Cloud Credentials Phishing Google Ads Target Aws Logins
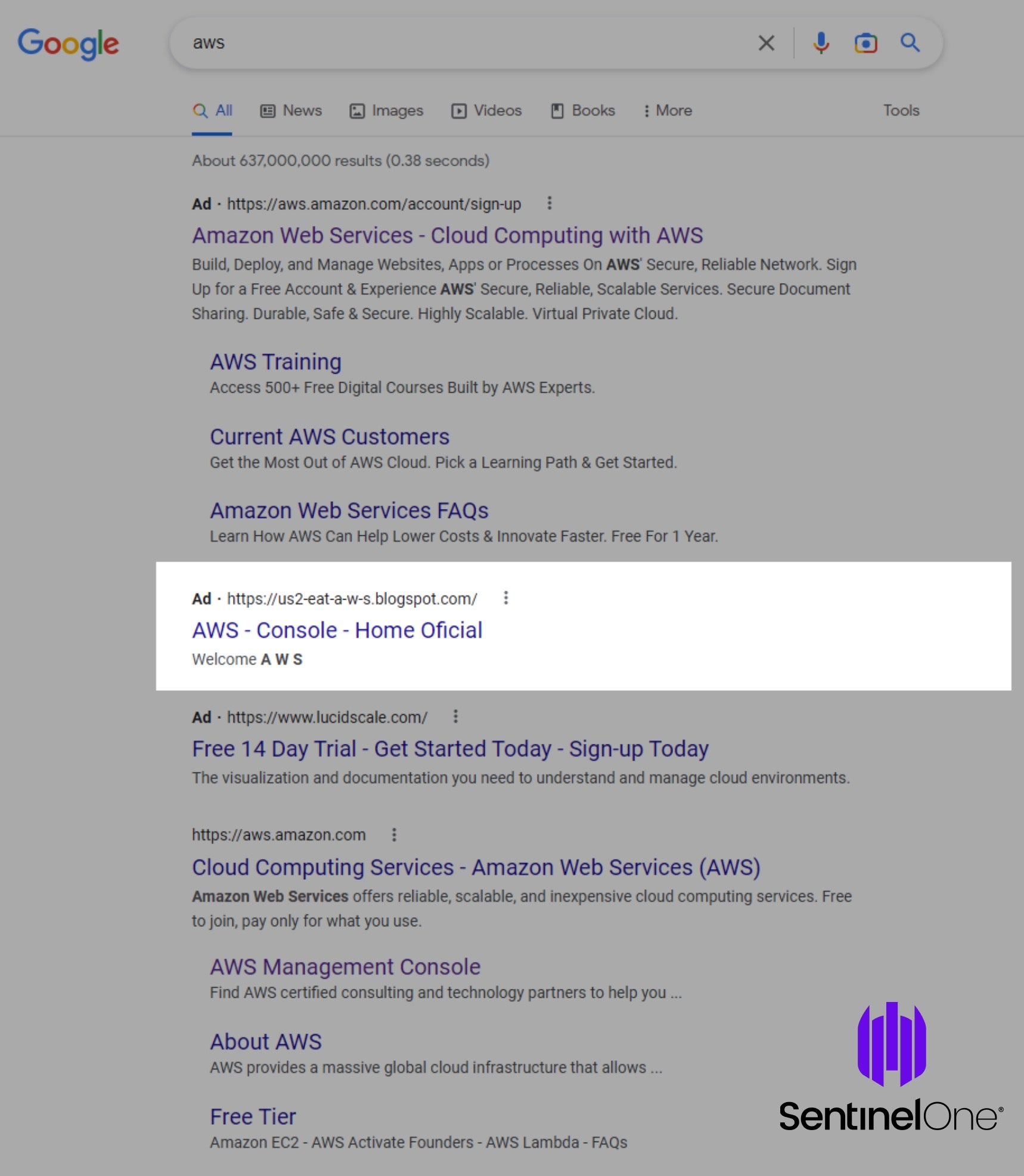
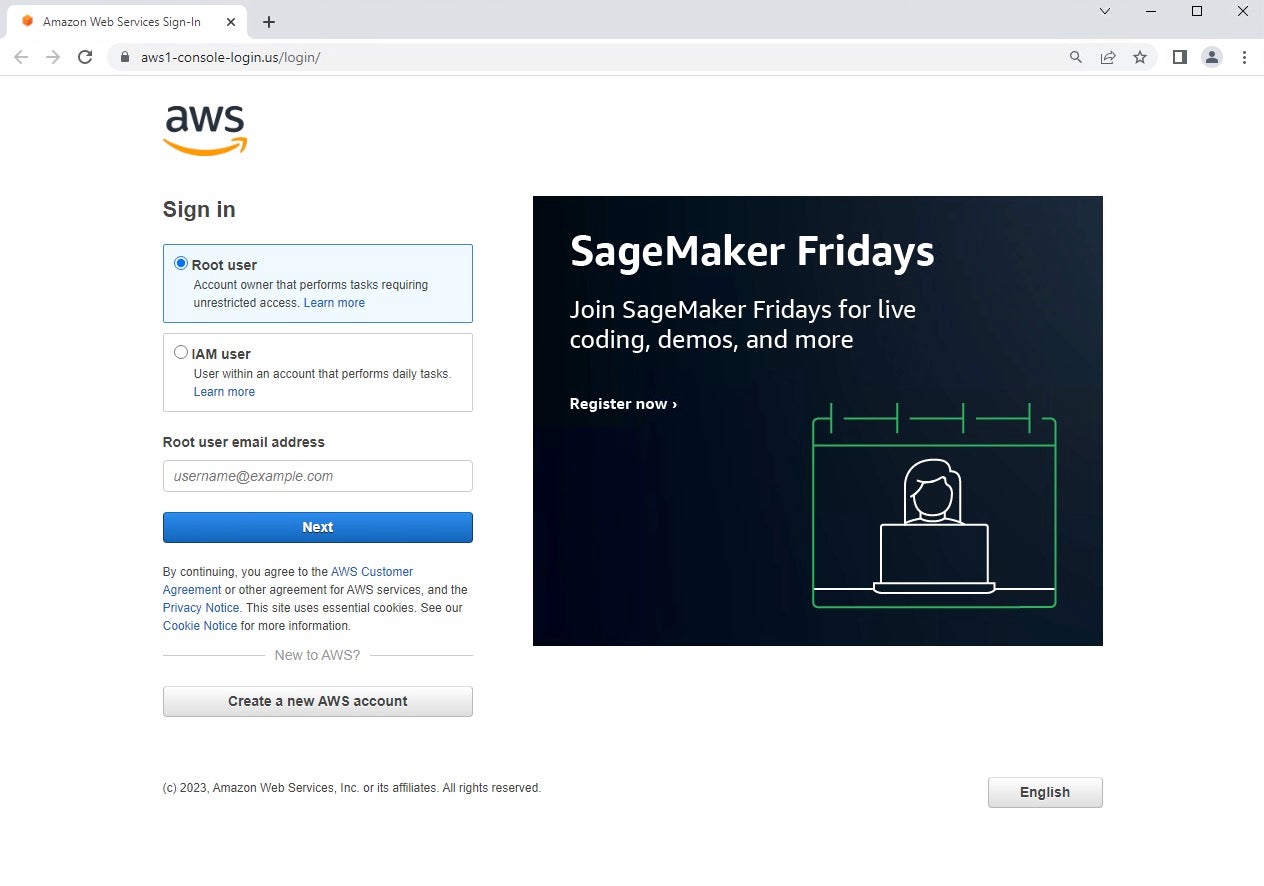
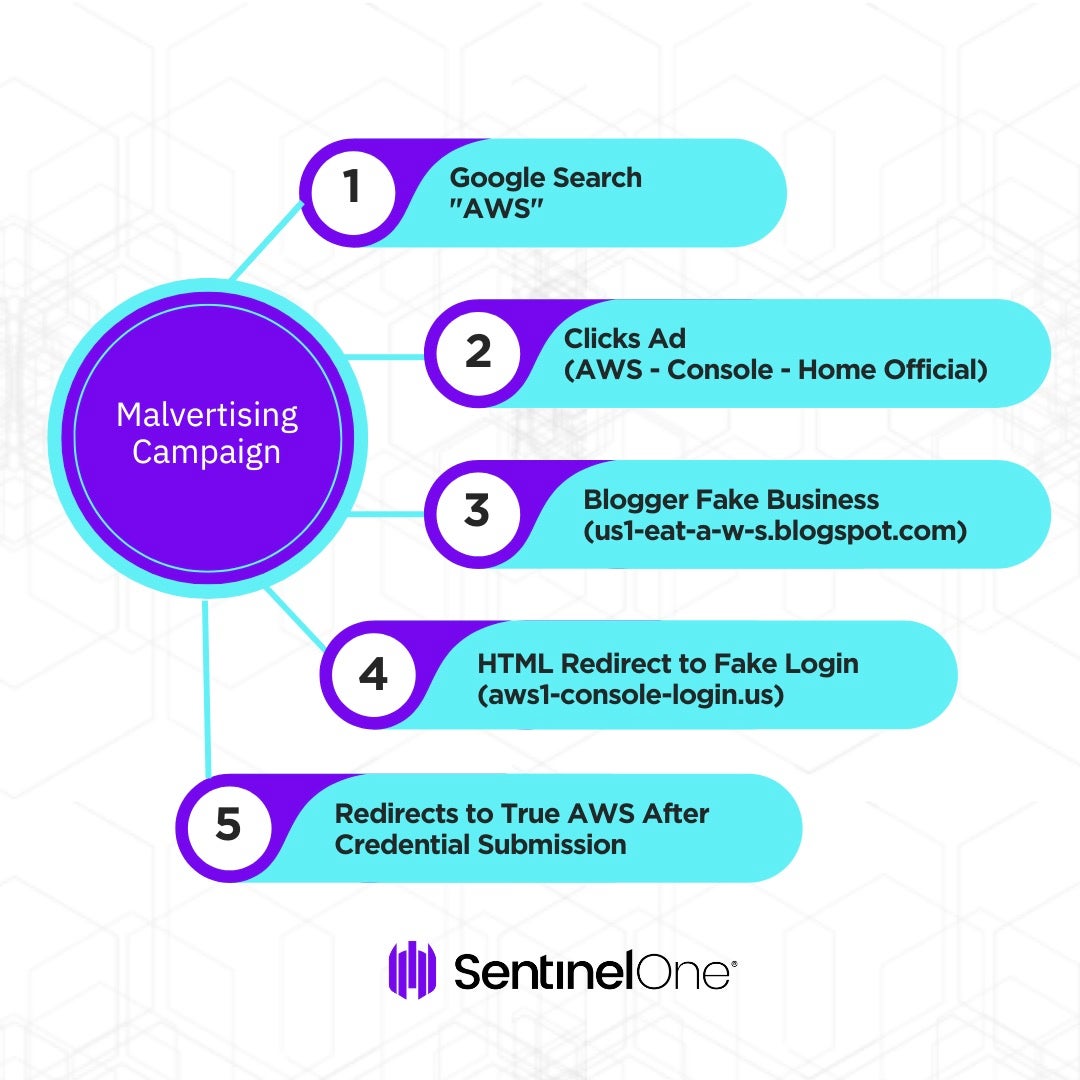
Cloud Credentials Phishing Google Ads Target Aws Logins In recent weeks, google ads, one of the largest online advertising platforms, has become a popular target for these types of attacks. in this analysis, we examine recent malicious google ads targeting amazon web services (aws) logins through fraudulent credential phishing websites. In recent weeks, google ads, one of the largest online advertising platforms, has become a popular target for these types of attacks. in this analysis, we examine recent malicious google ads targeting amazon web services (aws) logins through fraudulent credential phishing websites.

Cloud Credentials Phishing Google Ads Target Aws Logins How does ‘aws login’ get credentials? the aws login command uses the oauth 2.0 authorization code flow with pkce. in the usual scenario, the workflow looks like this: the user runs aws. Datadog security research identified an active adversary in the middle (aitm) phishing campaign targeting aws console credentials via typosquatted domains that mimic aws infrastructure. Aws ses urls are often used to host phishing pages that mimic legitimate aws login portals, tricking users into submitting their credentials on deceptive sites controlled by attackers. A major cloud security incident involving unauthorized access to sensitive data hosted on aws infrastructure highlighted the growing risk of credential based attacks.
Cloud Credentials Phishing Google Ads Target Aws Logins Aws ses urls are often used to host phishing pages that mimic legitimate aws login portals, tricking users into submitting their credentials on deceptive sites controlled by attackers. A major cloud security incident involving unauthorized access to sensitive data hosted on aws infrastructure highlighted the growing risk of credential based attacks. The honeypot, designed to mimic an employee’s aws login, encountered a sophisticated phishing page that only accepted the originally targeted victim’s email address, indicating potential personalization or filtering mechanisms. As victims submit their credentials, the phishing kit polls the attacker's server for instructions every few seconds, adapting the presented prompts to match the authentication stages of real google logins. With tools like wormgpt and fraudgpt available on the dark web, attackers now generate targeted phishing campaigns within minutes. these messages trick users into revealing cloud logins, especially for platforms like microsoft 365, google workspace, and aws iam. The operation is targeting next.js applications vulnerable to react2shell (cve 2025 55182) to gain initial access, then is deploying a multi phase credential harvesting tool that harvests credentials, ssh keys, cloud tokens, and environment secrets at scale.
Cloud Credentials Phishing Google Ads Target Aws Logins The honeypot, designed to mimic an employee’s aws login, encountered a sophisticated phishing page that only accepted the originally targeted victim’s email address, indicating potential personalization or filtering mechanisms. As victims submit their credentials, the phishing kit polls the attacker's server for instructions every few seconds, adapting the presented prompts to match the authentication stages of real google logins. With tools like wormgpt and fraudgpt available on the dark web, attackers now generate targeted phishing campaigns within minutes. these messages trick users into revealing cloud logins, especially for platforms like microsoft 365, google workspace, and aws iam. The operation is targeting next.js applications vulnerable to react2shell (cve 2025 55182) to gain initial access, then is deploying a multi phase credential harvesting tool that harvests credentials, ssh keys, cloud tokens, and environment secrets at scale.
Cloud Credentials Phishing Google Ads Target Aws Logins With tools like wormgpt and fraudgpt available on the dark web, attackers now generate targeted phishing campaigns within minutes. these messages trick users into revealing cloud logins, especially for platforms like microsoft 365, google workspace, and aws iam. The operation is targeting next.js applications vulnerable to react2shell (cve 2025 55182) to gain initial access, then is deploying a multi phase credential harvesting tool that harvests credentials, ssh keys, cloud tokens, and environment secrets at scale.
Comments are closed.