Computer Security Cryptography Ch01 Pdf

Cryptography And Data Security Lecture 1 Pdf Pdf Cryptography 1.2. what is security? \a secure channel over which a message can be transmitted such that no one can eaves drop" security involves storage, not just communication. This document discusses computer security and network cryptography. it begins by explaining how organizations can use cryptosystems like symmetric and asymmetric encryption to protect data.
Zch1 Introduction To Cryptography Pdf Cryptography and network security chapter 1 acknowledgments lecture slides are based on the slides created by lawrie brown. Chapter 1 an overview of computer security discharge. — the tempest, ii, i r security. the remainder of this book will elaborate on these concepts in order to reveal the logic underlying the principles of the the system. the next section discusses security policies that identify the threats and de ne the requirements for ensuring a se. E book at hand provides an introduction to cryptography. this is part of the broader area of cybersecurity, which deals wi h the protection of digital informa tion against misuse. even though cybersecurity is a complex field that encompasses technical aspects as well as organizational and human ones, almost all it security solut. “the combination of space, time, and strength that must be considered as the basic elements of this theory of defense makes this a fairly complicated matter. consequently, it is not easy to find a fixed point of departure.”.

Unit1 Cryptography And Cyber Security Pdf Encryption Cryptography E book at hand provides an introduction to cryptography. this is part of the broader area of cybersecurity, which deals wi h the protection of digital informa tion against misuse. even though cybersecurity is a complex field that encompasses technical aspects as well as organizational and human ones, almost all it security solut. “the combination of space, time, and strength that must be considered as the basic elements of this theory of defense makes this a fairly complicated matter. consequently, it is not easy to find a fixed point of departure.”. Many secret sharing schemes provided information theoretic security, in that any set of parties which is unqualified can obtain no information about the shared secret even if they have unbounded computing power. The document provides an introduction and roadmap to the topics of information security that will be covered, including cryptographic algorithms, mutual trust, network security, computer security, and standards organizations. If it’s provably secure, it probably isn’t. | lars knudsen the whole notion of provable security (in cryptography) must be taken with a grain of salt in practice, a (theoretically and or provably secure) cryptosystem must be implemented in one way or another. Pdf | it introduces an introduction to cryptography. | find, read and cite all the research you need on researchgate.
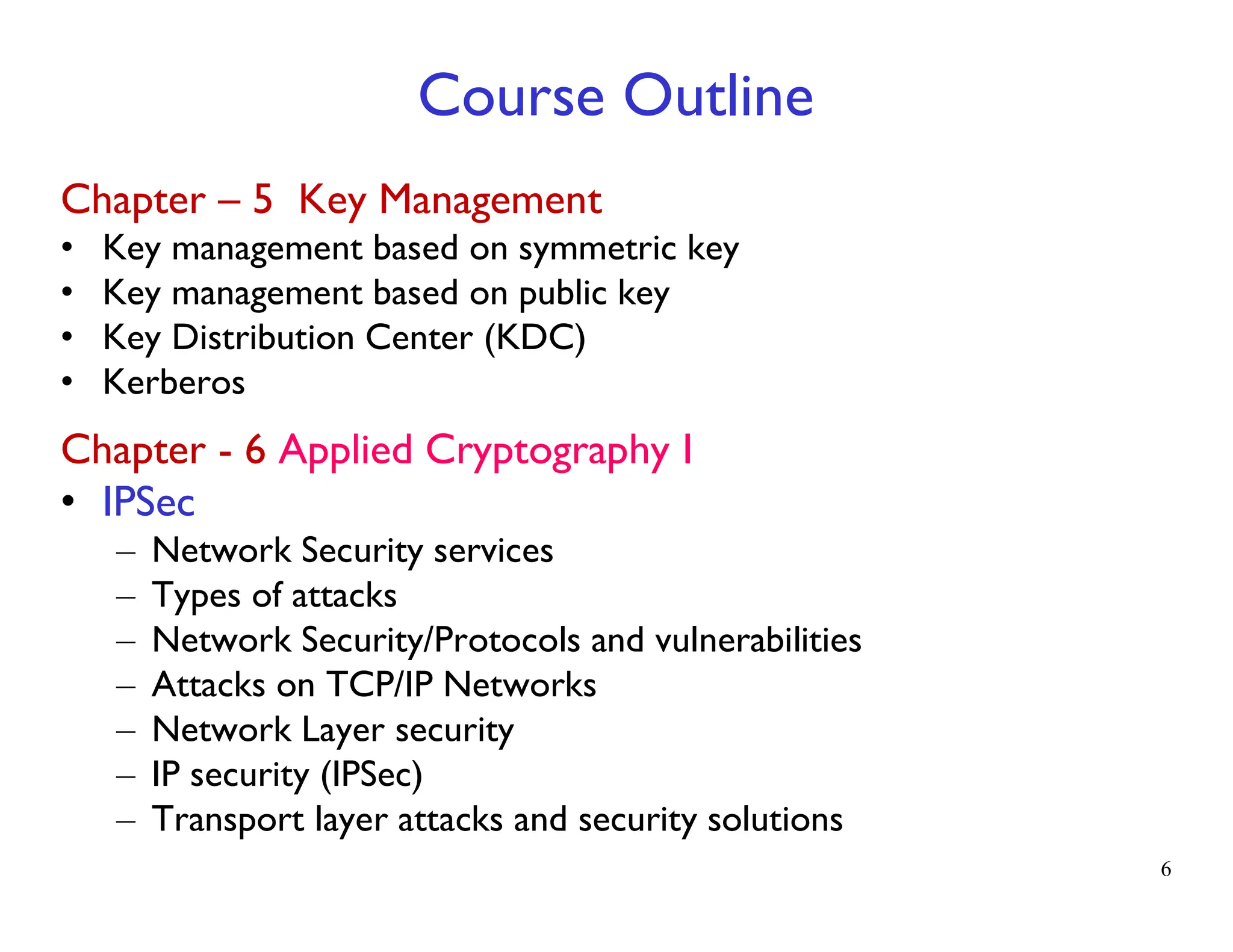
Chapter 1 Fundamentals Of Cryptography Pdf Many secret sharing schemes provided information theoretic security, in that any set of parties which is unqualified can obtain no information about the shared secret even if they have unbounded computing power. The document provides an introduction and roadmap to the topics of information security that will be covered, including cryptographic algorithms, mutual trust, network security, computer security, and standards organizations. If it’s provably secure, it probably isn’t. | lars knudsen the whole notion of provable security (in cryptography) must be taken with a grain of salt in practice, a (theoretically and or provably secure) cryptosystem must be implemented in one way or another. Pdf | it introduces an introduction to cryptography. | find, read and cite all the research you need on researchgate.

Cyber Security Cryptography Unit 1 Pdf Cybercrime Malware If it’s provably secure, it probably isn’t. | lars knudsen the whole notion of provable security (in cryptography) must be taken with a grain of salt in practice, a (theoretically and or provably secure) cryptosystem must be implemented in one way or another. Pdf | it introduces an introduction to cryptography. | find, read and cite all the research you need on researchgate.
Comments are closed.