Clickfix Attack Uses Fake Windows Update Screen To Push Malware Blade

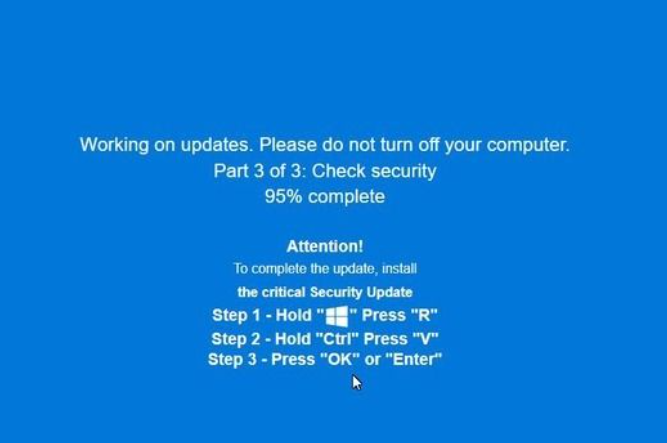
Clickfix Campaign Now Uses Fake Windows Updates To Spread Malware Fox Clickfix attack variants have been observed where threat actors trick users with a realistic looking windows update animation in a full screen browser page and hide the malicious code. Several researchers have flagged a new development in the ongoing clickfix campaign: attackers are now mimicking a windows update screen to trick people into running malware.
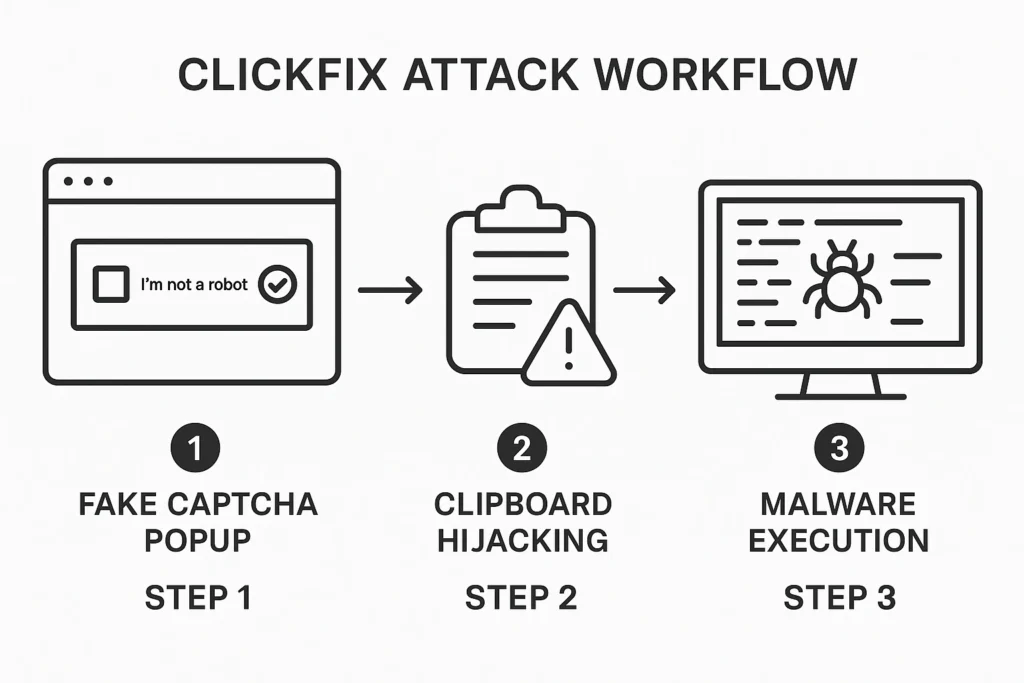
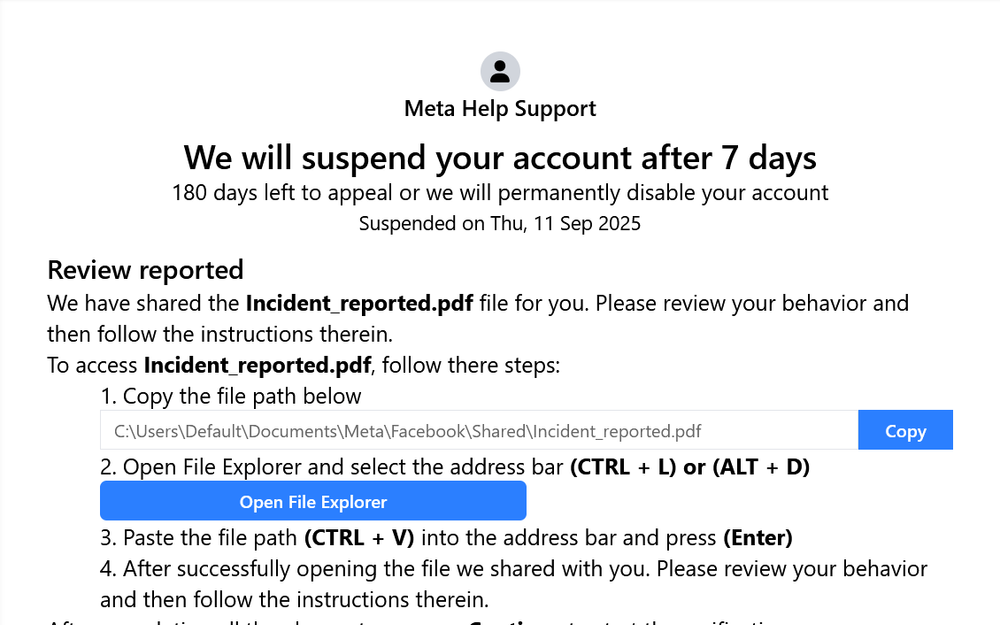
Clickfix The New Social Engineering Trick Hackers Are Using To Infect Because clickfix relies on human intervention to launch the malicious commands, a campaign that uses this technique could get past conventional and automated security solutions. A new wave of clickfix attacks is abusing highly realistic fake windows update screens and png image steganography to secretly deploy infostealing malware such as lummac2 and rhadamanthys on victim systems. The latest clickfix attack creates a fake, full screen windows os update through the browser to try and dupe the user into executing a malicious command. michael kan. Experts have been warning about clickfix attacks (sometimes called pastejacking) since at least early 2024. they often start with a phishing lure that pulls the victim to a realistic fake.
Warning Issued As Clickfix Attacks Re Emerge Using Fake Windows Update The latest clickfix attack creates a fake, full screen windows os update through the browser to try and dupe the user into executing a malicious command. michael kan. Experts have been warning about clickfix attacks (sometimes called pastejacking) since at least early 2024. they often start with a phishing lure that pulls the victim to a realistic fake. A new clickfix tactic uses a convincing windows update screen to trick you into running malware with a single copied command. First spotted in october, the latest clickfix campaigns force the browser into full screen mode and display what appears to be a standard blue windows update page — complete with progress messages and the familiar “working on updates” animation. Summary: new clickfix variants use full screen fake windows update pages to trick users into executing attacker controlled cmd commands. payloads (lummac2, rhadamanthys) are hidden inside png pixel data via steganography and reconstructed in memory using powershell a stego loader. The latest twist comes from the ongoing clickfix campaign. instead of asking you to prove you are human, attackers now disguise themselves as a windows update.
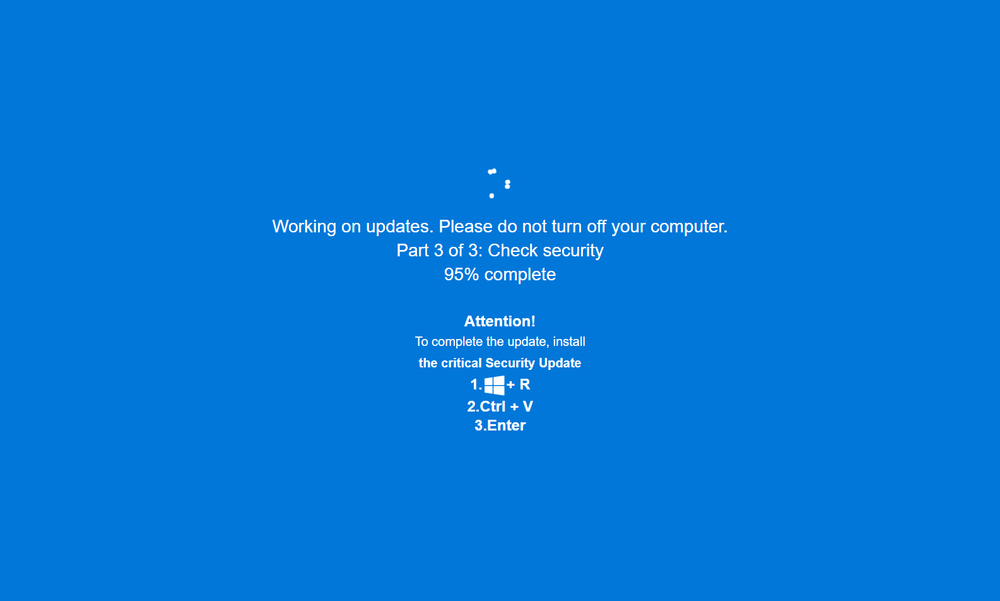
Fake Adult Websites Pop Realistic Windows Update Screen To Deliver A new clickfix tactic uses a convincing windows update screen to trick you into running malware with a single copied command. First spotted in october, the latest clickfix campaigns force the browser into full screen mode and display what appears to be a standard blue windows update page — complete with progress messages and the familiar “working on updates” animation. Summary: new clickfix variants use full screen fake windows update pages to trick users into executing attacker controlled cmd commands. payloads (lummac2, rhadamanthys) are hidden inside png pixel data via steganography and reconstructed in memory using powershell a stego loader. The latest twist comes from the ongoing clickfix campaign. instead of asking you to prove you are human, attackers now disguise themselves as a windows update.
Fake Adult Websites Pop Realistic Windows Update Screen To Deliver Summary: new clickfix variants use full screen fake windows update pages to trick users into executing attacker controlled cmd commands. payloads (lummac2, rhadamanthys) are hidden inside png pixel data via steganography and reconstructed in memory using powershell a stego loader. The latest twist comes from the ongoing clickfix campaign. instead of asking you to prove you are human, attackers now disguise themselves as a windows update.
New Clickfix Wave Infects Users With Hidden Malware In Images And Fake
Comments are closed.