Computer Information Security Encryption And Decryption Using 33 Hill Cipher
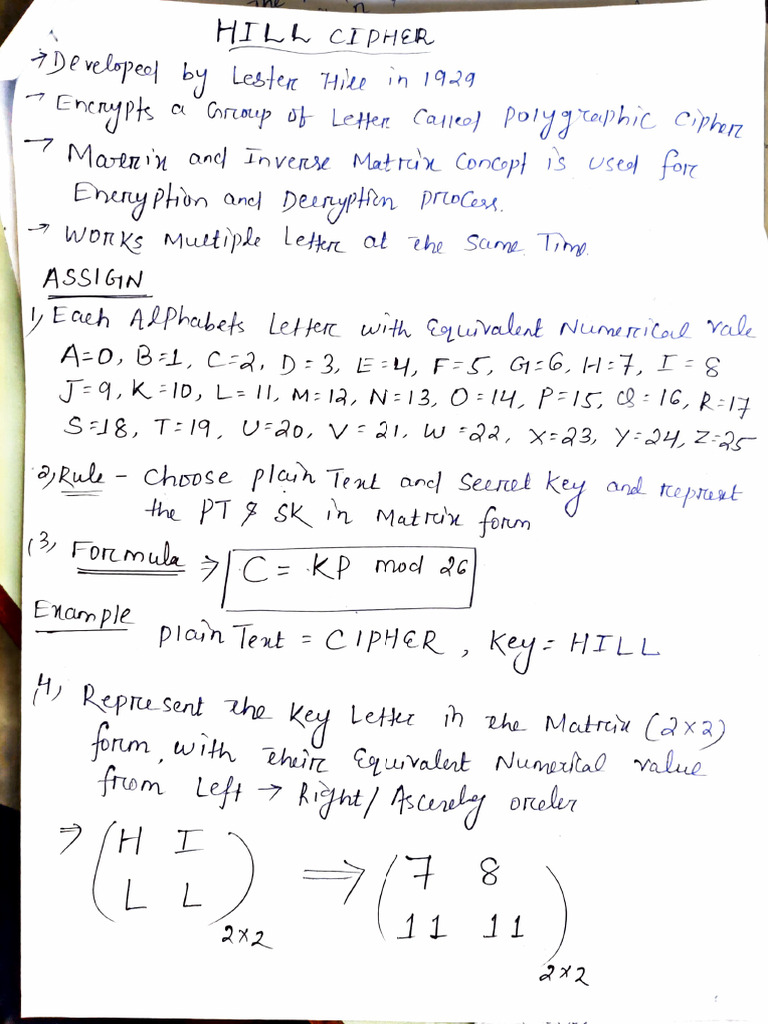
Hill Cipher Encryption Technique Pdf Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25. Hill cipher is a polyalphabetic cipher created by extending the affine cipher, using linear algebra and modular arithmetic via a numeric matrix that serves as an encryption and decryption key.
Decryption Hill Cipher Flexibility − messages with capital and lowercase letters, punctuation, and spaces can be encrypted and decrypted using the hill cipher. because of its adaptability, it can be used to encrypt a variety of text based files. In the examples given, we shall walk through all the steps to use this cipher to act on digraphs and trigraphs. it can be extended further, but this then requires a much deeper knowledge of the background mathematics. The document discusses the hill cipher, a multi letter encryption technique developed by lester hill in 1929, which uses matrix multiplication for encryption and decryption. With this, it is possible to encrypt three plain text letters at a time. now, let us look at an example on how to encrypt and decrypt using hill cipher algorithm.

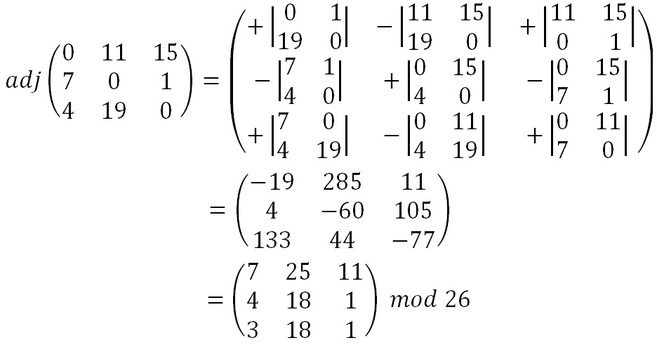
Solution Hill Cipher Hill Cipher Encryption And Decryption Des Data The document discusses the hill cipher, a multi letter encryption technique developed by lester hill in 1929, which uses matrix multiplication for encryption and decryption. With this, it is possible to encrypt three plain text letters at a time. now, let us look at an example on how to encrypt and decrypt using hill cipher algorithm. Select "3x3" as the matrix size, enter your key matrix and ciphertext, and click decrypt. the tool computes the 3x3 inverse matrix automatically using cofactor expansion and the adjugate method, then applies it to each 3 character block. Free online hill cipher encoder and decoder tool. encrypt and decrypt text using this matrix based cipher with customizable key matrices and interactive visualization. Hill cipher uses linear algebra to encrypt and decrypt messages, which creates a layer of security through diffusion. however, it can fall prey to a known plaintext attack. Developed in 1929 by the renowned american mathematician lester s. hill, the hill cipher is a popularly used method of encryption and decryption of text and images, built on the principles of linear algebra.

Pdf Color Image Encryption And Decryption Using Hill Cipher Image Select "3x3" as the matrix size, enter your key matrix and ciphertext, and click decrypt. the tool computes the 3x3 inverse matrix automatically using cofactor expansion and the adjugate method, then applies it to each 3 character block. Free online hill cipher encoder and decoder tool. encrypt and decrypt text using this matrix based cipher with customizable key matrices and interactive visualization. Hill cipher uses linear algebra to encrypt and decrypt messages, which creates a layer of security through diffusion. however, it can fall prey to a known plaintext attack. Developed in 1929 by the renowned american mathematician lester s. hill, the hill cipher is a popularly used method of encryption and decryption of text and images, built on the principles of linear algebra.

Hill Cipher Decryption Code Download Scientific Diagram Hill cipher uses linear algebra to encrypt and decrypt messages, which creates a layer of security through diffusion. however, it can fall prey to a known plaintext attack. Developed in 1929 by the renowned american mathematician lester s. hill, the hill cipher is a popularly used method of encryption and decryption of text and images, built on the principles of linear algebra.

Problem 1 0 25 Points In Hill Cipher Encryption Method User Is Usi Pdf
Comments are closed.