Company User Permissions
User Permissions Designs Themes Templates And Downloadable Graphic User permissions, part of the overall user management process, are the authorization that allows users to access specific resources on a network, such as applications, data files, printers, and scanners. they can also indicate the type of access, such as read only or read write. Over time, users' roles within an organization can change, and permissions that were once necessary may no longer be needed. conducting regular audits helps identify these discrepancies and mitigate security risks.
User Permissions Understand user roles & permissions, the foundation of security. learn about rbac, rebac, and see real world examples to implement effective control. For accessing and completing tasks users require specific roles and permissions. review the different available roles, permissions, and the associated tasks that users can complete with the roles and permissions. A "role" is nothing more than a collection of permissions. read this post for a closer look at user roles and permissions and some examples of each. In this article, we’ll explore five best practices for managing user permissions in it projects, helping you strike the perfect balance between security and efficiency. by implementing these strategies, you can safeguard your organization’s sensitive information while enabling seamless collaboration among team members. 1.
.png)
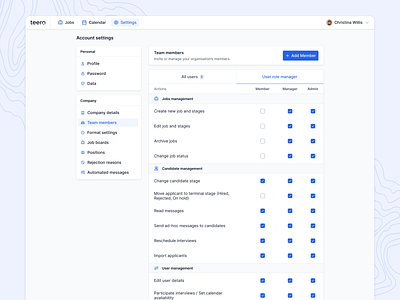
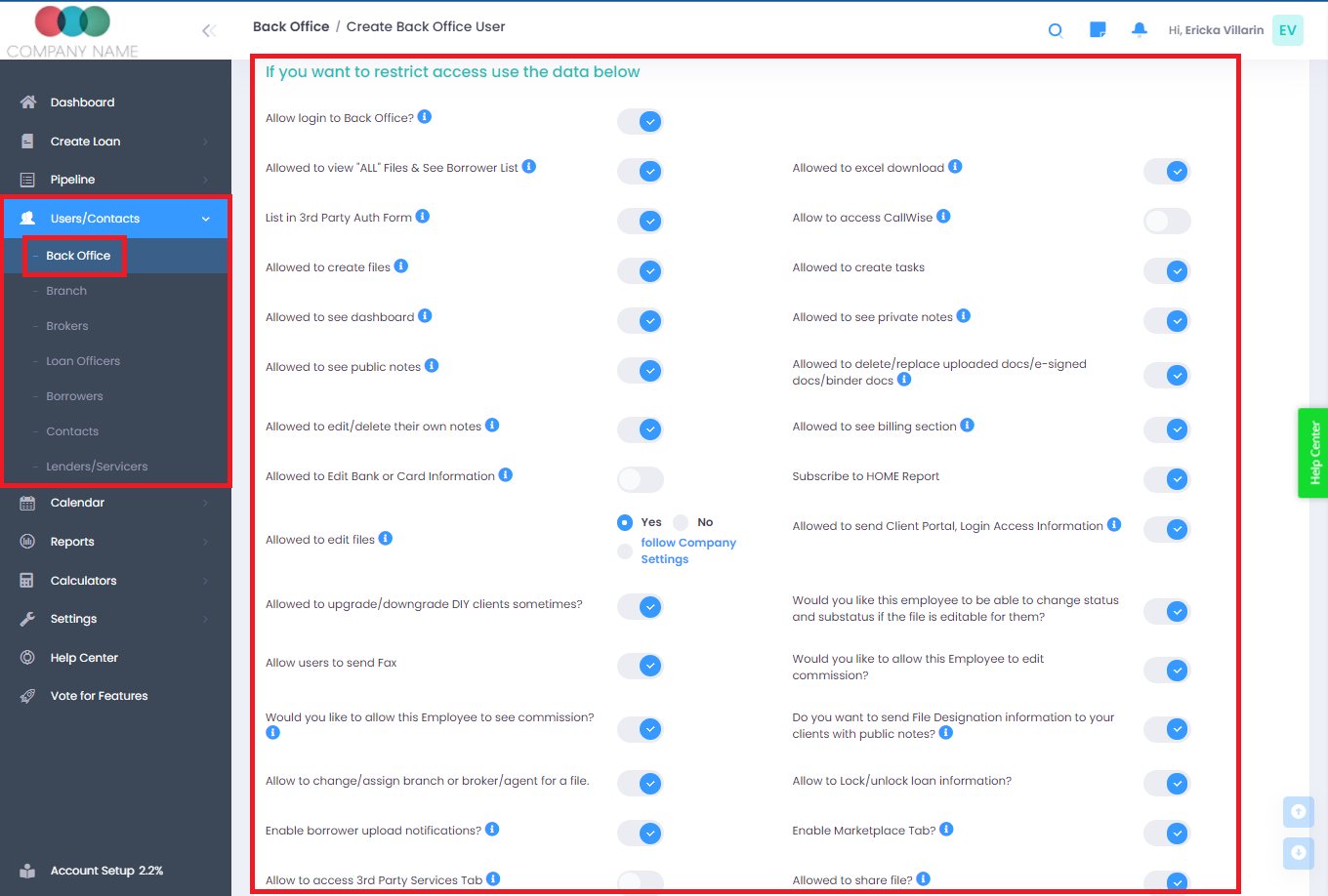
Configure User Permissions A "role" is nothing more than a collection of permissions. read this post for a closer look at user roles and permissions and some examples of each. In this article, we’ll explore five best practices for managing user permissions in it projects, helping you strike the perfect balance between security and efficiency. by implementing these strategies, you can safeguard your organization’s sensitive information while enabling seamless collaboration among team members. 1. The design and implementation of user roles, profiles, and permissions are not one time tasks. just as your business is not static, your user management strategies should be constantly evolving to meet the changing needs and challenges of your organization. A common challenge for many businesses is efficiently managing user permissions as new solutions are deployed and adopted. how do you ensure that the right people have the right permissions to access the data they need for their jobs?. Access & manage the company administration settings page where they can see locations, departments, user management, approvals, and more. company admins assigned to multiple companies (i.e., sister companies) are called multi company admins. User roles and permissions are crucial for maintaining secure access control within an application. by assigning specific privileges to each user based on their role or function in the organization, you can limit unauthorized access to sensitive data or restricted areas.

Manage User Permissions The design and implementation of user roles, profiles, and permissions are not one time tasks. just as your business is not static, your user management strategies should be constantly evolving to meet the changing needs and challenges of your organization. A common challenge for many businesses is efficiently managing user permissions as new solutions are deployed and adopted. how do you ensure that the right people have the right permissions to access the data they need for their jobs?. Access & manage the company administration settings page where they can see locations, departments, user management, approvals, and more. company admins assigned to multiple companies (i.e., sister companies) are called multi company admins. User roles and permissions are crucial for maintaining secure access control within an application. by assigning specific privileges to each user based on their role or function in the organization, you can limit unauthorized access to sensitive data or restricted areas.
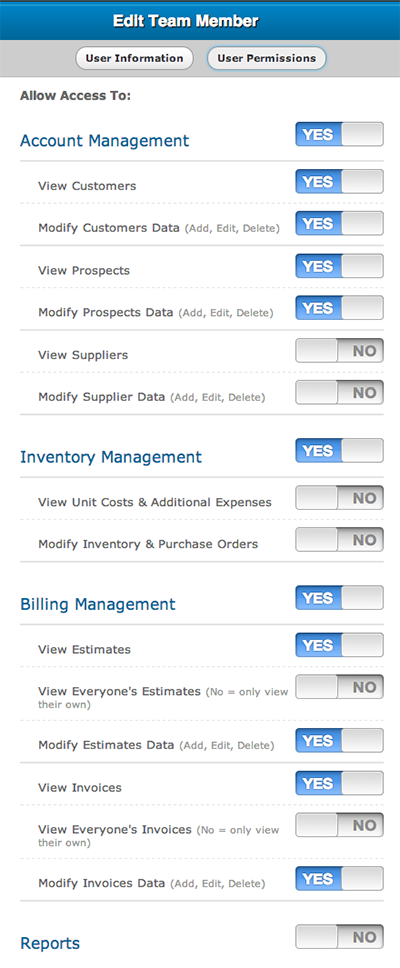
Custom User Permissions For Viewing Modifying And Collaborating Access & manage the company administration settings page where they can see locations, departments, user management, approvals, and more. company admins assigned to multiple companies (i.e., sister companies) are called multi company admins. User roles and permissions are crucial for maintaining secure access control within an application. by assigning specific privileges to each user based on their role or function in the organization, you can limit unauthorized access to sensitive data or restricted areas.

Empowering Internal Comms Across Your Entire Team With User Permissions
Comments are closed.