Cloud Security Checklist Networking Elements Pdf
Cloud Security Checklist Pdf Use security groups for controlling inbound and outbound traffic, and automatically apply rules for both security groups and wafs using aws firewall manager. group different resources into different subnets to create routing layers, for example database resources do not need a route to the internet. Practical guide to help you conduct a thorough cloud security assessment and strengthen your security posture. pro tip: print this checklist or keep it in your cloud security documentation hub for quick reference during quarterly or annual assessments.

Cloud Security Checklist Pdf Cloud Computing Computer Network As more businesses shift to the cloud, ensuring a secure and compliant cloud environment is essential. this cloud security assessment checklist helps identify vulnerabilities, enforce best practices, and protect sensitive data stored and processed in cloud platforms. In this worbook, we are examining key compliance requirements, best practices, risks, testing steps, and recommendation plans for the following cloud service providers:. The checklist covers technical, organizational and procedural security controls for iaas clouds. it aims to be comprehensive while keeping the list manageable for practical use. It is organised as a checklist of the most important security related items, divided into different layers, starting from the physical layer up to the data layer.
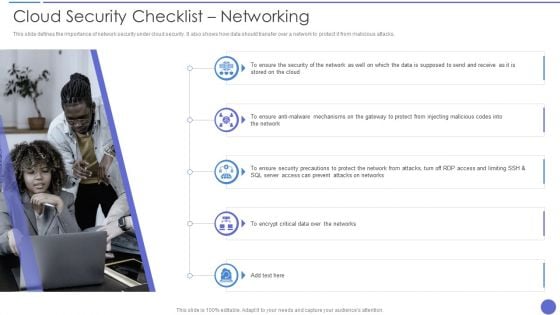
Cloud Security Checklist Networking Elements Pdf The checklist covers technical, organizational and procedural security controls for iaas clouds. it aims to be comprehensive while keeping the list manageable for practical use. It is organised as a checklist of the most important security related items, divided into different layers, starting from the physical layer up to the data layer. This collection is a good place to start if you’re looking to build out your cloud security knowledge base, because the technical detail provided in these reports and guides will enable you to start crafting a technical roadmap for your organization’s transition to the cloud. Once you have assessed the benefits of migrating a business system or its function to the cloud (see our white book of cloud adoption), the next step is to consider the security and risk management implications of doing so. Presenting cloud security checklist networking elements pdf to provide visual cues and insights. share and navigate important information on five stages that need your due attention. Fedramp reviews cloud services for adherence to security best practices and puts vendors on an approved list. by directing users to fedramp authorized apps, it admins provide some freedom while improving the odds that their cloud remains secure.

Network Security Checklist Pdf Cloud Computing Computer Network This collection is a good place to start if you’re looking to build out your cloud security knowledge base, because the technical detail provided in these reports and guides will enable you to start crafting a technical roadmap for your organization’s transition to the cloud. Once you have assessed the benefits of migrating a business system or its function to the cloud (see our white book of cloud adoption), the next step is to consider the security and risk management implications of doing so. Presenting cloud security checklist networking elements pdf to provide visual cues and insights. share and navigate important information on five stages that need your due attention. Fedramp reviews cloud services for adherence to security best practices and puts vendors on an approved list. by directing users to fedramp authorized apps, it admins provide some freedom while improving the odds that their cloud remains secure.
Comments are closed.