Computer Security Pdf Cryptography Public Key Cryptography

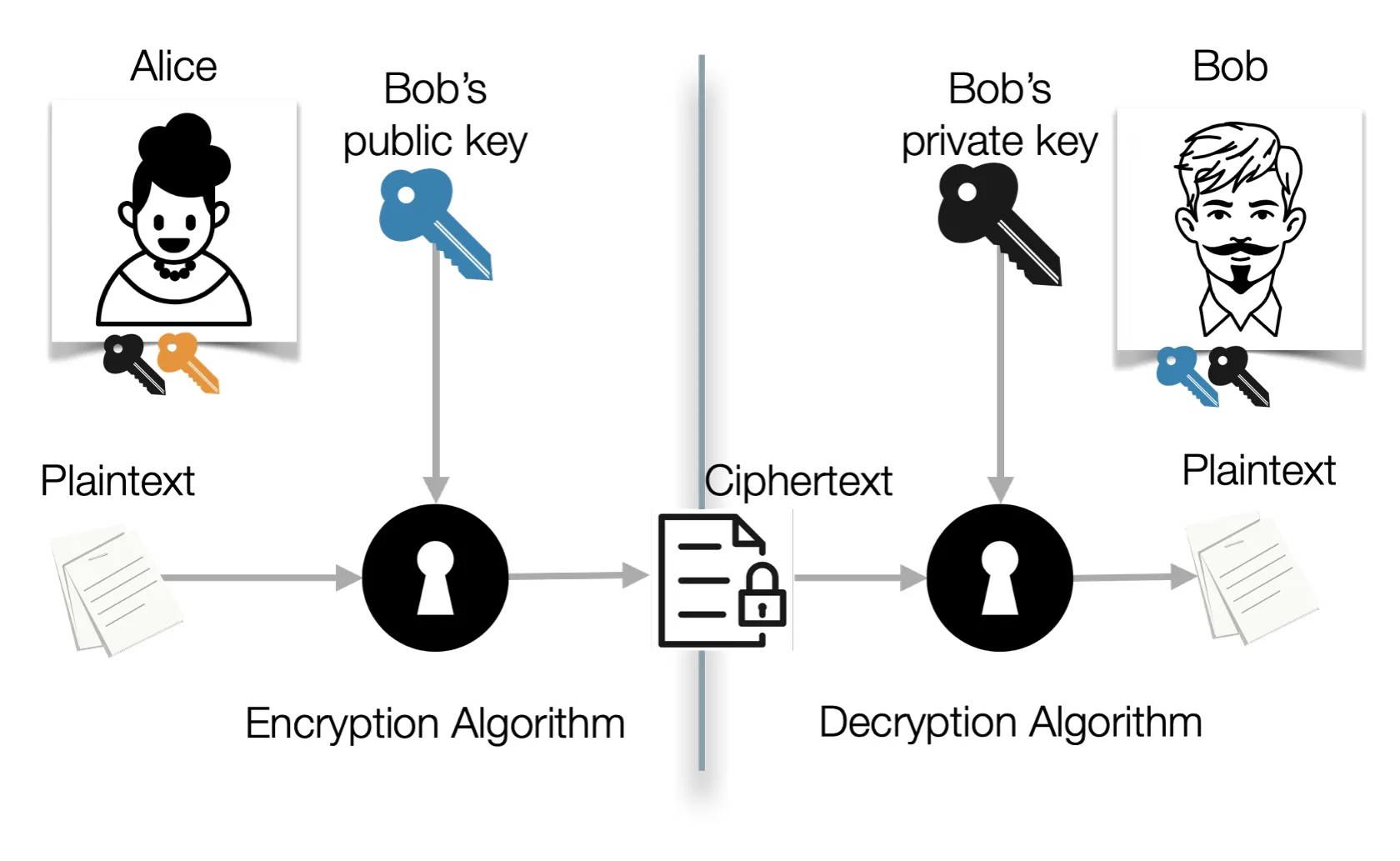
Public Key Cryptography Pdf Public Key Cryptography Key However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Digital signatures are based on public key techniques. signature generation ≡ decryption (uses private key), and signature verification ≡ encryption (uses public key).
Cs8792 Cryptography And Network Security Key Pdf Cryptography Elgamal encryption transforms diffie hellman key agreement into a public key encryption scheme by using the public secret information of the recipient as a long term key pair and the public secret information of the sender as a one time key pair. In this project we will introduce asymmetric key cryptography, and see why do we still use it. Reduce protection of information to protection of authenticity of public keys • no need to keep public keys secret, but must be sure that alice’s public key is really her true public key. Each receiver possesses a unique decryption key, generally referred to as his private key. receiver needs to publish an encryption key, referred to as his public key. some assurance of the authenticity of a public key is needed in this scheme to avoid spoofing by adversary as the receiver.
1 Introduction Network Security Cryptography Pdf Cryptography Reduce protection of information to protection of authenticity of public keys • no need to keep public keys secret, but must be sure that alice’s public key is really her true public key. Each receiver possesses a unique decryption key, generally referred to as his private key. receiver needs to publish an encryption key, referred to as his public key. some assurance of the authenticity of a public key is needed in this scheme to avoid spoofing by adversary as the receiver. Public key encryption means the algorithm has two keys: one public and one private. in this section, we explore public key encryption and the rsa encryption algorithm, named after the algorithm's inventors ron rivest, adi shamir, and len adleman. With our collection of free pdf books, you can delve into the principles of codes and hashes, learn about public and symmetric key cryptography, and discover innovative techniques used in cybersecurity. Rsa (rivest, shamir and adleman who first publicly described it in 1977) is an algorithm for public key cryptography. it is the first algorithm known to be suitable for signing as well as encryption, and one of the first great advances in public key cryptography. Lecture 23: network security public key cryptography comp 411, fall 2022 victoria manfredi.

Computer Security Pdf Cryptography Public Key Cryptography Public key encryption means the algorithm has two keys: one public and one private. in this section, we explore public key encryption and the rsa encryption algorithm, named after the algorithm's inventors ron rivest, adi shamir, and len adleman. With our collection of free pdf books, you can delve into the principles of codes and hashes, learn about public and symmetric key cryptography, and discover innovative techniques used in cybersecurity. Rsa (rivest, shamir and adleman who first publicly described it in 1977) is an algorithm for public key cryptography. it is the first algorithm known to be suitable for signing as well as encryption, and one of the first great advances in public key cryptography. Lecture 23: network security public key cryptography comp 411, fall 2022 victoria manfredi.
Cs 465 Introduction To Security And Privacy Rsa (rivest, shamir and adleman who first publicly described it in 1977) is an algorithm for public key cryptography. it is the first algorithm known to be suitable for signing as well as encryption, and one of the first great advances in public key cryptography. Lecture 23: network security public key cryptography comp 411, fall 2022 victoria manfredi.
Comments are closed.