Command Line Forensics To Find Masquerading Malware On Linux

Linux Forensics Cheatsheet Pdf Internet Protocols Information Age In this article, we will go hands on with 10 essential linux commands used daily by digital forensic analysts. we will solve real challenges, including: detecting file masquerading (a. In this video sandfly founder craig rowland goes over the basics behind using command line tools on linux to look into a suspicious process. you’ll learn how to start a benign process and have it masquerade to hide what it is like malware (process masquerading).

Detecting Linux Kernel Process Masquerading With Command Line Forensics Step by step guide to detect and analyze linux malware and attacks: botnets, miners, and more. includes commands, verification, and troubleshooting. While advanced security tools have their place, the power of basic linux command line tools for forensic analysis should not be underestimated. this guide will walk you through practical approaches to detect and respond to suspicious activities using simple, built in linux commands. Linux forensics is a critical skill for cybersecurity professionals investigating incidents, analyzing breaches, or recovering data. this guide covers verified commands, log analysis techniques, and file system forensics to help you gather evidence efficiently on linux systems. Through a series of hands on exercises, you will use standard command line utilities to investigate common signs of a compromise, gaining practical skills in system monitoring and basic forensic analysis.
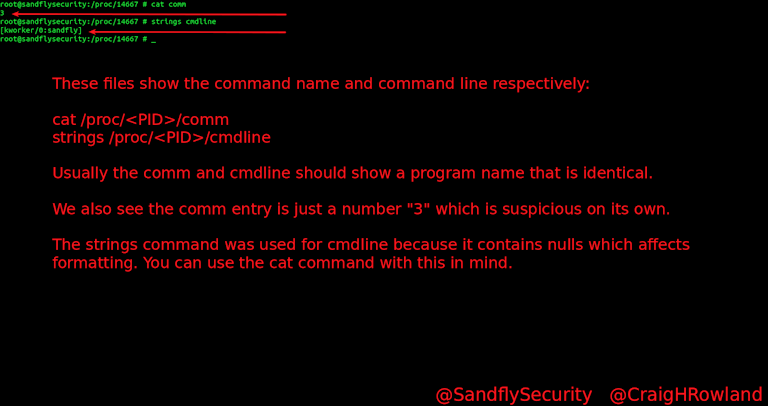
Linux Malware Detection Ubuntu Debian Redhat Suse Fedora Linux forensics is a critical skill for cybersecurity professionals investigating incidents, analyzing breaches, or recovering data. this guide covers verified commands, log analysis techniques, and file system forensics to help you gather evidence efficiently on linux systems. Through a series of hands on exercises, you will use standard command line utilities to investigate common signs of a compromise, gaining practical skills in system monitoring and basic forensic analysis. This lab reinforced the reality that a significant portion of linux security monitoring does not require specialized tooling. the commands used here are available on virtually every linux system and are fast to run during incident triage. Now you have two solid ways to use the linux command line to investigate suspicious processes trying to masquerade as kernel threads. adapted from original post which appeared on sandfly security. The document is a comprehensive cheat sheet for advanced linux detection and forensics, detailing various commands and file paths for analyzing system processes, logs, and kernel states. This article delves into six essential linux commands that i, as a seasoned security professional, frequently utilize for malware analysis. these commands are versatile and adaptable to various scenarios, ranging from basic file inspection to intricate reverse engineering tasks.
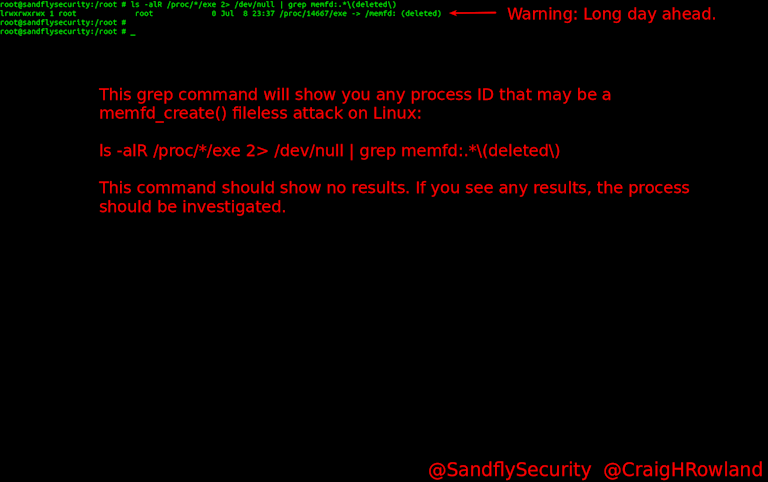
Linux Malware Detection Ubuntu Debian Redhat Suse Fedora This lab reinforced the reality that a significant portion of linux security monitoring does not require specialized tooling. the commands used here are available on virtually every linux system and are fast to run during incident triage. Now you have two solid ways to use the linux command line to investigate suspicious processes trying to masquerade as kernel threads. adapted from original post which appeared on sandfly security. The document is a comprehensive cheat sheet for advanced linux detection and forensics, detailing various commands and file paths for analyzing system processes, logs, and kernel states. This article delves into six essential linux commands that i, as a seasoned security professional, frequently utilize for malware analysis. these commands are versatile and adaptable to various scenarios, ranging from basic file inspection to intricate reverse engineering tasks.

Detecting Linux Kernel Process Masquerading With Command Line Forensics The document is a comprehensive cheat sheet for advanced linux detection and forensics, detailing various commands and file paths for analyzing system processes, logs, and kernel states. This article delves into six essential linux commands that i, as a seasoned security professional, frequently utilize for malware analysis. these commands are versatile and adaptable to various scenarios, ranging from basic file inspection to intricate reverse engineering tasks.

Detecting Linux Kernel Process Masquerading With Command Line Forensics
Comments are closed.