Closing Gaps With Browser Isolation
How Can Remote Browser Isolation Help Wwt With as much as 45 percent of cyberattacks now exploiting browser vulnerabilities, he argued that agencies must take browser isolation seriously if they hope to close critical gaps in their defenses. With up to 45% of cyberattacks exploiting browser vulnerabilities, he argued that isolation technology provides a vital safeguard.

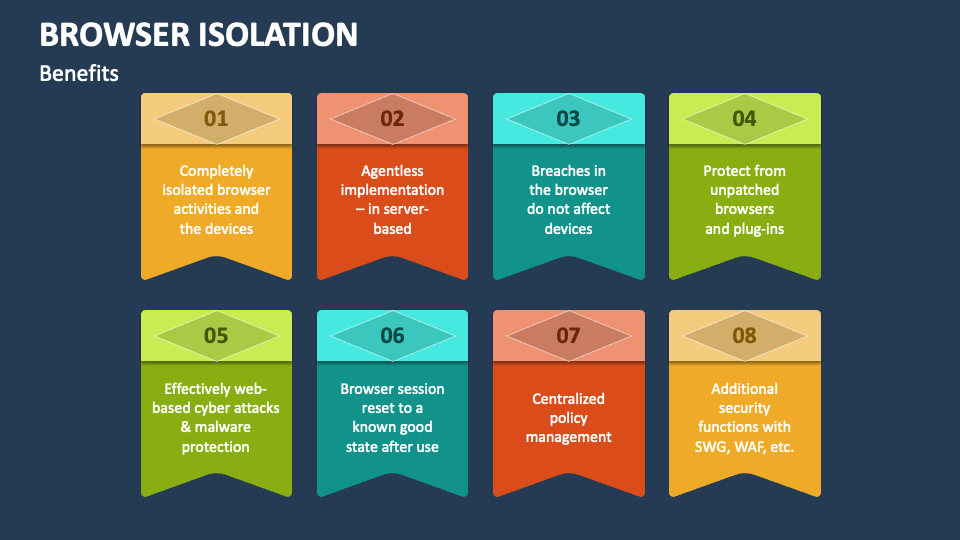
Closing Gaps With Browser Isolation In order to accomplish these goals, some organizations are turning to browser isolation, in which employee internet browsing is kept separate from local networks and infrastructure. It lets you plug in to a local or remote, even a headless browser, and fly it as if it's a normal browser. you can stream a remote browser with special cusotmizations to your clients to side step the restrictions of regular browsers. This guide describes the benefits of using isolation and the steps necessary for configuring zscaler internet access (zia) to add isolation to your security posture. Discover how browser isolation closes critical security gaps, reinforces zero trust, and protects enterprises from web based threats.
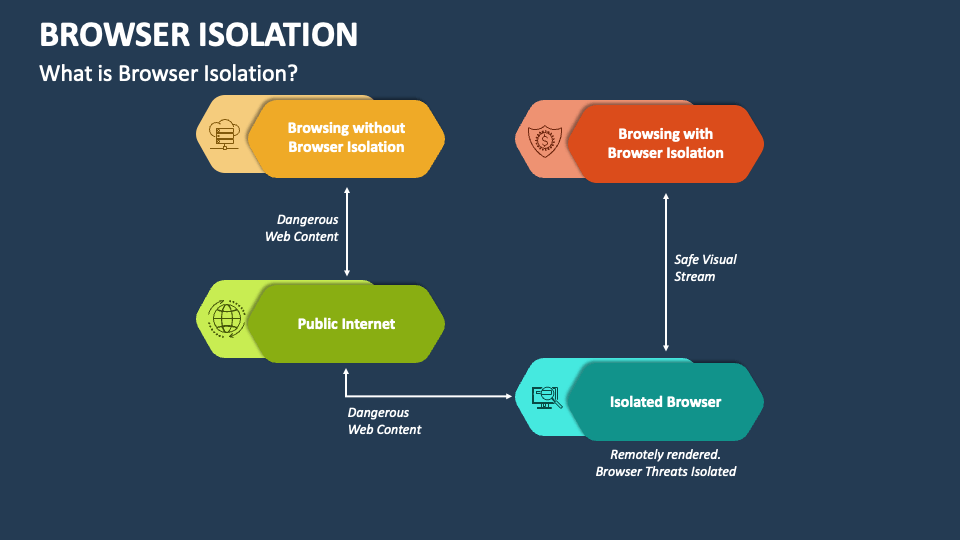
Browser Isolation Powerpoint And Google Slides Template Ppt Slides This guide describes the benefits of using isolation and the steps necessary for configuring zscaler internet access (zia) to add isolation to your security posture. Discover how browser isolation closes critical security gaps, reinforces zero trust, and protects enterprises from web based threats. Fortunately, there’s an effective solution to close this security gap: remote browser isolation (rbi), a cybersecurity technology that keeps you safe online while ensuring productivity is not disrupted. In this article, we’ll explore what is remote browser isolation, how it compares to conventional security methods, and why it’s becoming a foundational layer in zero trust strategies. Discover how isolating browsing activity helps to provide comprehensive protection against web based threats and malicious downloads. To achieve browser isolation, initially, the user sends a request to the general browser after which the request is forwarded to the isolated browser which creates a temporary login from where information is extracted and later on the login expires.
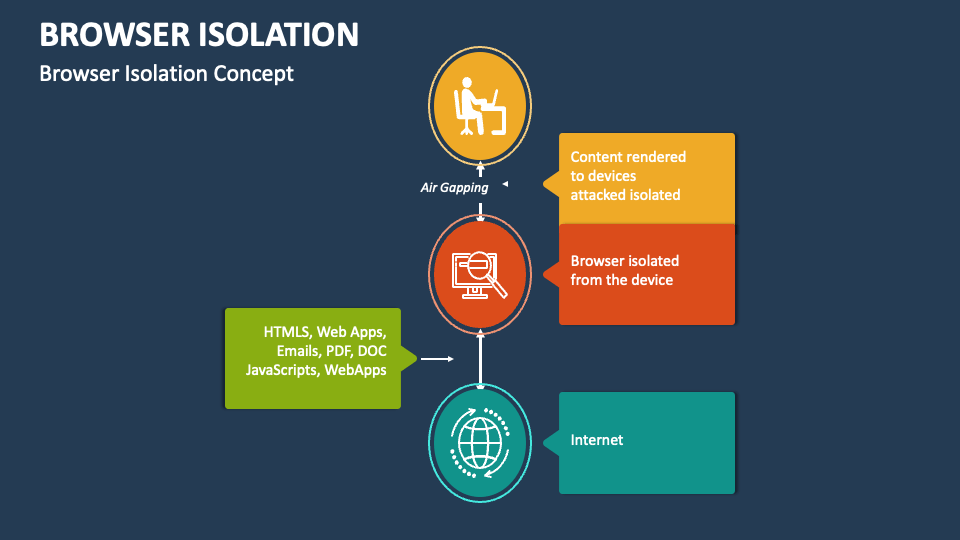
Browser Isolation Powerpoint And Google Slides Template Ppt Slides Fortunately, there’s an effective solution to close this security gap: remote browser isolation (rbi), a cybersecurity technology that keeps you safe online while ensuring productivity is not disrupted. In this article, we’ll explore what is remote browser isolation, how it compares to conventional security methods, and why it’s becoming a foundational layer in zero trust strategies. Discover how isolating browsing activity helps to provide comprehensive protection against web based threats and malicious downloads. To achieve browser isolation, initially, the user sends a request to the general browser after which the request is forwarded to the isolated browser which creates a temporary login from where information is extracted and later on the login expires.
Browser Isolation Powerpoint And Google Slides Template Ppt Slides Discover how isolating browsing activity helps to provide comprehensive protection against web based threats and malicious downloads. To achieve browser isolation, initially, the user sends a request to the general browser after which the request is forwarded to the isolated browser which creates a temporary login from where information is extracted and later on the login expires.

Remote Browser Isolation Rbi Solution
Comments are closed.