Common C2 Frameworks Used Key Examples Explained Network Threat
Common C2 Frameworks Used Key Examples Explained Network Threat Discover common c2 frameworks used by attackers and learn how knowing them helps boost your cybersecurity defense. Despite new c2 frameworks appearing every year, these five still form the backbone of real world offensive operations. whether you’re defending networks, threat hunting, or running red team campaigns, understanding how these frameworks function—and why they continue to dominate is essential.

Common C2 Frameworks Used Key Examples Explained Network Threat In this article, we will cover how c2 frameworks operate, their role in modern attacks, and strategies to detect and mitigate these threats. This guide will explain what c2 frameworks are, how attackers use them, and most importantly — how soc teams detect and stop them using detection engineering techniques like beaconing. In this blog, we explained how powerful c2 frameworks can be in maintaining stealthy operations for both red teams and cybercriminals. we highlighted examples where advanced persistent threats (apts) leverage trusted applications and networks to conceal post exploitation activity. Find out some of the most used c2 post exploitation frameworks for pentesting and much more.
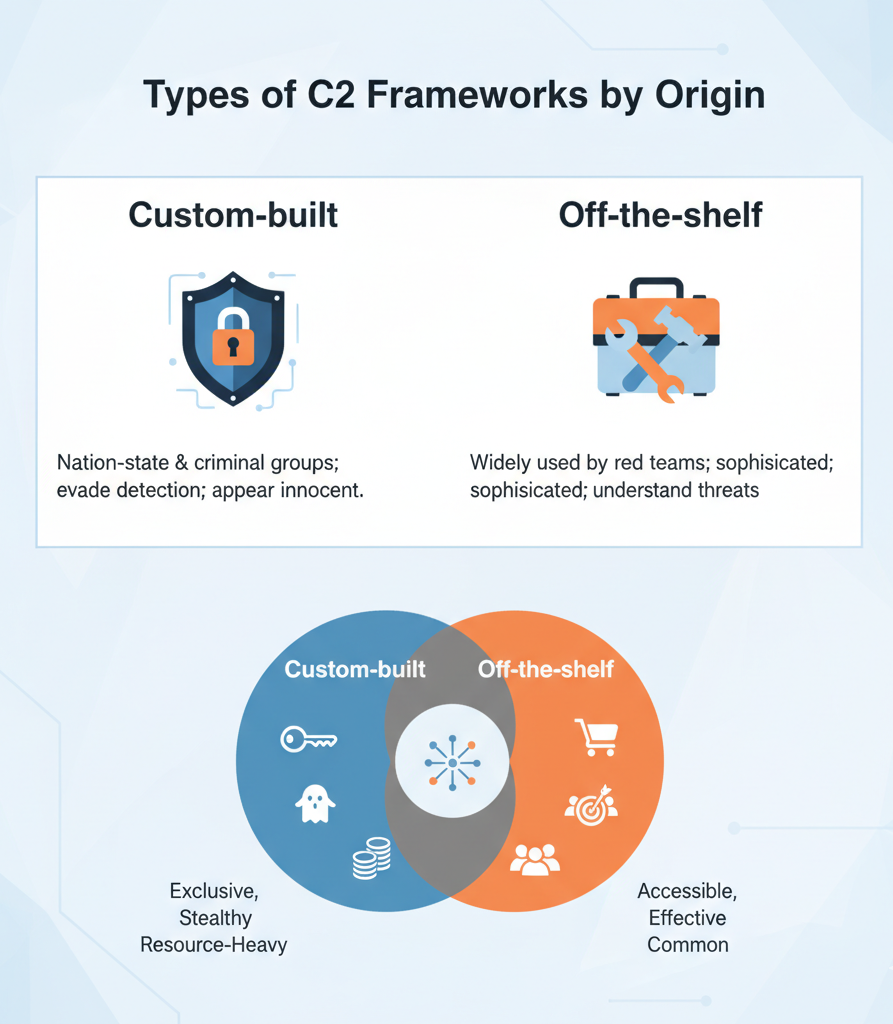
Common C2 Frameworks Used Key Examples Explained Network Threat In this blog, we explained how powerful c2 frameworks can be in maintaining stealthy operations for both red teams and cybercriminals. we highlighted examples where advanced persistent threats (apts) leverage trusted applications and networks to conceal post exploitation activity. Find out some of the most used c2 post exploitation frameworks for pentesting and much more. For educational purposes, resecurity has developed sample yara rules for various c2 frameworks to assist network defenders. this information may also be useful for red team specialists in planning potential evasion tactics when conducting vulnerability assessments and penetration testing (vapt). In this guide, you’ll learn what is a c2 server and framework, why you’d want to use one, and the key benefits they can provide you and your team. you’ll discover some of the most popular c2 frameworks available today and get hands on experience using the popular open source c2 framework havoc. Understanding how to detect c2 traffic is just as important as knowing how to use these frameworks. key detection strategies include: monitor for regular, periodic outbound connections (beaconing patterns). tools like rita (real intelligence threat analytics) are built to detect this. Commercial and open source c2 and post exploitation frameworks save red teamers time on custom development and allow them to quickly change ttps in their engagements. not surprisingly, adversaries also find them attractive due to their ease of use and flexibility.
Comments are closed.