Cloud Security Architecture Zero Trust Model

Cloud Security Architecture Zero Trust Model Artofit The zero trust model shifts the security focus from perimeter based security to an approach where no user or device is considered to be inherently trustworthy. instead, every access request. According to cisa, zero trust architecture is implemented through five distinct pillars that address identity, device, network environment, application workload, and data security domains.
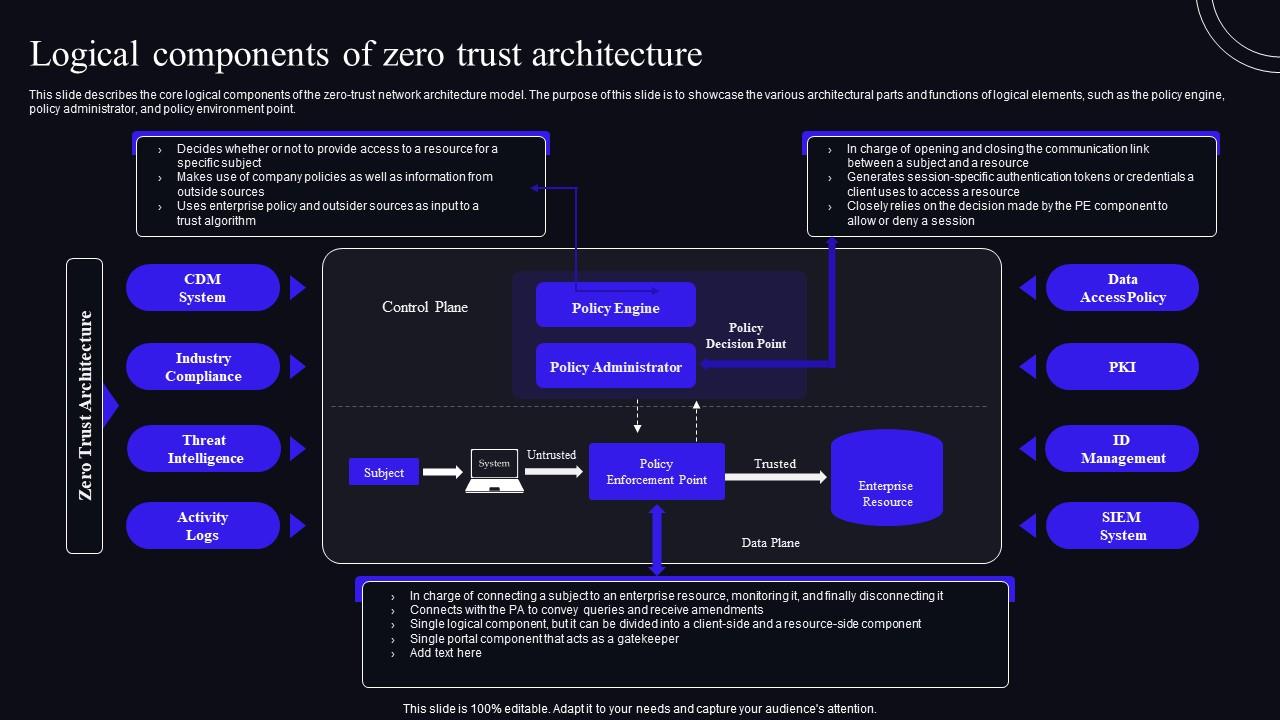
Logical Components Of Zero Trust Architecture Zero Trust Security Model Explore how zero trust architecture enables cyber resilience across multi cloud environments, with core principles and practical implementation strategies. Discover the power of zero trust architecture for cloud security. explore the core principles, key components, and best practices for implementation. This research explores the implementation and effectiveness of zero trust architecture (zta) in addressing security challenges within cloud networks. This article explores the technical foundation of zero trust, core implementation strategies, and the architectural components required to engineer a resilient, adaptive security model.
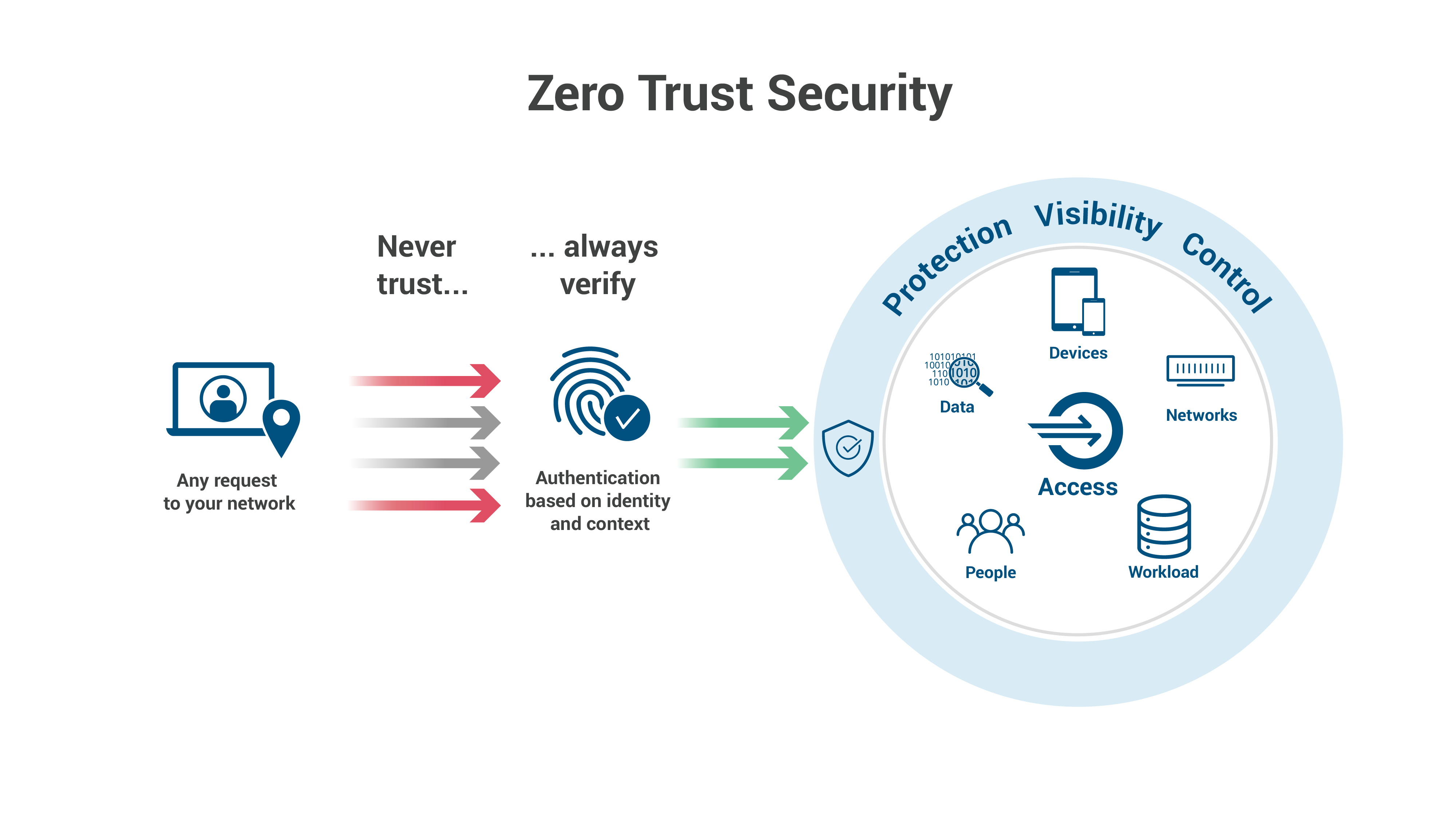
What Is Zero Trust Architecture Zero Trust Security Model This research explores the implementation and effectiveness of zero trust architecture (zta) in addressing security challenges within cloud networks. This article explores the technical foundation of zero trust, core implementation strategies, and the architectural components required to engineer a resilient, adaptive security model. This architecture guide is focused on the cisco zero trust framework with the user and device security, application and data security, and network and cloud security pillars. What is zero trust on aws? zero trust is a security model centered on the idea that access to data should not be solely made based on network location. The csa 2025 top threats report ranks insufficient identity and access management as the #1 cloud security threat—exactly what zero trust addresses. this guide explains zero trust principles, implementation strategies, and how to apply them in aws, azure, and gcp. We’ve covered zero trust security architecture and cloud security architecture separately. now let’s look at how organisations can integrate them into a unified, modern security architecture.
Comments are closed.