Cloud Security Checklist Data Encryption Cloud Computing Security It
Cloud Security Checklist Data Encryption Cloud Computing Security From ensuring proper encryption, and monitoring access, to maintaining compliance, this checklist keeps your cloud environment resilient and compliant with emerging threats. without it, your business risks falling victim to easily avoidable security lapses. Download our free cloud security assessment checklist to spot risks, ensure compliance & secure your cloud environment for stronger data protection & control.
Cloud Security Checklist Pdf But where do you start? this ultimate checklist breaks down the 15 essential steps to secure your cloud infrastructure. from implementing strong access controls to leveraging cloud native security features, we've got you covered. don't leave your data and reputation vulnerable to the next big breach. Protect your cloud security environment with a comprehensive security checklist, risk assessments, and best practices for compliance and resilience. Your complete cloud security checklist that promises the ultimate protection against cloud risks covering iam, posture management, and more. The complete guide to cloud security best practices for it leaders. 20 actionable controls across iam, network, data protection, monitoring, and compliance with aws, azure, and gcp examples.

Cloud Security Checklist Data Encryption Cloud Computing Security It Your complete cloud security checklist that promises the ultimate protection against cloud risks covering iam, posture management, and more. The complete guide to cloud security best practices for it leaders. 20 actionable controls across iam, network, data protection, monitoring, and compliance with aws, azure, and gcp examples. Struggling to prioritize cloud security risks? use this expert backed review checklist covering iam, encryption, logging, monitoring, and more. built for cisos, vps, and it leaders who need clarity and results. Discover the ultimate cloud security checklist to protect your data and achieve peace of mind. learn the essential steps to secure your cloud storage and services, manage user access, monitor activity, ensure compliance, and more. Explore our comprehensive guide to cloud security audits, covering key aspects such as compliance, risk assessment, best practices, and tools. By following this checklist, you will strengthen their overall digital security and create a culture where everyone understands the importance of keeping data secure.

Cloud Security Checklist Pdf Cloud Computing Computer Network Struggling to prioritize cloud security risks? use this expert backed review checklist covering iam, encryption, logging, monitoring, and more. built for cisos, vps, and it leaders who need clarity and results. Discover the ultimate cloud security checklist to protect your data and achieve peace of mind. learn the essential steps to secure your cloud storage and services, manage user access, monitor activity, ensure compliance, and more. Explore our comprehensive guide to cloud security audits, covering key aspects such as compliance, risk assessment, best practices, and tools. By following this checklist, you will strengthen their overall digital security and create a culture where everyone understands the importance of keeping data secure.
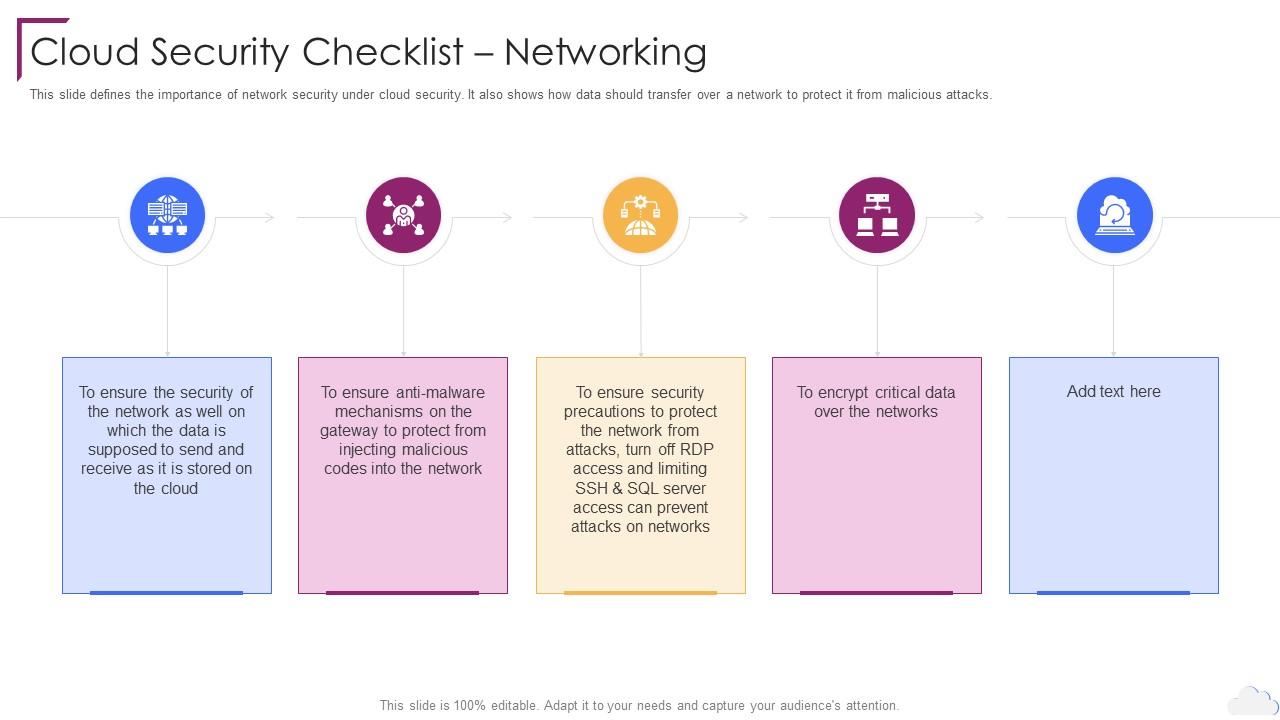
Cloud Security Checklist Networking Cloud Computing Security Explore our comprehensive guide to cloud security audits, covering key aspects such as compliance, risk assessment, best practices, and tools. By following this checklist, you will strengthen their overall digital security and create a culture where everyone understands the importance of keeping data secure.
Comments are closed.