Computer And Network Security Notes Pdf Cryptography Espionage
Cryptography And Network Security Notes Pdf This document provides information for instructors using lecture notes on computer and network security authored by avinash kak. it explains that the notes are intended to be used both as slides during lectures and for independent student reading. Think of these lecture notes as a living textbook that strives to strike a balance between the systems oriented issues and the cryptographic issues. without the latter, many aspects of the former cannot be fully comprehended, and, without the former, the latter are too dry to appreciate.
Cryptography And Network Security Introduction Autosaved Pdf Internet security measures to protect data during their transmission over a collection of interconnected networks our focus is on internet security which consists of measures to deter, prevent, detect and correct security violations that involve the transmission and storage of information. Cryptography can reformat and transform our data, making it safer on its trip between computers. the technology is based on the essentials of secret codes, augmented by modern mathematics that protects our data in powerful ways. Introduction: this is the age of universal electronic connectivity, where the activities like hacking, viruses, electronic fraud are very common. unless security measures are taken, a network conversation or a distributed application can be compromised easily. This definition introduces three key objectives that are at the heart of computer security.

Cryptography And Network Security Notes Btech Papers Introduction: this is the age of universal electronic connectivity, where the activities like hacking, viruses, electronic fraud are very common. unless security measures are taken, a network conversation or a distributed application can be compromised easily. This definition introduces three key objectives that are at the heart of computer security. Mrcet. Computer security generic name for the collection of tools designed to protect data and to prevent hackers. network security measures to protect data during their transmission. internet security measures to protect data during their transmission over a collection of interconnected networks. This repository contains notes required by cse it students for ip university. they are managed in respective folders along with some relevant pdfs also. ipu engineering notes it 7th sem cns handwritten complete cryptography and network security.pdf at master · coderjolly ipu engineering notes. Loading….
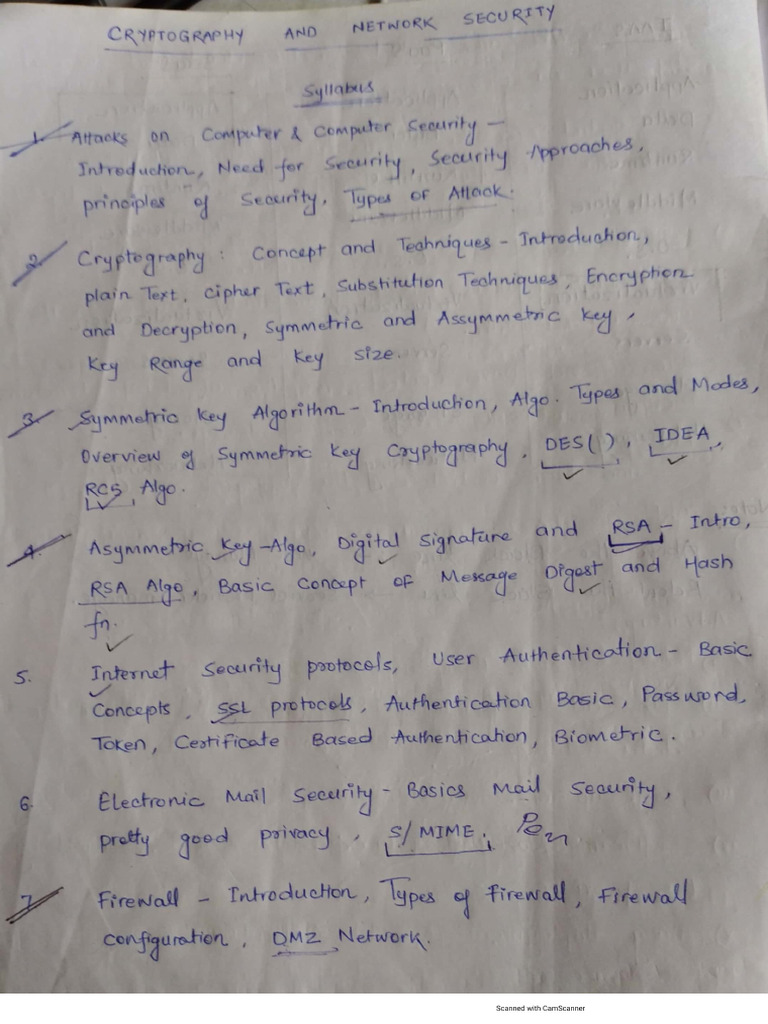
Cryptography And Network Security Notes Pdf Mrcet. Computer security generic name for the collection of tools designed to protect data and to prevent hackers. network security measures to protect data during their transmission. internet security measures to protect data during their transmission over a collection of interconnected networks. This repository contains notes required by cse it students for ip university. they are managed in respective folders along with some relevant pdfs also. ipu engineering notes it 7th sem cns handwritten complete cryptography and network security.pdf at master · coderjolly ipu engineering notes. Loading….

Computer Network And Security Notes Pdf Computer Network Network This repository contains notes required by cse it students for ip university. they are managed in respective folders along with some relevant pdfs also. ipu engineering notes it 7th sem cns handwritten complete cryptography and network security.pdf at master · coderjolly ipu engineering notes. Loading….
Comments are closed.