Cloud Security And Privacy
Cloud Security And Privacy Pdf We review the research progress on privacy security issues from the perspective of several privacy security protection technologies in cloud computing. first, we introduce some privacy security risks of cloud computing and propose a comprehensive privacy security protection framework. Ecome extremely important. this article examines key challenges by ensuring data security and maintaining user priv. cy in a cloud environment. the most important topics specified include data protection technologies, access control mechanisms, encryption methods, and secu.
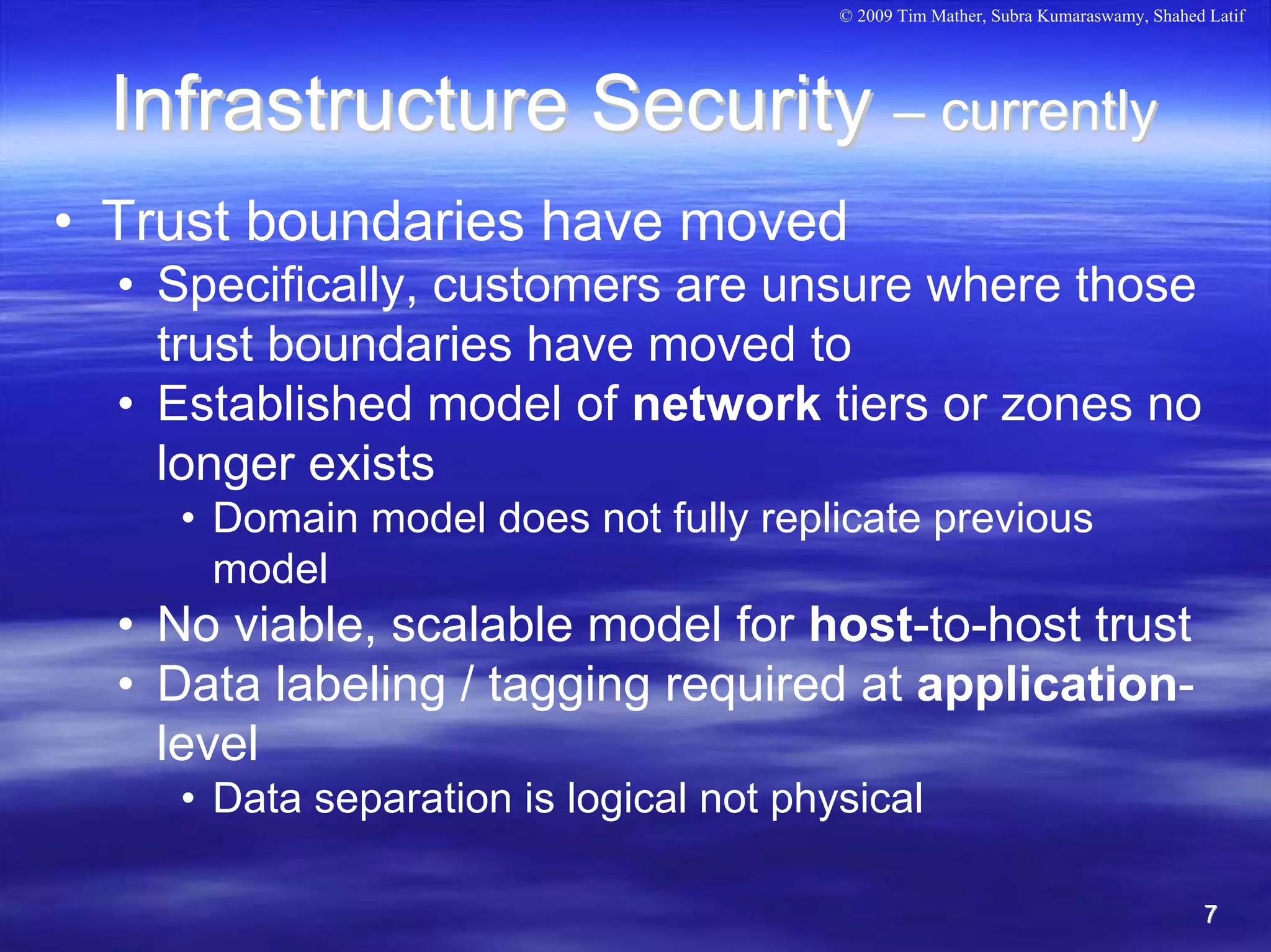
Cloud Security And Privacy Pdf By reviewing recent trends and case studies, the article provides practical recommendations for enhancing cloud security and protecting data privacy. Cloud security mainly focuses on how to implement policies, processes, and technologies together so they ensure data protection, support regulatory compliance, and provide control over. The rapid development of the cloud has led to more flexibility, cost cutting, and scalability of products but also faces an enormous amount of privacy and security challenges. Cloud data security is the practice of improving data security and privacy when using cloud services. within modern organizations, you store, transmit, and process data across multiple cloud services.
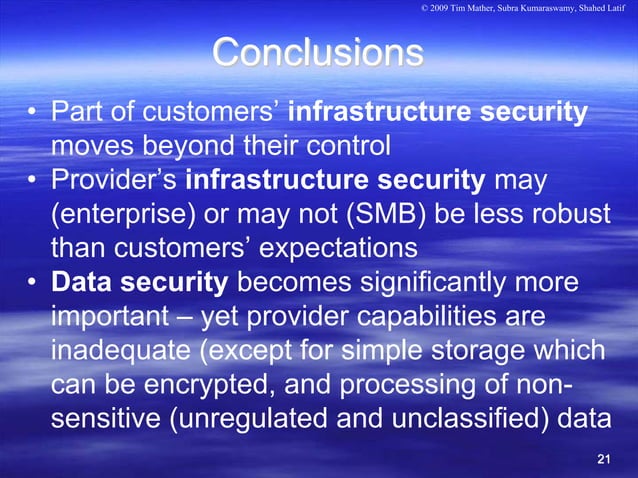
Cloud Security And Privacy Pdf The rapid development of the cloud has led to more flexibility, cost cutting, and scalability of products but also faces an enormous amount of privacy and security challenges. Cloud data security is the practice of improving data security and privacy when using cloud services. within modern organizations, you store, transmit, and process data across multiple cloud services. The paper reviews existing literature and industry practices to identify the key challenges and offers insights into effective strategies to enhance security and privacy in cloud environments. This paper reviews the security and privacy challenges faced by cloud computing, the impact of data breaches, the role of encryption, access control, and the emerging technologies designed to address these challenges. This paper provides an in depth examination of strategies aimed at bolstering security and privacy in cloud environments. central to these strategies are advanced encryption methods, fine grained access control models, and multi factor authentication protocols. Although cloud technology is widely used in many different areas, ensuring the security of the cloud is still very difficult. this content explores the complexities of cloud computing security, including technological advances, challenges, and opportunities.

How Cloud Security Architecture Shapes Data Protection Privacy The paper reviews existing literature and industry practices to identify the key challenges and offers insights into effective strategies to enhance security and privacy in cloud environments. This paper reviews the security and privacy challenges faced by cloud computing, the impact of data breaches, the role of encryption, access control, and the emerging technologies designed to address these challenges. This paper provides an in depth examination of strategies aimed at bolstering security and privacy in cloud environments. central to these strategies are advanced encryption methods, fine grained access control models, and multi factor authentication protocols. Although cloud technology is widely used in many different areas, ensuring the security of the cloud is still very difficult. this content explores the complexities of cloud computing security, including technological advances, challenges, and opportunities.
Comments are closed.