Comparison Of 3g 4g And 5g Security Mechanisms

5g Security Pdf Electronics Computer Science This report provides an exhaustive, chronologically structured analysis of the security vulnerabilities and attacks discovered in each cellular generation, from 2g through 5g, and details how these flaws were addressed by specific security controls and architectural changes in their successors. Objective: the objective of this research is to evaluate and contrast the cybersecurity efficacy of 4g lte and 5g networks, with specific emphasis on data encryption, susceptibility to.

5g Security Explained 3gpp 5g Core Network Sba And Security Mechanisms When i first worked on a 5gc deployment, i realized how the attack surfaces and security posture had shifted dramatically compared to 4g. let me break it down for you. In addition, we provide a taxonomy and comparison of authentication and privacy preserving schemes for 4g and 5g cellular networks in form of tables. based on the current survey, several recommendations for further research are discussed at the end of this paper. Compare 5g vs. 4g to find out how the two generations of cellular technology differ around speed, latency and other features. The main outputs of this survey paper provide insights into the hot topic of security threats and countermeasures at the phy layer in 4g 5g cellular networks. this allows researcher and industry experts to identify key threats such as jamming, eavesdropping, spoofing, and more.
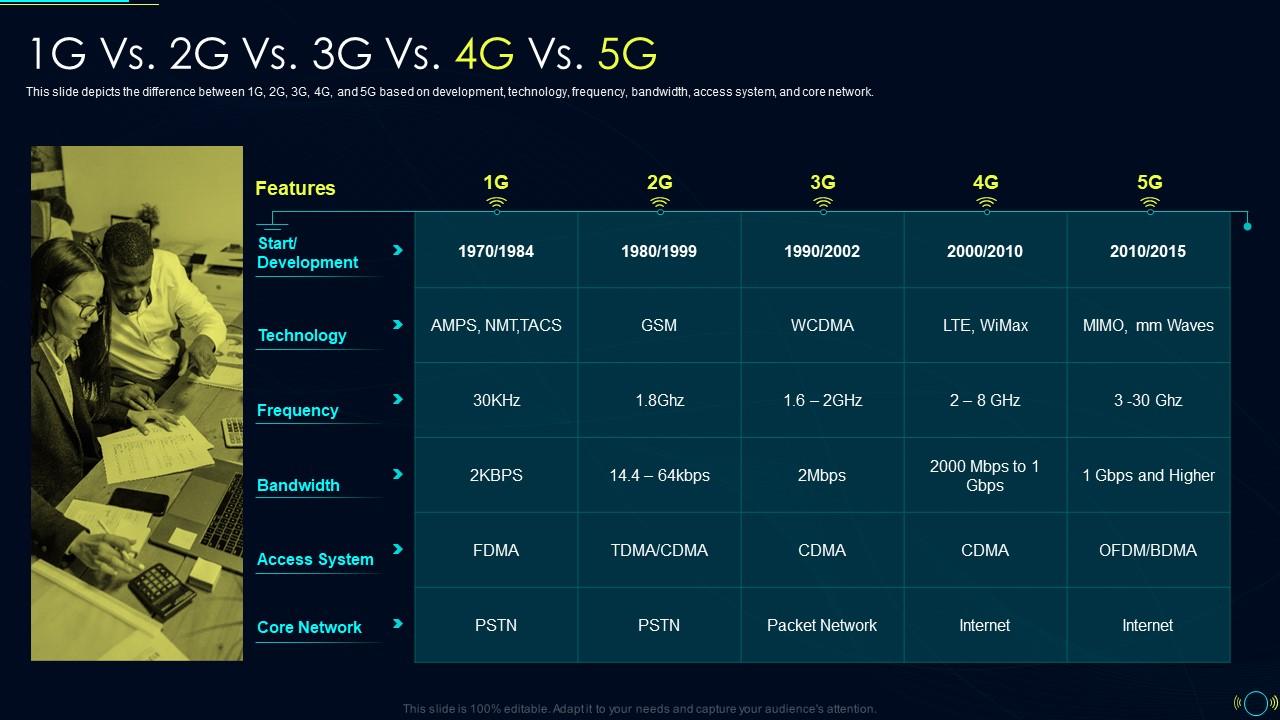
Comparison Between 4g And 5g Based On Features And 47 Off Compare 5g vs. 4g to find out how the two generations of cellular technology differ around speed, latency and other features. The main outputs of this survey paper provide insights into the hot topic of security threats and countermeasures at the phy layer in 4g 5g cellular networks. this allows researcher and industry experts to identify key threats such as jamming, eavesdropping, spoofing, and more. 3gpp’s 5g system standards provide security mechanisms, which are based on well proven 4g security mechanisms, but also include new enhancements for e.g. encryption, authentication, and user privacy. This paper takes a two step comparative approach to analyze the factors that influence users’ adoption of fourth generation (4g) and 5g services. we chose highly cited articles that discuss how users accept and adopt 4g and 5g technology services. This work focuses on 5g security issues and highlighting the challenges and proposed solutions, standards, and analysis, in addition to the architecture of 5g network and authentication process of both 4g and 5g. Unlike 4g, which is hardware based and centrally managed, 5g relies on virtualization, software defined components, and distributed infrastructure. this shift increases flexibility but also broadens the attack surface.
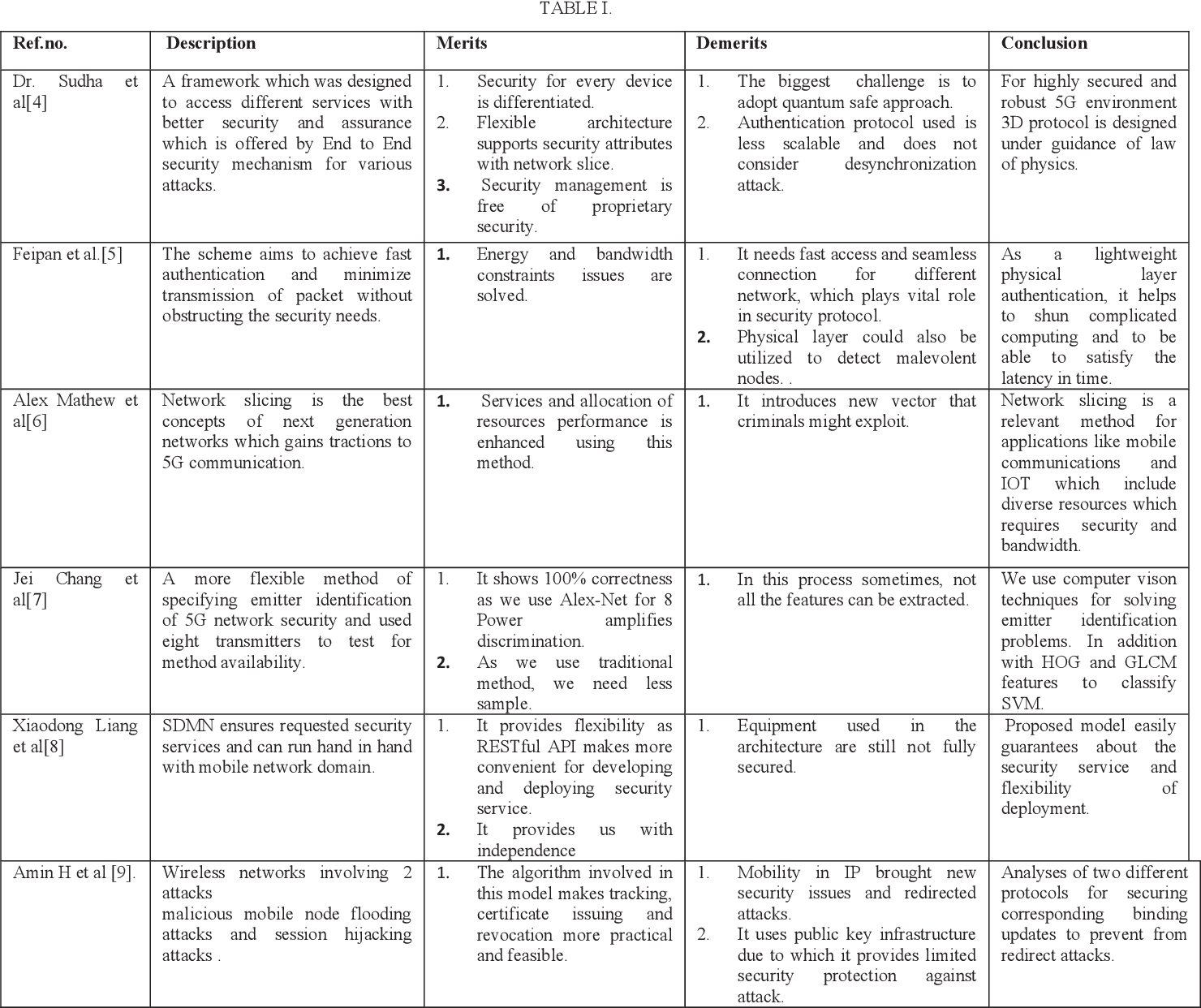
Table I From Comparative Analysis Of 5g Security Mechanisms Semantic 3gpp’s 5g system standards provide security mechanisms, which are based on well proven 4g security mechanisms, but also include new enhancements for e.g. encryption, authentication, and user privacy. This paper takes a two step comparative approach to analyze the factors that influence users’ adoption of fourth generation (4g) and 5g services. we chose highly cited articles that discuss how users accept and adopt 4g and 5g technology services. This work focuses on 5g security issues and highlighting the challenges and proposed solutions, standards, and analysis, in addition to the architecture of 5g network and authentication process of both 4g and 5g. Unlike 4g, which is hardware based and centrally managed, 5g relies on virtualization, software defined components, and distributed infrastructure. this shift increases flexibility but also broadens the attack surface.

Key Points Of 5g Security Cybersecurity Magazine This work focuses on 5g security issues and highlighting the challenges and proposed solutions, standards, and analysis, in addition to the architecture of 5g network and authentication process of both 4g and 5g. Unlike 4g, which is hardware based and centrally managed, 5g relies on virtualization, software defined components, and distributed infrastructure. this shift increases flexibility but also broadens the attack surface.
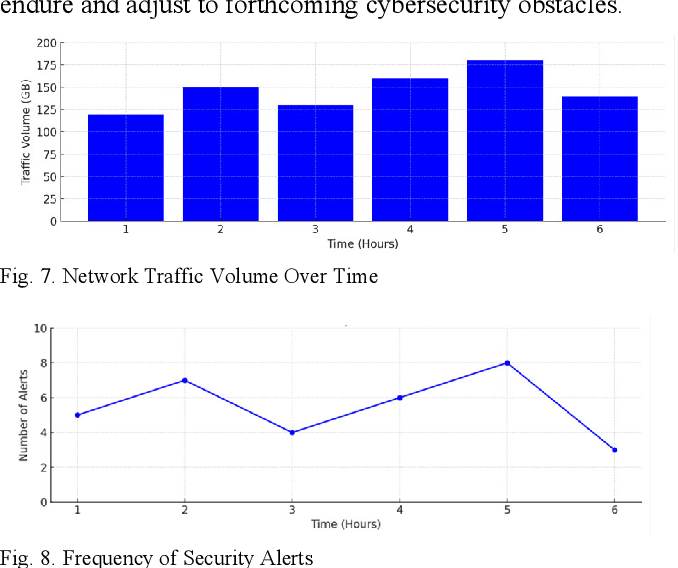
Figure 7 From A Comparison Of 4g Lte And 5g Network Cybersecurity
Comments are closed.