Computer Security Incident Handling Impact Analysis Implementing

Computer Security Incident Handling Guide Pdf Incident Management This publication seeks to assist organizations with incorporating cybersecurity incident response recommendations and considerations throughout their cybersecurity risk management activities as described by the nist cybersecurity framework (csf) 2.0. Incident management is the process of handling a security breach or attack, from its detection to its resolution. it involves identifying, analyzing, responding to, and recovering from incidents in a manner that minimizes impact on the organization’s operations, data, and reputation.
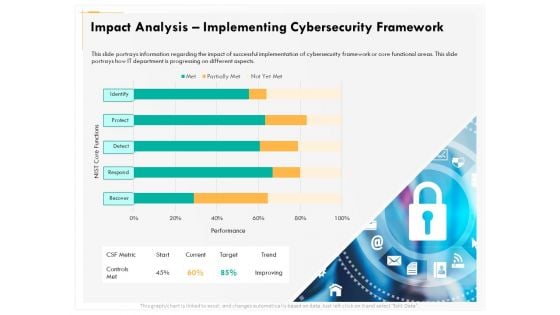
Computer Security Incident Handling Impact Analysis Implementing Learn how to build a strong cybersecurity incident response plan to detect, contain, and recover from cyber threats while ensuring compliance and resilience. An effective incident response plan provides a structured framework for managing cybersecurity incidents, enabling organizations to respond consistently and efficiently when security events occur. Learn about the nist incident response lifecycle and its key steps and phases. detect, contain, recover, and mitigate cyber incidents fast. In this post, we’ll explore the key concepts, processes, and best practices outlined in nist sp 800 61 to help organizations in their incident response efforts.

Computer Security Incident Handling Impact Analysis Effective Security Learn about the nist incident response lifecycle and its key steps and phases. detect, contain, recover, and mitigate cyber incidents fast. In this post, we’ll explore the key concepts, processes, and best practices outlined in nist sp 800 61 to help organizations in their incident response efforts. This publication assists organizations in establishing computer security incident response capabilities and handling incidents efficiently and effectively. this revision of the publication, revision 2, updates material throughout the publication to reflect the changes in threats and incidents. As cyber attacks evolve in sophistication; organizations are under constant threat. this necessitates a cohesive approach to prioritize incident response (ir) capabilities and mitigate potential. Discover the key steps and best practices for effective cyber security incident management. learn how to respond to breaches and reduce costs. A robust security incident handling process is crucial to minimize the impact of these incidents, protect sensitive data, and ensure business continuity. this guide provides a comprehensive framework for effectively responding to computer security incidents.
Comments are closed.