Cloud Security Management Identity Risks
Cloud Security Management Identity Risks In this comprehensive guide, we’ll break down the biggest cloud identity risks, explain why traditional security models fall short, and share actionable strategies to protect your organization using modern identity and access management (iam) and zero trust principles. Our comprehensive guide on cloud risk management covers risk assessment, mitigation, and compliance, and more.
Cloud Security Management Identity Risks To mitigate these risks, cybersecurity teams are adopting a layered approach grounded in zero trust principles: leading cloud providers like aws and google cloud recommend replacing long term credentials with short lived iam roles for human and machine identities. Centralized identity management eliminates the security risks of fragmented authentication systems by providing consistent policy enforcement, unified monitoring, and streamlined access control across all resources. Iam ensures individuals access only the resources they are authorized to by verifying their identity and managing their roles and privileges. insufficient iam can lead to major security breaches. Iam is a foundational component of securing resources, and its implementation in a cloud native environment helps protect against the potentially catastrophic consequences of security breaches, noncompliance, and operational slow downs.

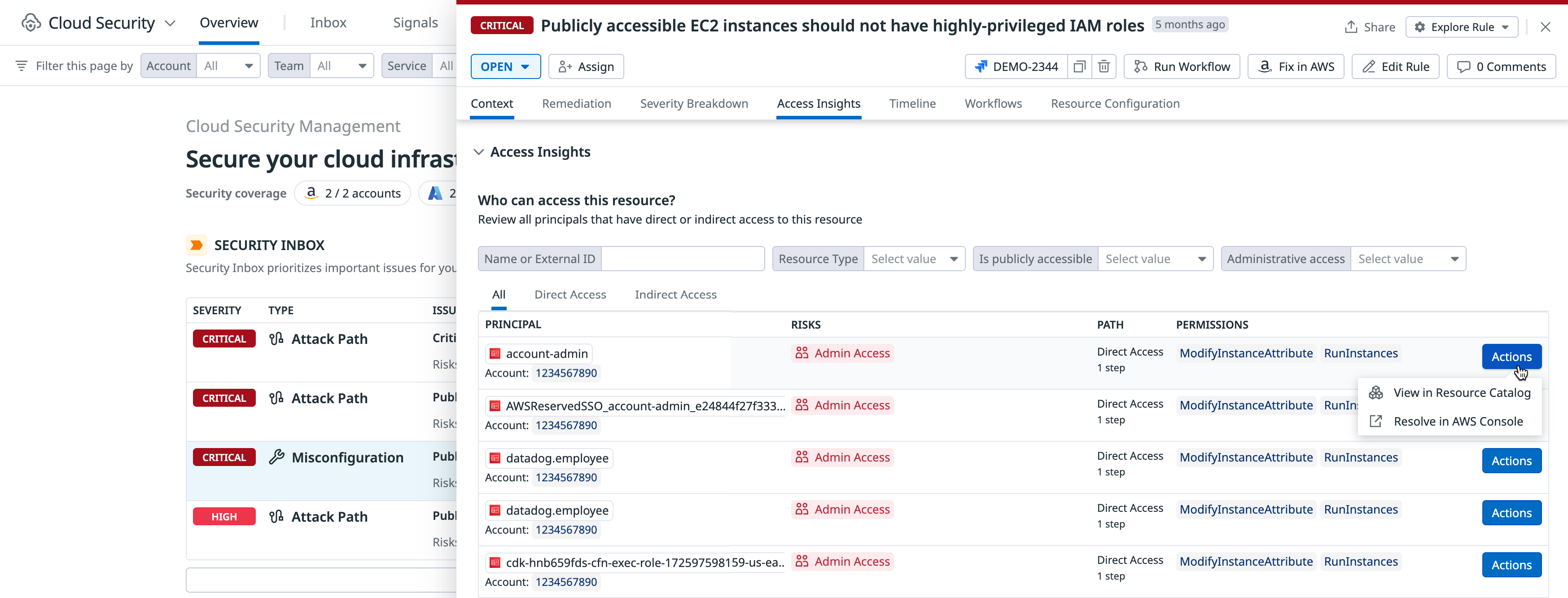
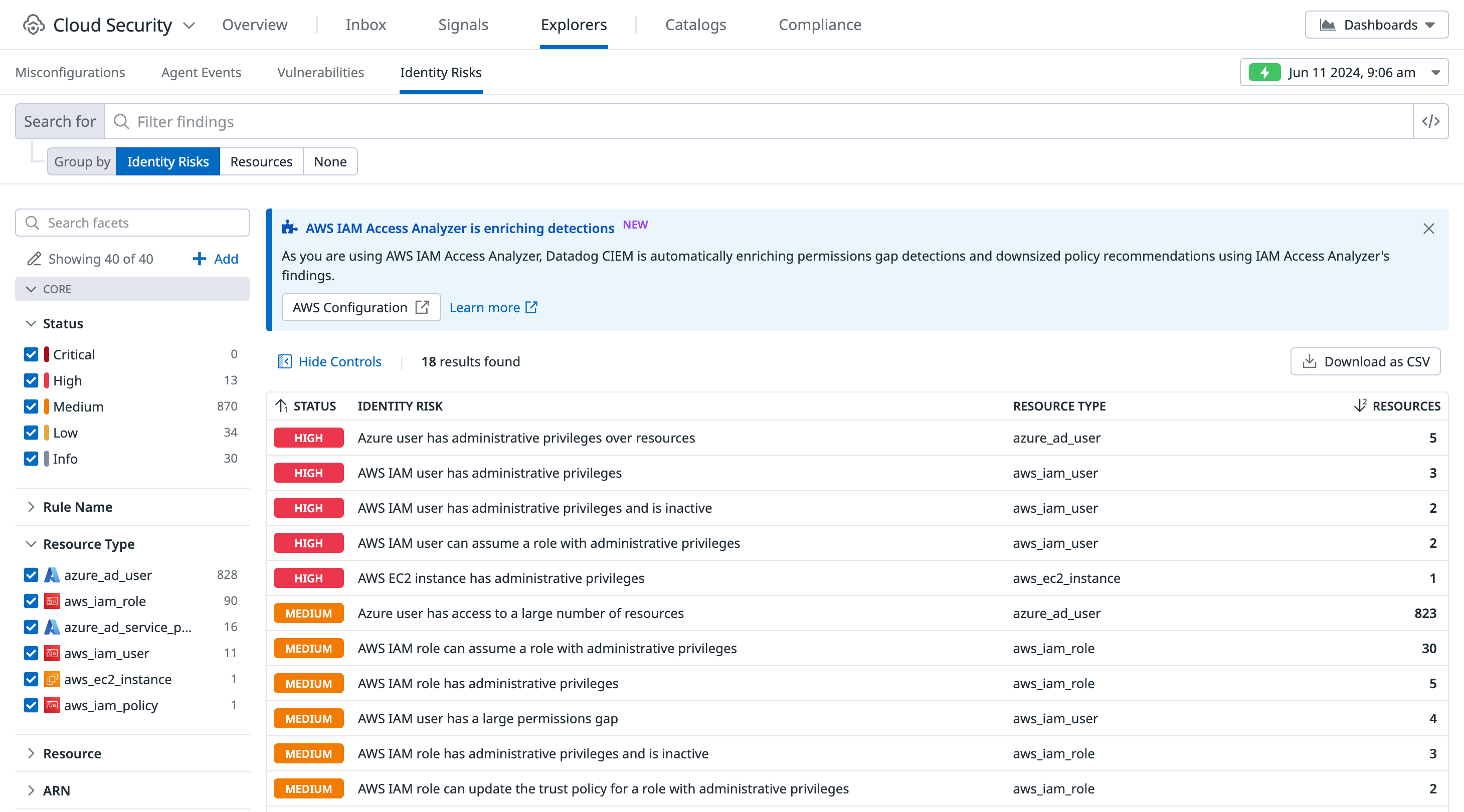
Cloud Security Management Identity Risks Iam ensures individuals access only the resources they are authorized to by verifying their identity and managing their roles and privileges. insufficient iam can lead to major security breaches. Iam is a foundational component of securing resources, and its implementation in a cloud native environment helps protect against the potentially catastrophic consequences of security breaches, noncompliance, and operational slow downs. Learn which cloud security risks matter most and how attackers exploit identity, misconfiguration, and trusted workflows to breach environments. Learn the top identity and access management risks to keep your saas stack secure and safeguard it from cyberattacks. A complete guide to cloud security architecture covering layers, risks, monitoring tools, best practices, and the shared responsibility model. Cloud security identity risks is available for aws, azure, and gcp. cloud security identity risk detections include users, roles, groups, policies, ec2 instances, and lambda functions. review your organization’s active identity risks on the identity risks findings page.
Comments are closed.