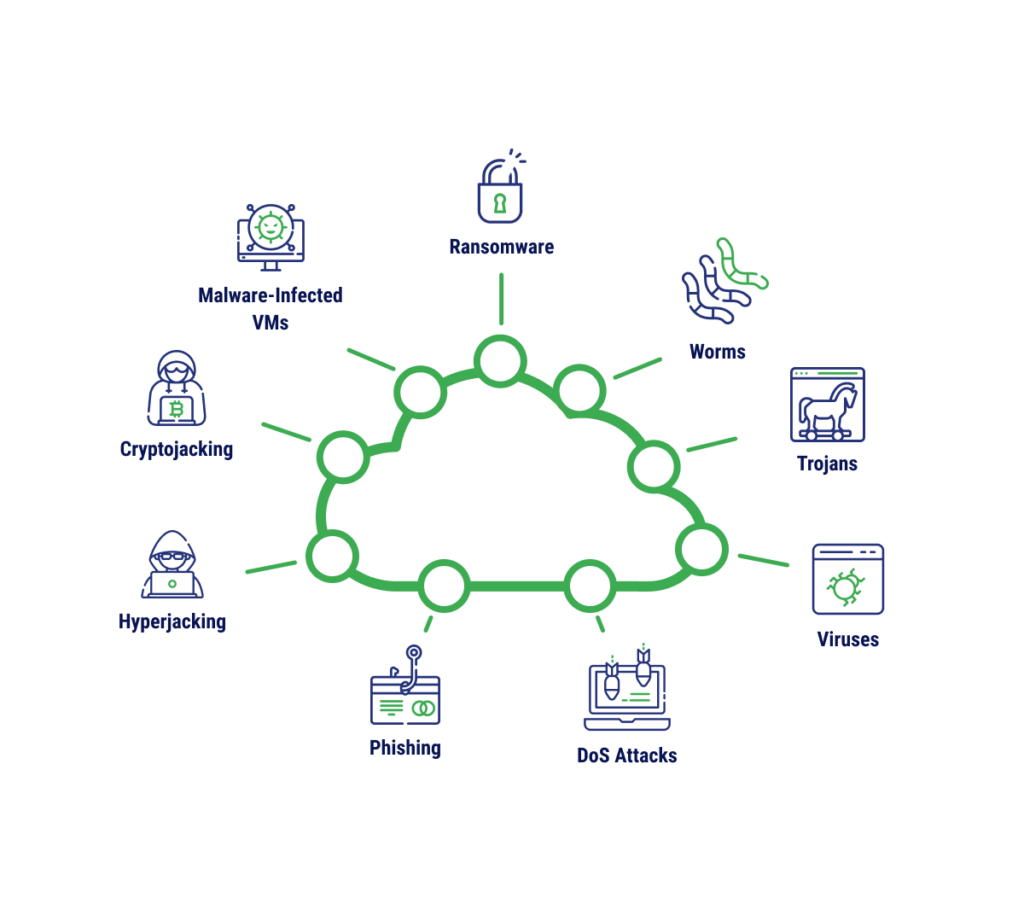
How To Protect Your Data From Cloud Malware Abstract cloud computing remains a cornerstone of modern it infrastructure in 2025, yet it is plagued by persistent and evolving security issues. Review of virtualisation technologies: it reviews different types of virtualisation (computation, storage, network) and their role in cloud native design and deployment [7]. Despite these advantages, cloud computing environments face numerous security challenges that threaten data confidentiality, system integrity, and service availability. this paper provides a comprehensive review of security threats associated with cloud computing systems by examining existing academic and industry literature. This research paper delves into the intricate domain of cloud computing security, emphasizing the need to address threats and mitigate risks associated with information storage and emerging technologies. This paper provides a detailed discussion on detecting malware in cloud environments and the advantages of cloud computing in safeguarding iot and cps from cyber attacks. Abstract – this paper is aimed to present information about the most current attacks on cloud computing, as well as security measures. due to its emergence a number of attacks can be performed over the cloud by the attackers or intruders.
Comments are closed.