Clickfix Attack Uses Steganography To Hide Malicious Code In Fake
Clickfix Malware Tricks You Into Infecting Your Own Windows Pc Fox News A new wave of clickfix attacks is abusing highly realistic fake windows update screens and png image steganography to secretly deploy infostealing malware such as lummac2 and rhadamanthys on victim systems. Clickfix attack variants have been observed where threat actors trick users with a realistic looking windows update animation in a full screen browser page and hide the malicious code.

Clickfix Exploits Users With Fake Errors And Malicious Code Huntress uncovered an attack utilizing a clickfix lure to initiate a multi stage malware execution chain. this analysis reveals how threat actors use steganography to conceal infostealers like lummac2 and rhadamanthys within seemingly harmless pngs. Clickfix just got more convincing, hiding malware in png images and faking windows updates to make users run dangerous commands. Clickfix is a social engineering family of attacks that tricks victims into copying and pasting commands into os dialogs or terminals, thereby executing attacker supplied code with their own privileges. Threat actors are using a twist on the clickfix attack model, in this case hiding the malicious code they want victims to download in a convincing – but fake – windows update screen, complete with white lettering against a bright blue background.

Clickfix Fake Error Message Malware Spikes Over 500 Takes Second Clickfix is a social engineering family of attacks that tricks victims into copying and pasting commands into os dialogs or terminals, thereby executing attacker supplied code with their own privileges. Threat actors are using a twist on the clickfix attack model, in this case hiding the malicious code they want victims to download in a convincing – but fake – windows update screen, complete with white lettering against a bright blue background. A typical clickfix attack begins with threat actors using phishing emails, malvertisements, or compromised websites to lead unsuspecting users to a visual lure—usually a landing page—and trick them into executing a malicious command themselves. The latest tactics of this campaign include steganography — hiding malware in the pixels of an image — and a “highly convincing” fake windows update screen that asks the user to open a run. Cybersecurity researchers at huntress have uncovered a sophisticated clickfix campaign that leverages steganography to conceal malicious code within png images disguised as windows update screens. A brand new wave of clickfix assaults is abusing extremely lifelike pretend home windows replace screens and png picture steganography to secretly deploy infostealing malware akin to lummac2 and rhadamanthys on sufferer methods.
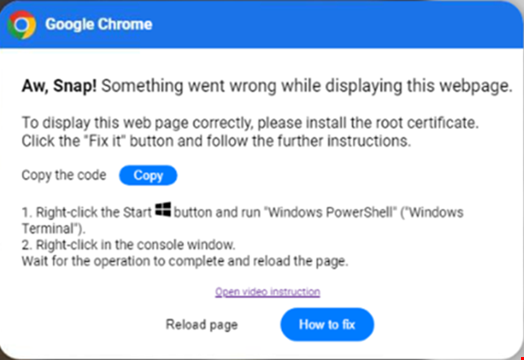
Clickfix Cyber Attacks For Malware Deployment On The Rise A typical clickfix attack begins with threat actors using phishing emails, malvertisements, or compromised websites to lead unsuspecting users to a visual lure—usually a landing page—and trick them into executing a malicious command themselves. The latest tactics of this campaign include steganography — hiding malware in the pixels of an image — and a “highly convincing” fake windows update screen that asks the user to open a run. Cybersecurity researchers at huntress have uncovered a sophisticated clickfix campaign that leverages steganography to conceal malicious code within png images disguised as windows update screens. A brand new wave of clickfix assaults is abusing extremely lifelike pretend home windows replace screens and png picture steganography to secretly deploy infostealing malware akin to lummac2 and rhadamanthys on sufferer methods.
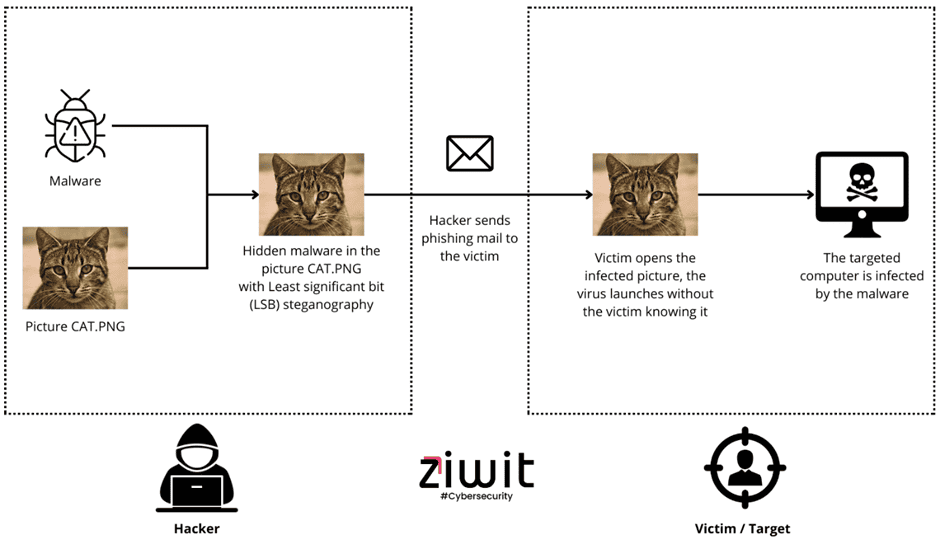
Beyond The Click Clickfix Meets Steganography Stripe Olt Cybersecurity researchers at huntress have uncovered a sophisticated clickfix campaign that leverages steganography to conceal malicious code within png images disguised as windows update screens. A brand new wave of clickfix assaults is abusing extremely lifelike pretend home windows replace screens and png picture steganography to secretly deploy infostealing malware akin to lummac2 and rhadamanthys on sufferer methods.
Comments are closed.