Cn 35 Network Security Model With Example

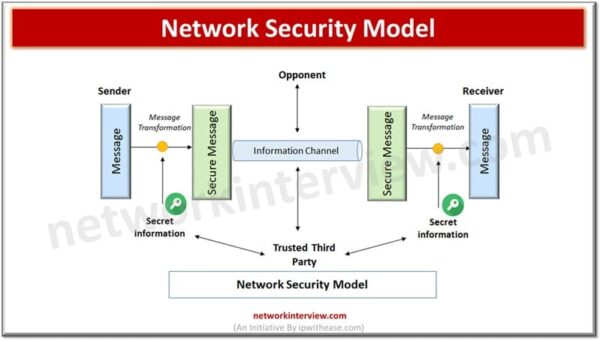
Network Security Model Pdf Encryption Cipher Cn 35: network security model with example cs & it tutorials by vrushali 👩🎓 66k subscribers subscribed. A network security model explains how secure communication is achieved over an insecure network using security services, mechanisms, and protocols. defines the framework for secure data transmission over networks.

Network Security Model Pdf Security Computer Security It is important that you secure, store and backup your data on a regular basis. 4, firewall : firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. Overview of network security: discuss the role of network security in protecting organizational data and infrastructure from unauthorized access and potential threats. mention recent trends in cybersecurity, emphasizing the increased sophistication of cyber attacks. A network security model in computer networks refers to the structured defensive mechanisms and protocols implemented to protect the integrity, confidentiality and availability of data transmitted between devices over an interconnected system of networks. Explain security concepts, ethics in network security. identify and classify various attacks and explain the same. compare and contrast symmetric and asymmetric encryption systems and their vulnerability to various attacks. explain the role of third party agents in the provision of authentication services.

Network Security Model Learnbywatch A network security model in computer networks refers to the structured defensive mechanisms and protocols implemented to protect the integrity, confidentiality and availability of data transmitted between devices over an interconnected system of networks. Explain security concepts, ethics in network security. identify and classify various attacks and explain the same. compare and contrast symmetric and asymmetric encryption systems and their vulnerability to various attacks. explain the role of third party agents in the provision of authentication services. Cn 36 : network attacks | active attack vs passive attack | explain with examples 5. This lesson gives a global overview of possible network security threats, vulnerabilities, and countermeasures. Configuration and troubleshooting: students will learn how to configure network devices, set up network services, and troubleshoot common networking issues. this practical experience is crucial for preparing students for real world challenges in the field. network design: the lab provides a platform for students to design and implement. Overview of network security:elements of network security , classification of network attacks ,security methods ,symmetric key cryptography :data encryption standard (des),advanced encryption standard (aes) , public key cryptography :rsa algorithm ,diffie hellman key exchange protocol , authentication :hash function , secure hash algorithm (sha.
Network Security Model And Cryptography Network Interview Cn 36 : network attacks | active attack vs passive attack | explain with examples 5. This lesson gives a global overview of possible network security threats, vulnerabilities, and countermeasures. Configuration and troubleshooting: students will learn how to configure network devices, set up network services, and troubleshoot common networking issues. this practical experience is crucial for preparing students for real world challenges in the field. network design: the lab provides a platform for students to design and implement. Overview of network security:elements of network security , classification of network attacks ,security methods ,symmetric key cryptography :data encryption standard (des),advanced encryption standard (aes) , public key cryptography :rsa algorithm ,diffie hellman key exchange protocol , authentication :hash function , secure hash algorithm (sha.

What Is Network Security Model Definition Importance Strategy Unstop Configuration and troubleshooting: students will learn how to configure network devices, set up network services, and troubleshoot common networking issues. this practical experience is crucial for preparing students for real world challenges in the field. network design: the lab provides a platform for students to design and implement. Overview of network security:elements of network security , classification of network attacks ,security methods ,symmetric key cryptography :data encryption standard (des),advanced encryption standard (aes) , public key cryptography :rsa algorithm ,diffie hellman key exchange protocol , authentication :hash function , secure hash algorithm (sha.

What Is Network Security Model Definition Importance Strategy
Comments are closed.