Closing The Kubernetes Threat Detection Gap

Closing The Gap Expanding Cyber Deterrence Cyber Threat Alliance In this video, we explore how cloud detection and response (cdr) within crowdstrike falcon® cloud security extends protection to kubernetes by analyzing api activity, identifying behavioral anomalies, and exposing malicious intent that would otherwise appear legitimate. Once workloads are live in kubernetes, static scanning and shift left controls aren’t enough. runtime is where real signals appear — unusual processes, unexpected network paths, identity.
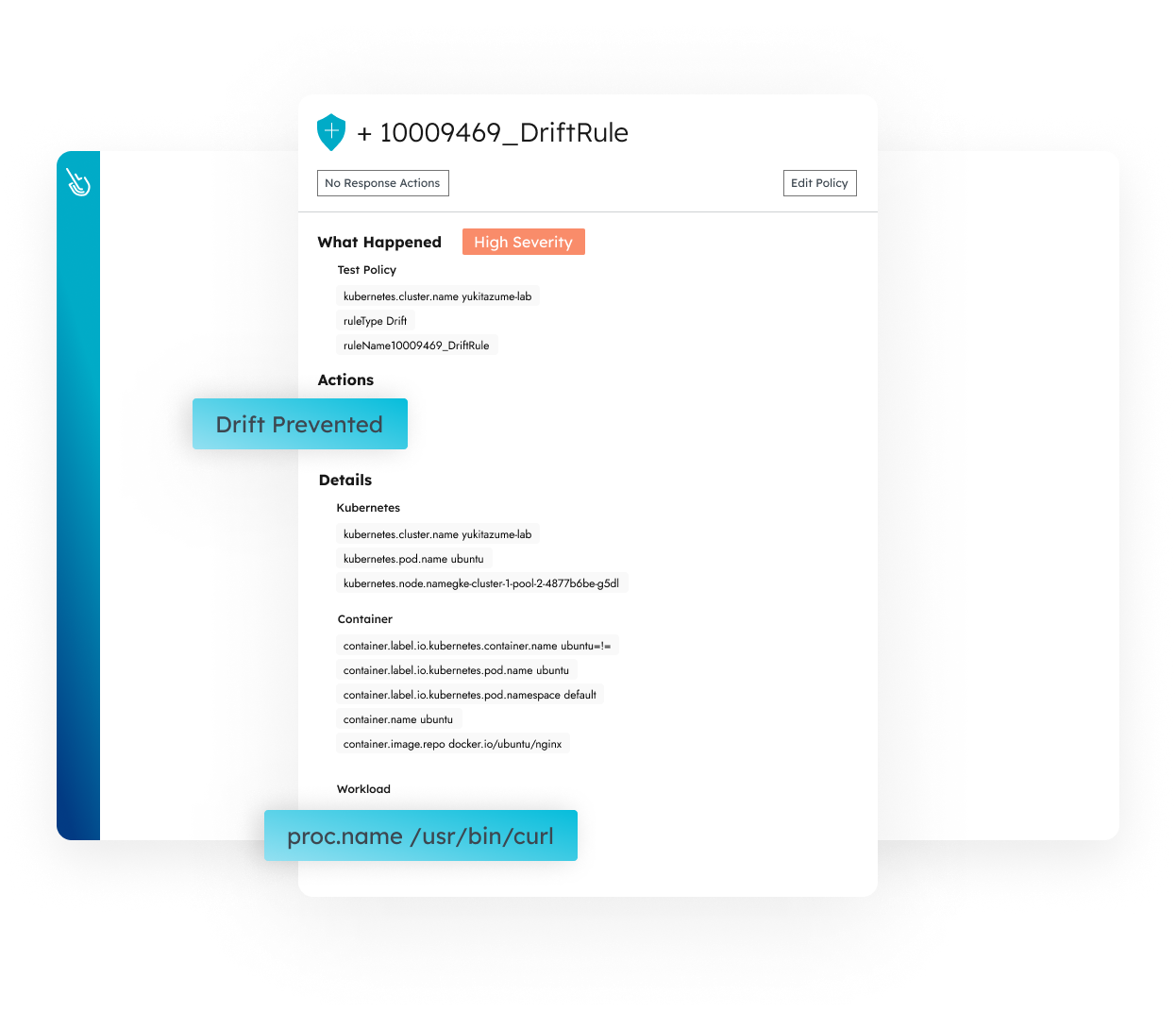
Server Threat Detection Tools Sysdig Struggling with kubernetes security blind spots? discover how ebpf drastically cut our threat detection time by 70% by providing deep, kernel level runtime visibility. As kubernetes powers cloud native and ai applications at scale, its control plane has become a critical and often overlooked security focus.see how crowdstri. The detection gap is the space between what your security tools are designed to detect and what attackers actually do. here's why it exists, why it's growing, and how an intelligent detection layer closes it. Strong posture comes from combining scanners, policy engines, runtime monitors, and network controls to close gaps across the cluster lifecycle.

Kubernetes Threat And Attack Detection Video Course Scanlibs The detection gap is the space between what your security tools are designed to detect and what attackers actually do. here's why it exists, why it's growing, and how an intelligent detection layer closes it. Strong posture comes from combining scanners, policy engines, runtime monitors, and network controls to close gaps across the cluster lifecycle. This paper presents a novel framework that combines real time multi class threat detection with adaptive deception to enhance kubernetes security. Are you sure you don't have any? 🔓 our field ciso tim chase explains why a unified data model isn't just a nice to have, it's the only way to truly detect, prioritize, and remediate risk across. If these return nothing for active endpoints, you’ve found a gap. close it at the collection stage — then your processing (detections, hunts) will actually work, and the whole loop finally turns. To secure kubernetes against attacks, defenders must implement validated settings, deep runtime visibility, and strictly limited permissions. these approaches help to transform kubernetes from a potential exposure point into a highly resilient and defensible platform.
Github Jatrost Awesome Kubernetes Threat Detection A Curated List Of This paper presents a novel framework that combines real time multi class threat detection with adaptive deception to enhance kubernetes security. Are you sure you don't have any? 🔓 our field ciso tim chase explains why a unified data model isn't just a nice to have, it's the only way to truly detect, prioritize, and remediate risk across. If these return nothing for active endpoints, you’ve found a gap. close it at the collection stage — then your processing (detections, hunts) will actually work, and the whole loop finally turns. To secure kubernetes against attacks, defenders must implement validated settings, deep runtime visibility, and strictly limited permissions. these approaches help to transform kubernetes from a potential exposure point into a highly resilient and defensible platform.
Comments are closed.