Cissp Cots Software Development Security

Cissp Domain 8 Software Development Security Pdf In this video, i have explained how cots integrated with risk management. i have covered the cissp cots section with software assurance security important links more. Explore cissp domain 8 software development security. learn secure coding practices, sdlc, and new 2025 updates to prep for the cissp exam.

Cissp Cots Software Development Security Education Marthoma Understanding the shared responsibility model is important for infosec professionals. quality: does it do what it’s supposed to do?. When you install a cots application, you're shifting part of your trust boundary outside your organization. you're now trusting not only the product but also the vendor’s entire supply chain. so how do you assess this kind of risk? you start by demanding transparency. This section addresses the implementation of appropriate security controls across all components of a software development environment—from code to deployment infrastructure—to ensure software is developed, tested, and delivered securely. This guide will break down the key concepts of the cissp software development security domain, from development methodologies to security testing, providing a clear roadmap for your studies.
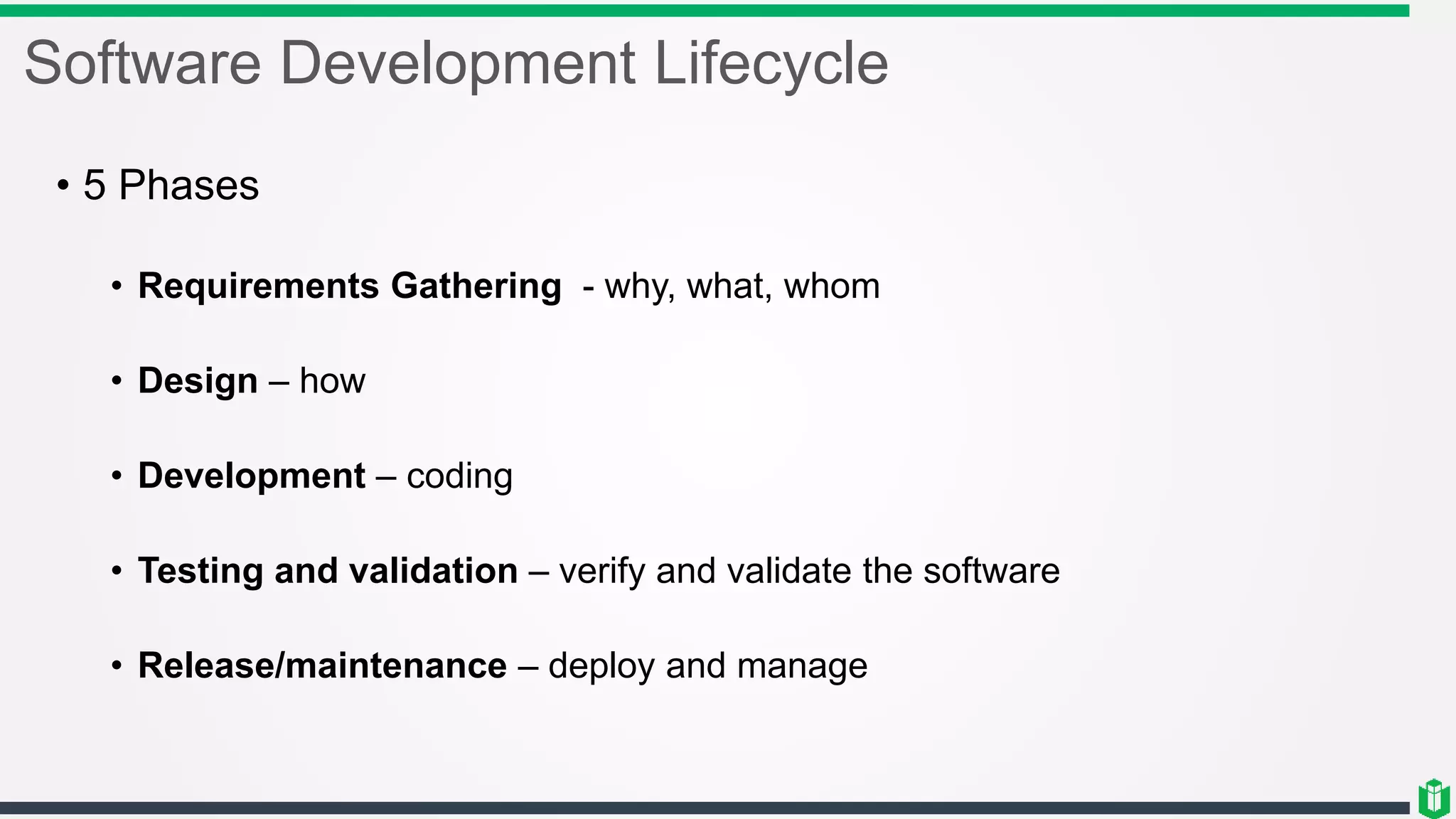
Cissp Software Development Security Pptx This section addresses the implementation of appropriate security controls across all components of a software development environment—from code to deployment infrastructure—to ensure software is developed, tested, and delivered securely. This guide will break down the key concepts of the cissp software development security domain, from development methodologies to security testing, providing a clear roadmap for your studies. Cissp domain 8 short notes: software development security explained for exam preparation and real world application, covering secure software lifecycle practices, resilient applications,. Welcome to my 21 part series on the takeaways and crucial points from each chapter in the isc2 cissp official study guide. to be clear, this isn’t a replacement for all those other study methods i mentioned above. this is just a supplement. this also isn’t everything you need to know for the test. Software defined security (sds or sdsec): a security model in which security functions such as firewalling, ids ips, and network segmentation are implemented in software within an sdn environment. This course examines the need to provide security throughout the sdlc, which aligns with domain 8 on the cissp exam. we will compare and contrast agile and the waterfall methodologies, and look at the assessment of web applications and more traditional applications.

Cissp Software Development Security Cissp domain 8 short notes: software development security explained for exam preparation and real world application, covering secure software lifecycle practices, resilient applications,. Welcome to my 21 part series on the takeaways and crucial points from each chapter in the isc2 cissp official study guide. to be clear, this isn’t a replacement for all those other study methods i mentioned above. this is just a supplement. this also isn’t everything you need to know for the test. Software defined security (sds or sdsec): a security model in which security functions such as firewalling, ids ips, and network segmentation are implemented in software within an sdn environment. This course examines the need to provide security throughout the sdlc, which aligns with domain 8 on the cissp exam. we will compare and contrast agile and the waterfall methodologies, and look at the assessment of web applications and more traditional applications.

Software Development Security Question Cissp Course Practice Test Software defined security (sds or sdsec): a security model in which security functions such as firewalling, ids ips, and network segmentation are implemented in software within an sdn environment. This course examines the need to provide security throughout the sdlc, which aligns with domain 8 on the cissp exam. we will compare and contrast agile and the waterfall methodologies, and look at the assessment of web applications and more traditional applications.
Comments are closed.