Cmmc Compliance Truly Simplified Relevant Compliance

How To Demonstrate Compliance With Cmmc An Overview Navigating cmmc compliance can be overwhelming for businesses. our compliance software simplifies the process with intuitive tools, guided workflows, and actionable insights. An it msp can simplify the path to compliance by providing the expertise, tools, and support needed to meet the right cmmc level for your business. whether you’re starting at level 1 or aiming for level 2, the right partner can save time, reduce risk, and make compliance much more manageable.
Cmmc Compliance Truly Simplified Relevant Compliance If you’re ready to simplify cmmc compliance and protect your clients’ data, get a huntress demo today and see how our platform can make continuous compliance and security effortless. Cmmc compliant managed services: providing cmmc certified managed services so your systems remain secure and compliant with all relevant frameworks, including cmmc. We created the following cmmc compliance checklist to help you expedite your compliance, lower your costs, & maintain your competitive position in the dib. cmmc compliance is designed to raise cybersecurity levels throughout the defense industrial base (dib) by better protecting fci and cui. By simplifying compliance processes and offering different pathways for assessment, the updated cmmc rule helps dib companies of all sizes meet their obligations to protect sensitive data—enabling them to continue participating in critical defense contracts without unnecessary barriers.
Cmmc Compliance Truly Simplified Relevant Compliance We created the following cmmc compliance checklist to help you expedite your compliance, lower your costs, & maintain your competitive position in the dib. cmmc compliance is designed to raise cybersecurity levels throughout the defense industrial base (dib) by better protecting fci and cui. By simplifying compliance processes and offering different pathways for assessment, the updated cmmc rule helps dib companies of all sizes meet their obligations to protect sensitive data—enabling them to continue participating in critical defense contracts without unnecessary barriers. Explore what cmmc is, why it matters for defense contractors, and how it strengthens cybersecurity across the supply chain. Among the myriad of tasks required for compliance, the significance of clear and concise documentation cannot be overstated. this article delves into why meticulous documentation is the unsung hero in ensuring organizations' readiness for nist 800 171 and cmmc compliance. Building a cmmc 2.0 compliance checklist helps ensure you tackle all the essential steps, from assessing your current security posture to documenting final proofs of compliance. This complete cmmc compliance checklist and guide helps you meet requirements, prepare for audits, and improve cyber maturity across your organization.
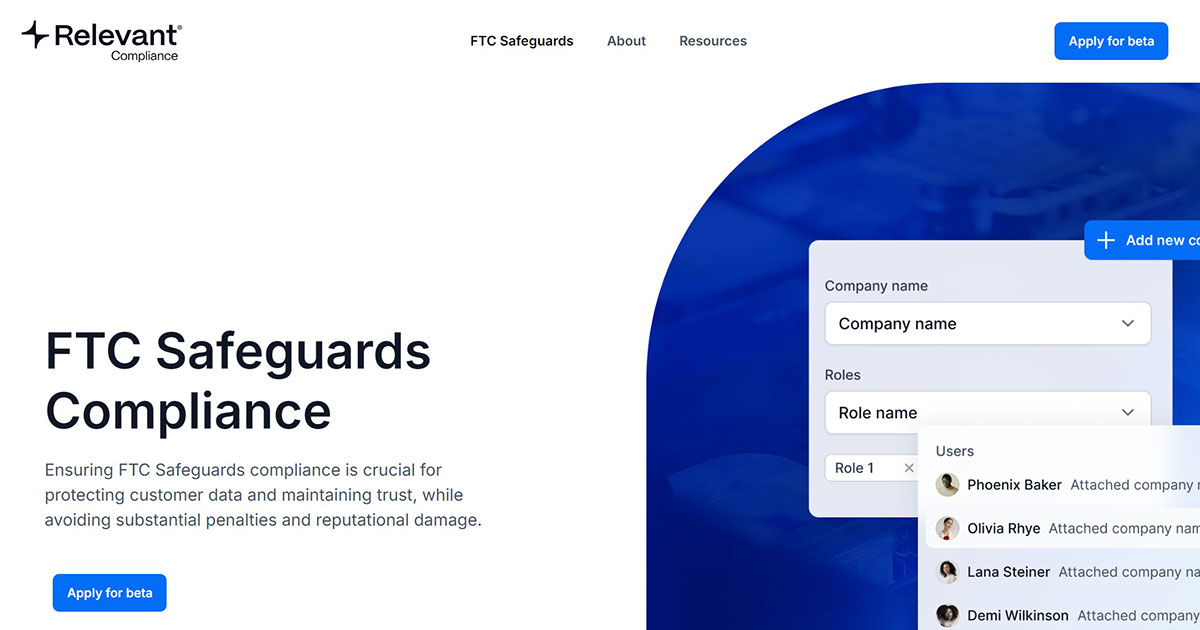
Cmmc Compliance Truly Simplified Relevant Compliance Explore what cmmc is, why it matters for defense contractors, and how it strengthens cybersecurity across the supply chain. Among the myriad of tasks required for compliance, the significance of clear and concise documentation cannot be overstated. this article delves into why meticulous documentation is the unsung hero in ensuring organizations' readiness for nist 800 171 and cmmc compliance. Building a cmmc 2.0 compliance checklist helps ensure you tackle all the essential steps, from assessing your current security posture to documenting final proofs of compliance. This complete cmmc compliance checklist and guide helps you meet requirements, prepare for audits, and improve cyber maturity across your organization.
Comments are closed.