Clone Phishing
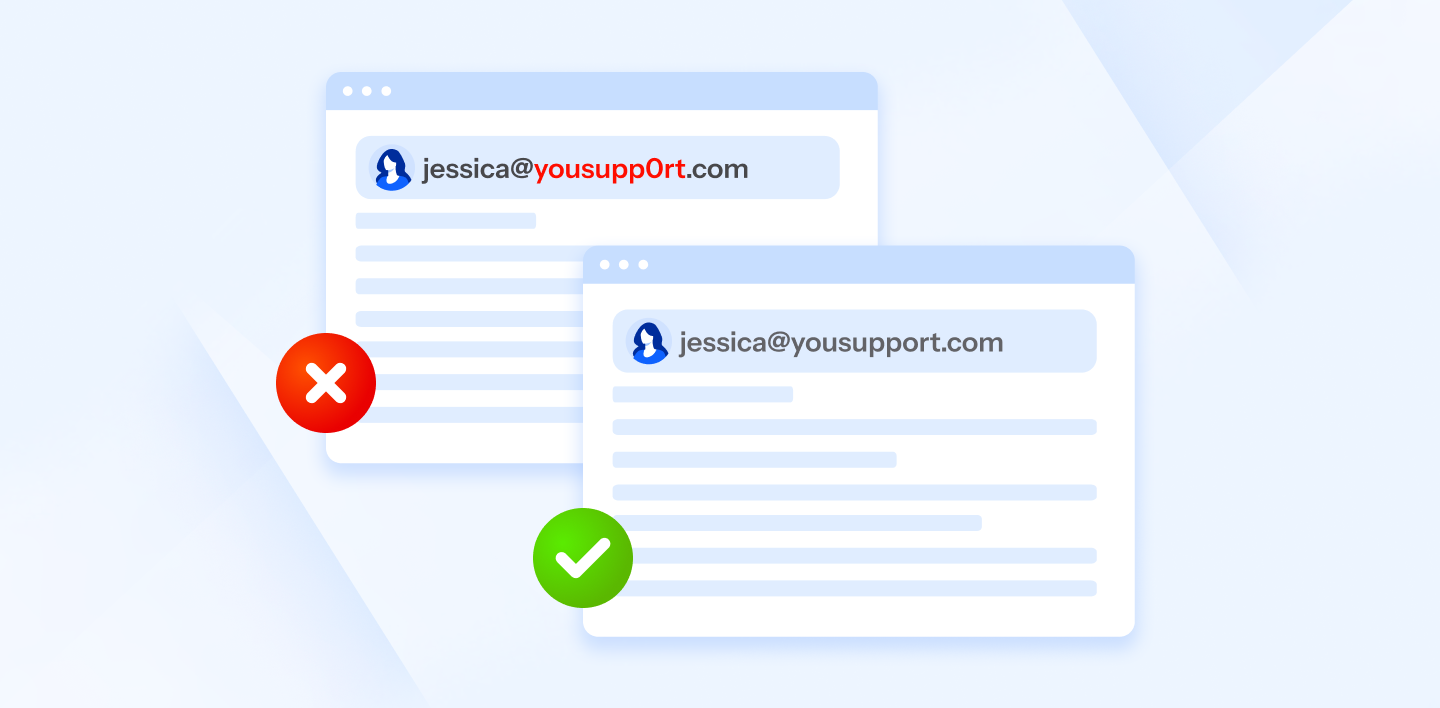
What Is Clone Phishing Internxt Blog What is clone phishing? clone phishing is an email based phishing attack, wherein attackers copy an authentic email that a recipient previously received and make minor changes to it by inserting fraudulent links or attachments. this is done to either deliver malware or harvest sensitive credentials. Clone phishing is a type of cyberattack in which the attacker clones or replicates a legitimate email to spread malware. hackers do this by intercepting the message and then modifying it before sending it to victims.

Clone Phishing Turns Trusted Emails Into Attacks Hoxhunt Clone phishing, similar to thread hijacking, is a newer type of email based threat where attackers clone a real email message with attachments and resend it pretending to be the original sender. Clone phishing involves a scammer adopting a person or brand’s identity to deceive a broad range of targets using replicated websites and communication channels. Clone phishing is a type of cyberattack in which perpetrators build a false website or email that closely mimics a real website or email from a reliable source in an effort to coerce consumers into disclosing important information. Clone phishing is a type of cyberattack in which perpetrators build a false website or email that closely mimics a real website or email from a reliable source in an effort to coerce consumers.

Clone Phishing Turns Trusted Emails Into Attacks Hoxhunt Clone phishing is a type of cyberattack in which perpetrators build a false website or email that closely mimics a real website or email from a reliable source in an effort to coerce consumers into disclosing important information. Clone phishing is a type of cyberattack in which perpetrators build a false website or email that closely mimics a real website or email from a reliable source in an effort to coerce consumers. Clone phishing is a deceptive cyber attack method that replicates legitimate emails or messages and modifies them to include malicious links or attachments. these emails are then sent from spoofed or compromised accounts, making them appear authentic. What is clone phishing, and how can you stop it? take a look at real life clone phishing examples and the top ways you can protect your business and customers. Clone phishing exploits familiarity and established trust. attackers intercept or replicate genuine emails—often routine communications like shipping notifications, subscription renewals, password resets, or invoice reminders—and recreate them with pixel perfect accuracy. the malicious version substitutes legitimate links with phishing urls or replaces safe attachments with malware laden. Clone phishing is a cyberattack where attackers duplicate legitimate emails or websites to deceive recipients into revealing sensitive information or installing malware. this method poses significant risks across financial, operational, and reputational domains.

What Is Clone Phishing How Scammers Mimic People You Trust Clone phishing is a deceptive cyber attack method that replicates legitimate emails or messages and modifies them to include malicious links or attachments. these emails are then sent from spoofed or compromised accounts, making them appear authentic. What is clone phishing, and how can you stop it? take a look at real life clone phishing examples and the top ways you can protect your business and customers. Clone phishing exploits familiarity and established trust. attackers intercept or replicate genuine emails—often routine communications like shipping notifications, subscription renewals, password resets, or invoice reminders—and recreate them with pixel perfect accuracy. the malicious version substitutes legitimate links with phishing urls or replaces safe attachments with malware laden. Clone phishing is a cyberattack where attackers duplicate legitimate emails or websites to deceive recipients into revealing sensitive information or installing malware. this method poses significant risks across financial, operational, and reputational domains.
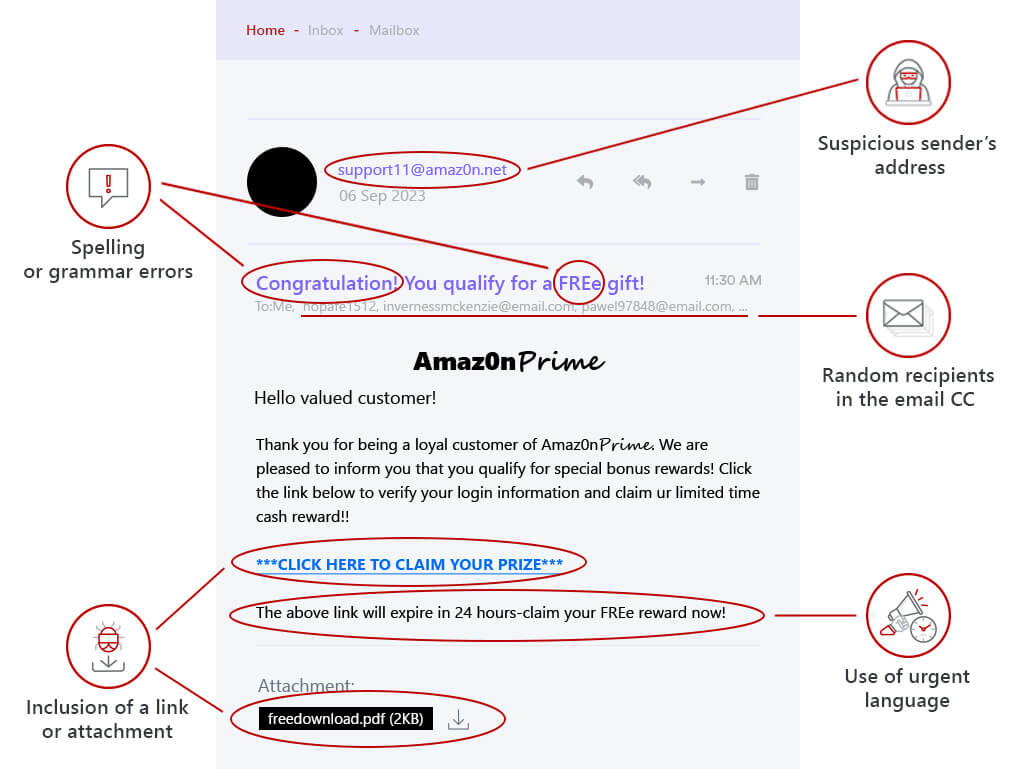
What Is Clone Phishing How Scammers Mimic People You Trust Clone phishing exploits familiarity and established trust. attackers intercept or replicate genuine emails—often routine communications like shipping notifications, subscription renewals, password resets, or invoice reminders—and recreate them with pixel perfect accuracy. the malicious version substitutes legitimate links with phishing urls or replaces safe attachments with malware laden. Clone phishing is a cyberattack where attackers duplicate legitimate emails or websites to deceive recipients into revealing sensitive information or installing malware. this method poses significant risks across financial, operational, and reputational domains.
Comments are closed.