Cloud Design Gatekeeper Pattern

Gatekeeper Pattern Learn how to use the gatekeeper pattern to protect applications and services by using a dedicated host instance as a broker to validate requests and data. See how and learn when to implement a gatekeeper security pattern to protect your cloud hosted apps and services.
Gatekeeper Design Pattern Madhukar S Musings Discover the gatekeeper pattern in software architecture. learn how to centralize security, validation, and access control using asp core and yarp, including practical c# examples, security best practices, and common pitfalls for modern system design. The gatekeeper pattern acts as a security layer that validates access before requests reach application resources. deploy a security gateway in front of protected resources. The gatekeeper pattern is a software design pattern used to control access to resources in a system. the purpose of this pattern is to provide a centralized point of control for managing. By this post, i am starting the series of post on cloud design patterns. these patterns are mostly generic and can be used with any cloud provider but in this series, i will mainly focus on the azure.

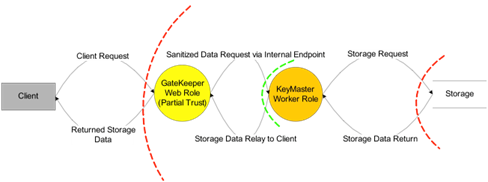
Cloud Pattern Gatekeeper The gatekeeper pattern is a software design pattern used to control access to resources in a system. the purpose of this pattern is to provide a centralized point of control for managing. By this post, i am starting the series of post on cloud design patterns. these patterns are mostly generic and can be used with any cloud provider but in this series, i will mainly focus on the azure. The gatekeeper design pattern is a way to control access to resources or operations in your application. it acts as a mediator to ensure that only authorized or validated requests can proceed to the next stage of execution. In cloud architectures, this idea scales up into the gatekeeper pattern: put a dedicated host or component in front of your app that validates and sanitizes requests, runs in reduced. Summary: learn how to use the gatekeeper pattern to protect applications and services by using a dedicated host instance as a broker to validate requests and data. The gatekeeper pattern places a dedicated, hardened host between clients and backend services. this host's sole responsibility is to validate, authenticate, and sanitize every incoming request before forwarding it to the actual application servers.
Comments are closed.