Computer Security Incident Handling Optimizing Cybersecurity Framework Road

Computer Security Incident Handling Optimizing Cybersecurity Framework Road This publication seeks to assist organizations with incorporating cybersecurity incident response recommendations and considerations throughout their cybersecurity risk management activities as described by the nist cybersecurity framework (csf) 2.0. This publication seeks to assist organizations with incorporating cybersecurity incident response recommendations and considerations throughout their cybersecurity risk management activities, as described by csf 2.0.
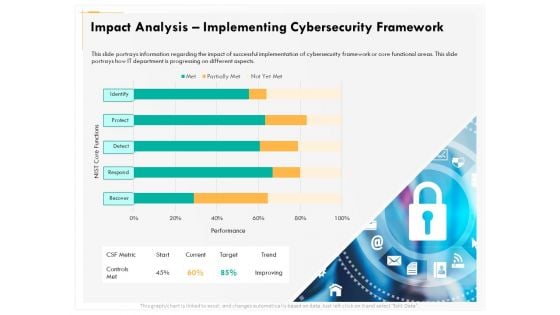
Computer Security Incident Handling Impact Analysis Implementing This cybersecurity incident management guide provides a structured approach to preparing for, responding to, and recovering from security incidents. it offers practical frameworks, actionable recommendations, and implementation guidance based on industry best practices and real world experience. The topics discussed in these slides are implement enterprise security program, implement control environment, implement security processes. this is a completely editable powerpoint presentation and is available for immediate download. This guide is a practical, actionable blueprint for building a complete incident response framework for 2025, covering the latest methodologies, the critical role of digital forensics, and the game changing impact of artificial intelligence. clarity in terminology is essential. Learn how to build and optimize an incident management framework to reduce risk, improve response, and boost cybersecurity resilience.
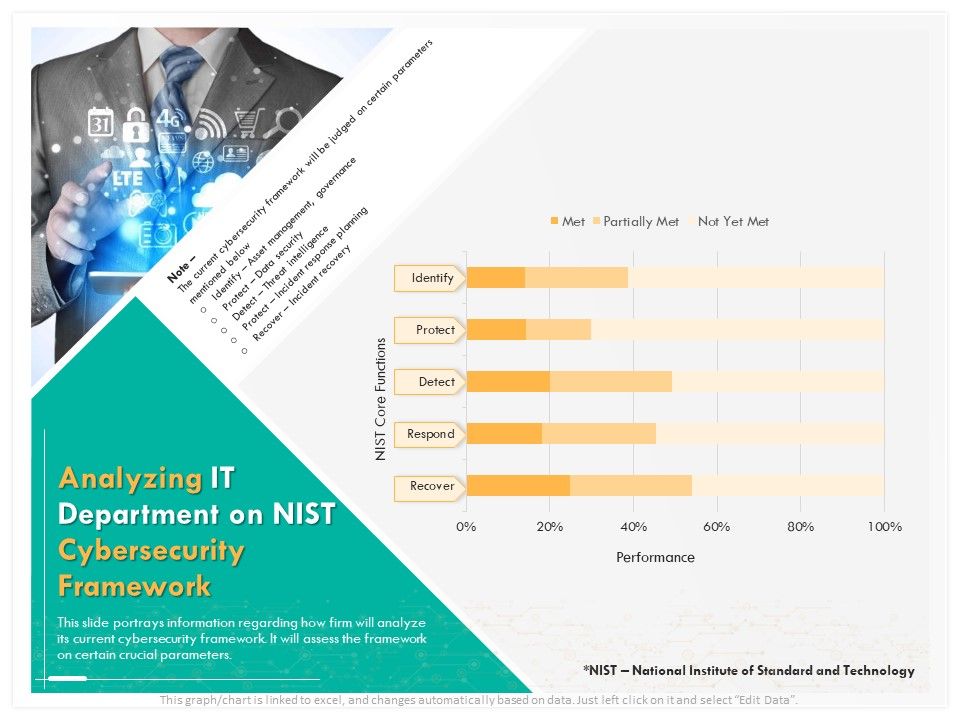
Computer Security Incident Handling Analyzing It Department On Nist This guide is a practical, actionable blueprint for building a complete incident response framework for 2025, covering the latest methodologies, the critical role of digital forensics, and the game changing impact of artificial intelligence. clarity in terminology is essential. Learn how to build and optimize an incident management framework to reduce risk, improve response, and boost cybersecurity resilience. These playbooks provide fceb agencies with a standard set of procedures to identify, coordinate, remediate, recover, and track successful mitigations from incidents and vulnerabilities affecting fceb systems, data, and networks. The nist computer security incident handling guide provides in depth guidelines on how to build an incident response capability within an organization. it covers several models for incident response teams, how to select the best model, and best practices for operating the team. Effective incident detection and handling ensures data security, operational continuity, and regulatory compliance. this guide explores best practices, frameworks, and tools for building robust cybersecurity operations. Gcih certification holders have the knowledge needed to manage security incidents by understanding common attack techniques, vectors and tools, as well as defend against and respond to such attacks when they occur.

Computer Security Incident Handling Cybersecurity Maintenance Checklist Bac These playbooks provide fceb agencies with a standard set of procedures to identify, coordinate, remediate, recover, and track successful mitigations from incidents and vulnerabilities affecting fceb systems, data, and networks. The nist computer security incident handling guide provides in depth guidelines on how to build an incident response capability within an organization. it covers several models for incident response teams, how to select the best model, and best practices for operating the team. Effective incident detection and handling ensures data security, operational continuity, and regulatory compliance. this guide explores best practices, frameworks, and tools for building robust cybersecurity operations. Gcih certification holders have the knowledge needed to manage security incidents by understanding common attack techniques, vectors and tools, as well as defend against and respond to such attacks when they occur.
Comments are closed.