Client Credentials Grant Flow Is Really Bad
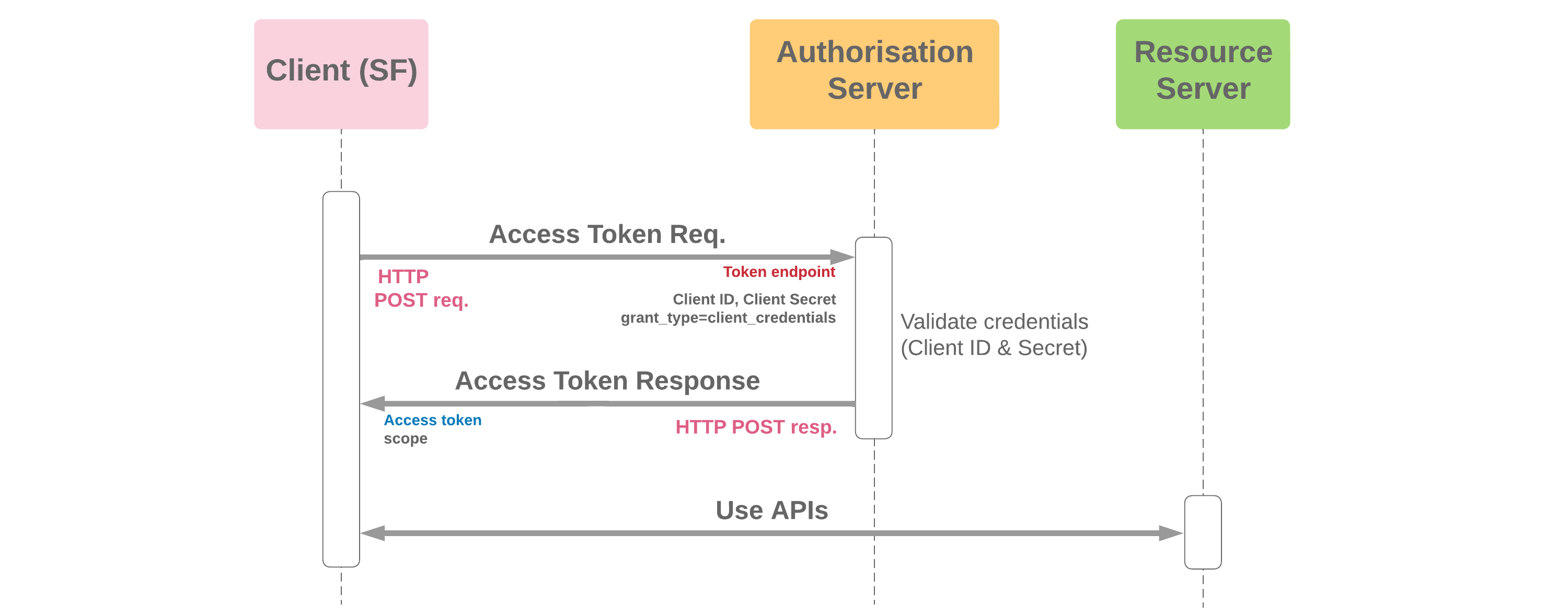
Client Credentials Grant Flow Cloud Sundial In the client credentials flow, permissions are granted directly to the application itself by an administrator. when the app presents a token to a resource, the resource enforces that the app itself has authorization to perform an action since there is no user involved in the authentication. While many oauth flows involve a human user granting consent, certain scenarios — such as machine to machine (m2m) or service account integrations — require authentication without user.

A Detailed Overview Of Client Credentials Flow In this piece, we explore why using the oauth client credentials flow which is built for confidential, server side apps in mobile, native, and thick client applications is inherently unsafe. we break down the technical reasons behind these risks and illustrate how attackers might exploit them. This article focuses on how to monitor oauth 2.0 client credentials flows end to end; from token issuance to authenticated api calls, so devops teams can detect failures early, isolate root causes faster, and maintain reliable integrations. In the client credentials flow, permissions are granted directly to the application itself by an administrator. when the app presents a token to a resource, the resource enforces that the app itself has authorization to perform an action since there is no user involved in the authentication. This grant is similar to the resource owner credentials grant except only the client’s credentials are used to authenticate a request for an access token. again this grant should only be allowed to be used by trusted clients.
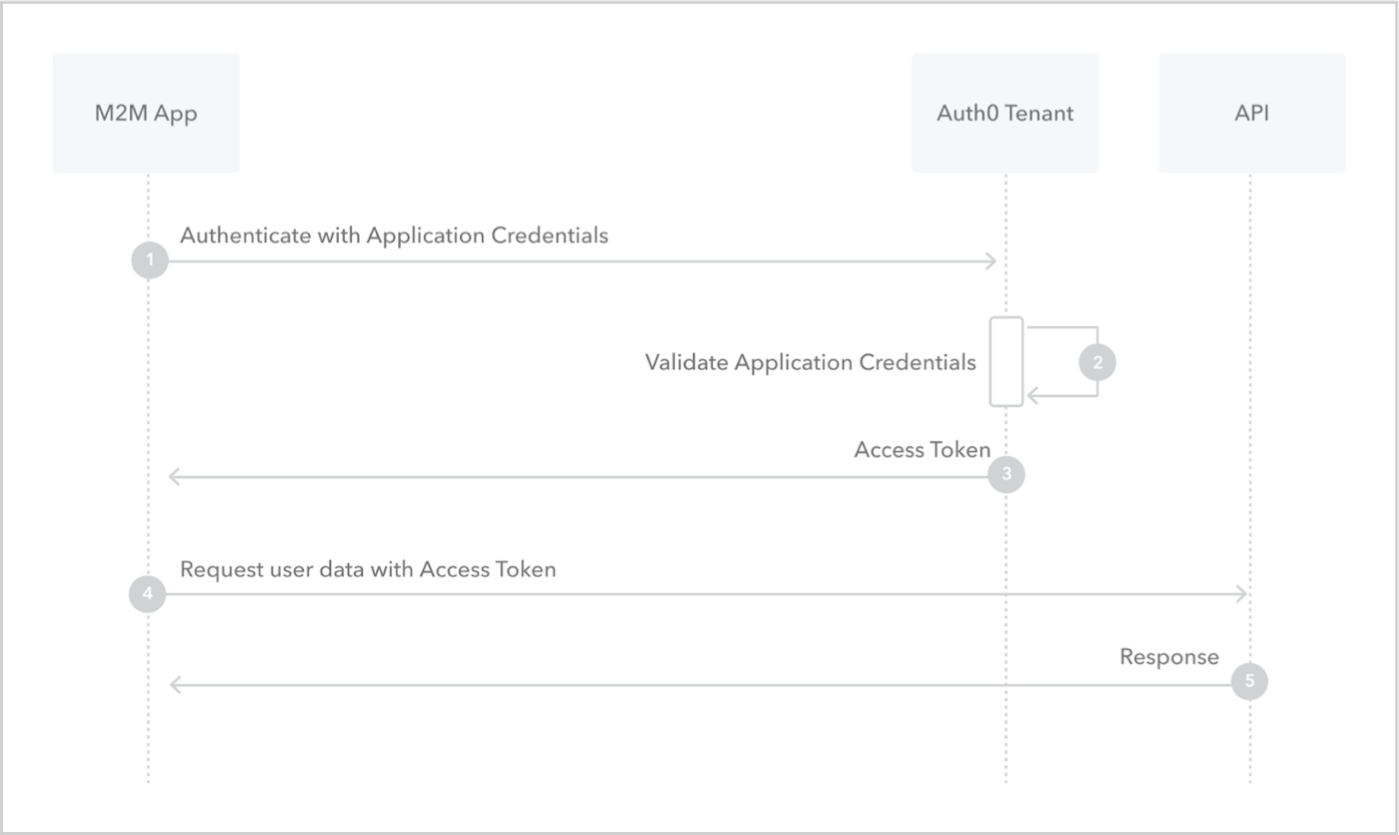
Client Credentials Grant Authentication Flow In the client credentials flow, permissions are granted directly to the application itself by an administrator. when the app presents a token to a resource, the resource enforces that the app itself has authorization to perform an action since there is no user involved in the authentication. This grant is similar to the resource owner credentials grant except only the client’s credentials are used to authenticate a request for an access token. again this grant should only be allowed to be used by trusted clients. Learn how the client credentials flow works and why you should use it for machine to machine (m2m) applications. Public clients can’t be trusted to identify themselves using client authentication, so that would not be a good candidate for client credentials grant flow. the following image shows an outline of the flow:. This guide breaks down how the flow works, when to use it, how to implement it securely, and the trade offs to be aware of. it also covers the flow’s practical use cases and implementation with node.js examples while showing its internal structure. Oauth 2.0 offers multiple grant types for different authentication scenarios, but choosing the wrong flow can create security vulnerabilities or poor user experiences.
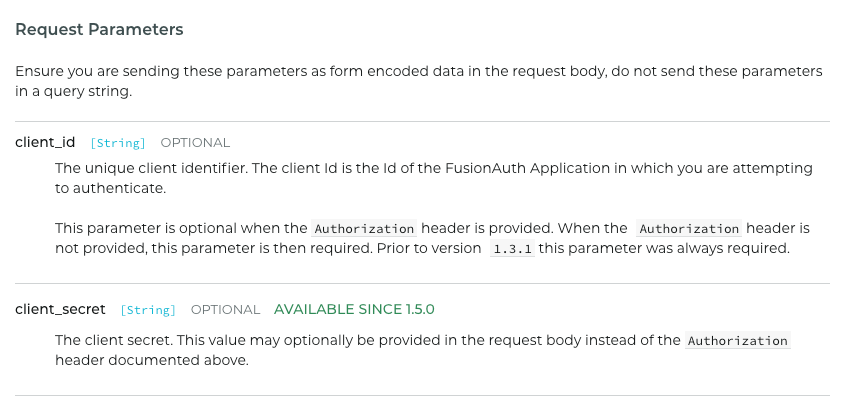
Client Credentials Grant Flow Basic Auth Or Client Id And Client Learn how the client credentials flow works and why you should use it for machine to machine (m2m) applications. Public clients can’t be trusted to identify themselves using client authentication, so that would not be a good candidate for client credentials grant flow. the following image shows an outline of the flow:. This guide breaks down how the flow works, when to use it, how to implement it securely, and the trade offs to be aware of. it also covers the flow’s practical use cases and implementation with node.js examples while showing its internal structure. Oauth 2.0 offers multiple grant types for different authentication scenarios, but choosing the wrong flow can create security vulnerabilities or poor user experiences.
Client Credentials Flow This guide breaks down how the flow works, when to use it, how to implement it securely, and the trade offs to be aware of. it also covers the flow’s practical use cases and implementation with node.js examples while showing its internal structure. Oauth 2.0 offers multiple grant types for different authentication scenarios, but choosing the wrong flow can create security vulnerabilities or poor user experiences.
Client Credentials Flow
Comments are closed.