Cloud Computing Patterns Mechanisms Malware Hash Arcitura Patterns
Cloud Computing Patterns Mechanisms Malware Hash Arcitura Patterns Those programs have since evolved and grown, and the courses in those programs now contain the latest patterns related content. you can continue to access the current version of this content via the arcitura online elearning platform. In this research, malware attacks and the techniques for safeguarding against malware challenges in cloud computing architecture were analysed.
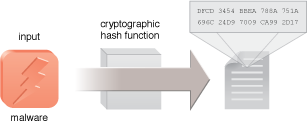
Cloud Computing Patterns Mechanisms Malware Hash Arcitura Patterns “the book provides a comprehensive and well researched guide to cloud computing. it covers a wide range of topics, from the basics of cloud computing to advanced archi tectural considerations. the book is written in a clear and concise style and is packed with valuable information and case studies. Cloud computing fundamentals describe cloud service models and cloud deployment types analogous to the nist cloud definition↗. these patterns extend this definition by covering the conditions under which a certain service model and deployment type should be used for a cloud application. In this paper we will use cloud services for deployment of cloud based antivirus and hash signatures and patterns will be used in intrusion detection system. we also propose a system for real time analysis on cloud for malware detection and prevention. Malware, which has become an ongoing danger to the security of information, is adapting and reconfiguring how it infiltrates and compromises cloud computing systems that could result in significant damage or data breaches.

Cloud Computing Patterns Mechanisms Arcitura Patterns In this paper we will use cloud services for deployment of cloud based antivirus and hash signatures and patterns will be used in intrusion detection system. we also propose a system for real time analysis on cloud for malware detection and prevention. Malware, which has become an ongoing danger to the security of information, is adapting and reconfiguring how it infiltrates and compromises cloud computing systems that could result in significant damage or data breaches. The field of cryptography and security in arxiv covers all areas of cryptography and security including authentication, public key cryptosytems, proof carrying code, etc. roughly it includes material in acm subject classes d.4.6 and e.3. paper digest team analyzes all papers published in this field in the past years, and presents up to 30 most influential papers for each year. this ranking. It summarizes the cloud computing patterns and covers the fundamental cloud computing architectural principles and the design of cloud applications using these patterns. It emphasizes the benefits and challenges of cloud computing, with a focus on security concerns related to malware threats. However, just like any other technology, cloud computing opens up many forms of security threats and problems. in this work, we focus on discussing different cloud models and cloud services, respectively.
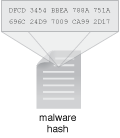
Cloud Computing Patterns Compound Patterns Cloud Balancing The field of cryptography and security in arxiv covers all areas of cryptography and security including authentication, public key cryptosytems, proof carrying code, etc. roughly it includes material in acm subject classes d.4.6 and e.3. paper digest team analyzes all papers published in this field in the past years, and presents up to 30 most influential papers for each year. this ranking. It summarizes the cloud computing patterns and covers the fundamental cloud computing architectural principles and the design of cloud applications using these patterns. It emphasizes the benefits and challenges of cloud computing, with a focus on security concerns related to malware threats. However, just like any other technology, cloud computing opens up many forms of security threats and problems. in this work, we focus on discussing different cloud models and cloud services, respectively.

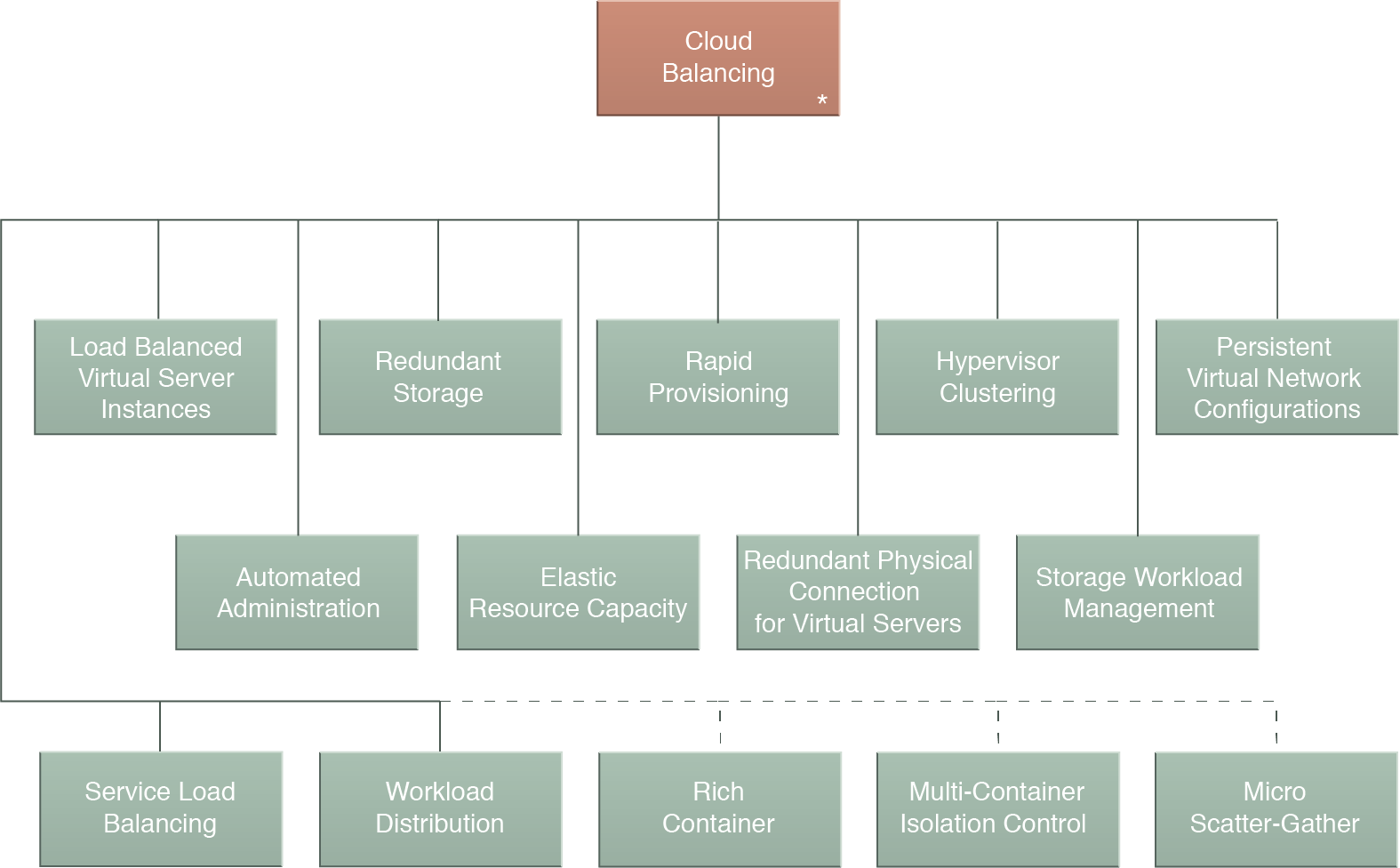
Cloud Computing Patterns Design Patterns Cloud Key Management It emphasizes the benefits and challenges of cloud computing, with a focus on security concerns related to malware threats. However, just like any other technology, cloud computing opens up many forms of security threats and problems. in this work, we focus on discussing different cloud models and cloud services, respectively.
Cloud Computing Patterns Design Patterns Cloud Authentication
Comments are closed.