Common Linux Privilege Escalation Using Kernel Exploits
How To Conduct Linux Privilege Escalations Techtarget By understanding common techniques—such as kernel exploits, misconfigured services, suid misuse, sudo misconfigurations, and cron job vulnerabilities—you can better secure systems against these threats. Explore how attackers escalate privileges on linux using kernel exploits, suid binaries, sudo misconfigurations, path manipulation, cronjobs, and nfs weaknesses techniques and practical examples.

Linux Privilege Escalation Kernel Exploits Steflan S Security Blog Linux security & privilege escalation relevant source files this section documents the methodologies, vectors, and technical implementations for assessing linux security and achieving privilege escalation. it covers system enumeration, kernel exploitation, service specific vulnerabilities (grafana, logstash, ipsec), and post exploitation. Common methods for vertical privilege escalation include exploiting software or kernel vulnerabilities, misconfiguring sudo permissions, and abusing setuid setgid binaries. understanding these techniques is crucial for securing systems against potential threats. The room provides a deep dive into eight core privilege escalation techniques, while also covering essential linux fundamentals that support the enumeration and exploitation process. Sudo versions before 1.9.17p1 (1.9.14 1.9.17 < 1.9.17p1) allows unprivileged local users to escalate their privileges to root via sudo chroot option when etc nsswitch.conf file is used from a user controlled directory. here is a poc to exploit that vulnerability.

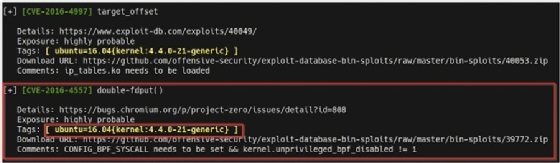
Linux Privilege Escalation Kernel Exploits Steflan S Security Blog The room provides a deep dive into eight core privilege escalation techniques, while also covering essential linux fundamentals that support the enumeration and exploitation process. Sudo versions before 1.9.17p1 (1.9.14 1.9.17 < 1.9.17p1) allows unprivileged local users to escalate their privileges to root via sudo chroot option when etc nsswitch.conf file is used from a user controlled directory. here is a poc to exploit that vulnerability. It consolidates various techniques and methods to identify and exploit potential paths for privilege escalation, helping users quickly assess and enhance the security of linux systems. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host. By exploiting vulnerabilities in the linux kernel we can sometimes escalate our privileges. what we usually need to know to test if a kernel exploit works is the os, architecture and kernel version. In this post, i'll cover the most common and effective linux privilege escalation techniques, from exploiting misconfigurations to leveraging kernel vulnerabilities.

Linux Privilege Escalation Kernel Exploits Steflan S Security Blog It consolidates various techniques and methods to identify and exploit potential paths for privilege escalation, helping users quickly assess and enhance the security of linux systems. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host. By exploiting vulnerabilities in the linux kernel we can sometimes escalate our privileges. what we usually need to know to test if a kernel exploit works is the os, architecture and kernel version. In this post, i'll cover the most common and effective linux privilege escalation techniques, from exploiting misconfigurations to leveraging kernel vulnerabilities.
Linux Privilege Escalation With Kernel Exploits Zsecurity By exploiting vulnerabilities in the linux kernel we can sometimes escalate our privileges. what we usually need to know to test if a kernel exploit works is the os, architecture and kernel version. In this post, i'll cover the most common and effective linux privilege escalation techniques, from exploiting misconfigurations to leveraging kernel vulnerabilities.

Windows Privilege Escalation Kernel Exploits Steflan S Security Blog
Comments are closed.