Cis 3 Continuous Vulnerability Management
Continuous Vulnerability Management Securelymanaged A number of dashboards, reports, and assurance report cards (arc) are readily available to provide organizations with real time continuous vulnerability monitoring and reporting, such as the cis control 3 18 continuous vulnerability management and application security dashboard. Cis control 3: continuous vulnerability management continuously acquire, assess, and take action on new information in order to identify vulnerabilities, remediate, and minimize the window of opportunity for attackers.
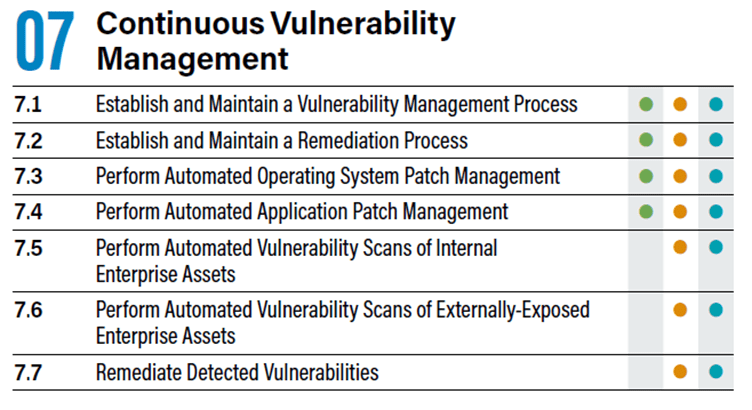
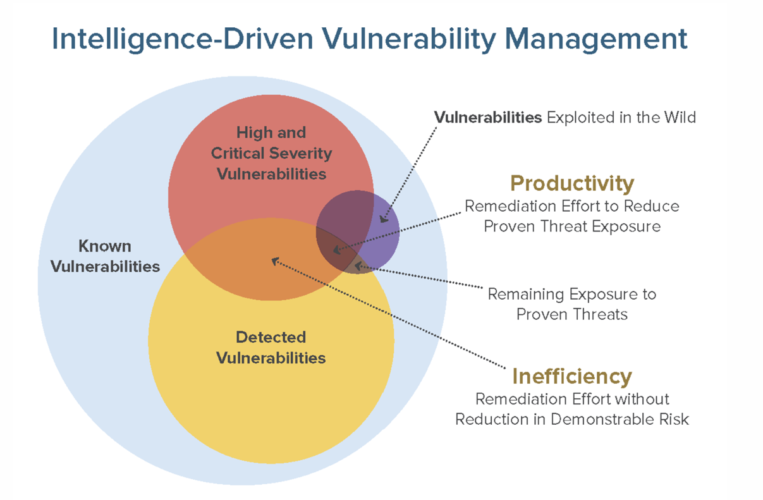
Cis Control 7 Continuous Vulnerability Management Incident Response This week, i will be walking you through the third critical control: continuous vulnerability management. specifically, we will be looking at why vulnerability management and remediation is important for your overall security maturity, what the control consists of, and how to implement it. Develop a plan to continuously assess and track vulnerabilities on all enterprise assets within the enterprise’s infrastructure, in order to remediate, and minimize, the window of opportunity for attackers. monitor public and private industry sources for new threat and vulnerability information. This dashboard will focus on control 3 (continuous vulnerability management) and control 18 (application software security). historically cis has referred the first six cis controls as cyber hygiene, which focuses on an organization’s cybersecurity activities. Understanding and managing vulnerabilities is a continuous activity, requiring focus of time, attention, and resources. attackers have access to the same information and can often take advantage of vulnerabilities more quickly than an enterprise can remediate.

Cis 7 Continuous Vulnerability Management Colorado Hi Tech Solutions This dashboard will focus on control 3 (continuous vulnerability management) and control 18 (application software security). historically cis has referred the first six cis controls as cyber hygiene, which focuses on an organization’s cybersecurity activities. Understanding and managing vulnerabilities is a continuous activity, requiring focus of time, attention, and resources. attackers have access to the same information and can often take advantage of vulnerabilities more quickly than an enterprise can remediate. Continuously acquire, assess, and take action on new information in order to identify vulnerabilities, remediate, and minimize the window of opportunity for attackers. Cis control 3: continuous vulnerability management the focus of this control is to have an established vulnerability management program that is con figured to conduct regular, comprehensive, credentialed scans across the organization. Utilize an up to date security content automation protocol (scap) compliant vulnerability scanning tool to automatically scan all systems on the network on a weekly or more frequent basis to identify all potential vulnerabilities on the organization’s systems. The table of contents below and in the sidebar should let you easily access the documentation for your topic of interest. you can also use the search function in the top left corner. the main documentation for the site is organized into sections for each individual cis control.
Comments are closed.