Cia Cyber Security Pdf

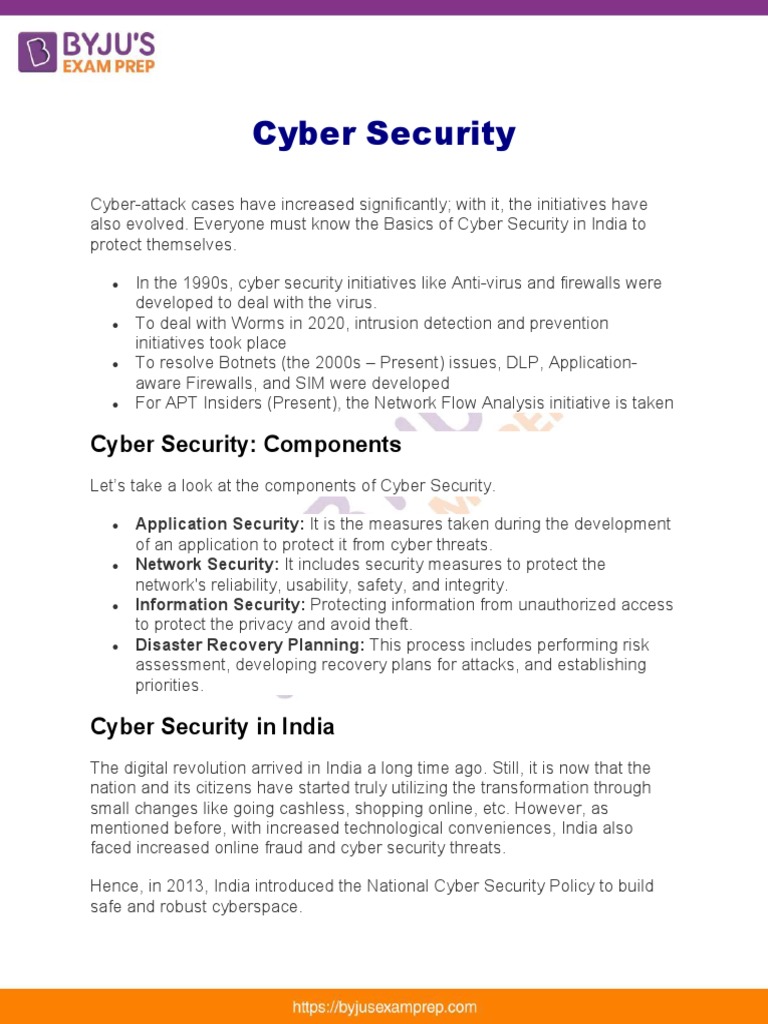
Cia Cyber Security Pdf Real world applications of the cia triad how each element of the cia triad applies to everyday cybersecurity practices. examples of tools and methods (encryption, hashing, backups) for each cia triad principle. thank you! questions?. It is a discipline to protect data, hardware, software, and networked systems from cyber attackers and malicious users. it’s a risk that can harm a computer system or network, making it partially or completely unavailable, or compromise the confidentiality and integrity of data.

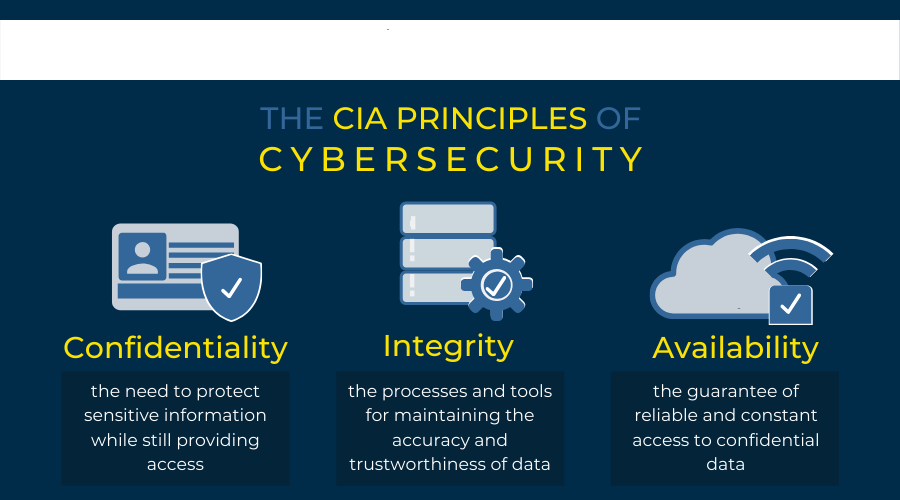
Cyber Security Pdf Cyber threats cyber warfare: cyber warfare refers to the use of digital attacks like computer viruses and hacking by one country to disrupt the vital computer systems of another, with the aim of creating damage, death and destruction. Triad of the cia free download as word doc (.doc .docx), pdf file (.pdf), text file (.txt) or read online for free. the document discusses the triad of cybersecurity known as cia (confidentiality, integrity, availability). This paper delves into the intricate tapestry of information security in network systems, scrutinizing the quintessential "cia triad" confidentiality, integrity, and availability through the. This paper reviews the history of the cia (confidentiality, integrity and availability) triad from the perspectives of information security practitioners and scholars.

Cia Triad In Cyber Security Definition Examples Importance Urity teams use the cia triad to develop security measures. the cia security triangle shows the fundamental g. als that must be included in information security measures. the cia triad serves as a tool or guide for securing inform. The cia triad has long been a foundational model in information security, and this review evaluates how each component contributes to protecting systems against evolving cyber threats. For cybersecurity professionals, a deep understanding of the cia triad is essential. protecting data requires balancing confidentiality, integrity, and availability—neglecting even one aspect can create serious vulnerabilities. Transparency was critical. to keep everyone connected and informed, we developed a fort nightly update for all agency heads, along with the national security council, homeland security council, and ofice of management and budget.

Cia Triad And Cybersecurity Roles Pdf Information Security Security

Cyber Security Pdf

Cyber Security Download Free Pdf Security Computer Security
Cyber Security Pdf Docdroid

Cyber Security Pdf Pdf Computer Security Security

Cyber Security Pdf Malware Information Technology

Cia Pdf
Cybersecurity Integrity Cia Match Up

Confidentiality Integrity And Availability Cia In Cybersecurity

Cyber Security Pdf Pdf

Cyber Security Pdf Malware Security

Cyber Security By Cisco Academy Pdf Security Computer Security
Cyber Security Cia Let S Tech It Easy

Confidentiality Integrity And Availability Cia In Cyber Security

Cyber Security Pdf

Cyber Security Cit Pdf Computer Virus Malware

Cia Blockchain Pdf Computer Network Computer Security

Cyber Security Pdf Download Free Pdf Security Computer Security

Cyber Security Pdf Security Computer Security

Cia Pdf Security Computer Security
The Importance Of The Cia Triad In Information Security 9spheres

Confidentiality Integrity And Availability Cia In Cyber Security

Cybersecurity Pdf Computer Security Security

Cyber Security Pdf Security Computer Security

Cia Notes Pdf Security Computer Security

Cia Cybersecurity The Cia Triad For Protecting Information

Confidentiality Integrity And Availability Cia In Cyber Security
Cyber Security Pdf Security Computer Security

Cyber Security Download Free Pdf Security Computer Security

It Cia Pdf Cybercrime Security

What Is Cia In Cyber Security
Github Cyberalbsecop Cybersecurity Pdf Vault A Comprehensive
Comments are closed.