Cloud Access Control Explained

Cloud Access Control Stealth Security Understand the fundamentals of cloud access control, including how to manage users, roles, and permissions to secure your business infrastructure effectively. If you want access control that survives audits and real attackers, you need to understand what dac, mac, and rbac are actually optimizing for —and what they inevitably trade away.

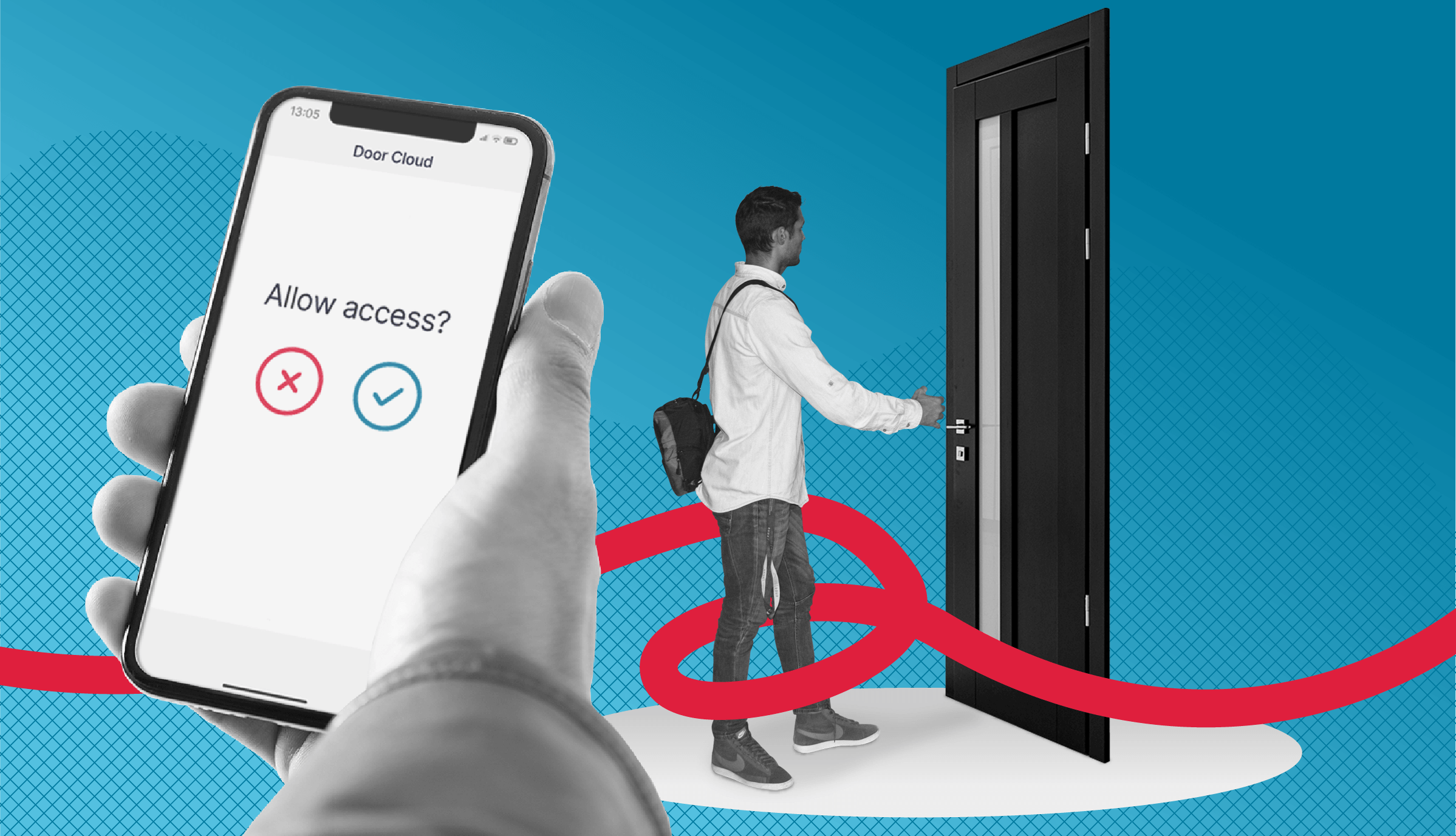
Cloud Access Control Jd Security A. cloud based access control is a modern solution that utilizes cloud resources to manage and control physical access to buildings, facilities, or areas. it centralizes the administration and security protocols, allowing for scalability, flexibility, and remote management of access permissions. What is cloud based access control? cloud based access control is a security system that uses cloud technology. it manages and controls entry to specific areas in a building. these systems use online servers to store and access data they don’t rely on local servers and hardware as usual. In this post, we will define cloud based access control, discuss the basics of how it works, outline the reasons why it is a better option than traditional access control, and compare key features of both systems. You can unlock doors from your smartphone, manage employee access across multiple sites, and receive instant alerts without bulky servers or complex wiring. this is the power of cloud based access control, a modern alternative to traditional keycard and pin systems.
Cloud Access Control Checklist Checklist Gg In this post, we will define cloud based access control, discuss the basics of how it works, outline the reasons why it is a better option than traditional access control, and compare key features of both systems. You can unlock doors from your smartphone, manage employee access across multiple sites, and receive instant alerts without bulky servers or complex wiring. this is the power of cloud based access control, a modern alternative to traditional keycard and pin systems. In this guide, we will explore how cloud based access control works, its benefits and challenges, and how you can implement it to safeguard your cloud environment. Learn how access control protects your workplace and ensures compliance. explore types, technologies, and tips for implementing access control. Explore access control in cloud security and how rbac is implemented across aws iam, azure rbac, and gcp iam in real environments. With cloud based access controls, businesses can reduce the risk of tampered documents by implementing stringent access and editing permissions. these controls ensure that only authorized personnel can modify sensitive documents, and any changes are tracked and logged, providing a clear audit trail.
What Is Cloud Access Control Spica In this guide, we will explore how cloud based access control works, its benefits and challenges, and how you can implement it to safeguard your cloud environment. Learn how access control protects your workplace and ensures compliance. explore types, technologies, and tips for implementing access control. Explore access control in cloud security and how rbac is implemented across aws iam, azure rbac, and gcp iam in real environments. With cloud based access controls, businesses can reduce the risk of tampered documents by implementing stringent access and editing permissions. these controls ensure that only authorized personnel can modify sensitive documents, and any changes are tracked and logged, providing a clear audit trail.

Cloudbased Access Control Cloud Based Access Control What Explore access control in cloud security and how rbac is implemented across aws iam, azure rbac, and gcp iam in real environments. With cloud based access controls, businesses can reduce the risk of tampered documents by implementing stringent access and editing permissions. these controls ensure that only authorized personnel can modify sensitive documents, and any changes are tracked and logged, providing a clear audit trail.
Comments are closed.