Chpter 2 Computer Network Pdf Transport Layer Security

Transport Layer Security Tls A Network Security P Pdf Transport Chpter 2 computer network free download as pdf file (.pdf), text file (.txt) or read online for free. When sender’s retransmit timer expires, two indistinguishable cases (why?): in latter case, duplicate data packet reaches receiver! how to prevent receiver from passing duplicates to application? how many tombstones must receiver store? also should cover layer 3 source and destination!.

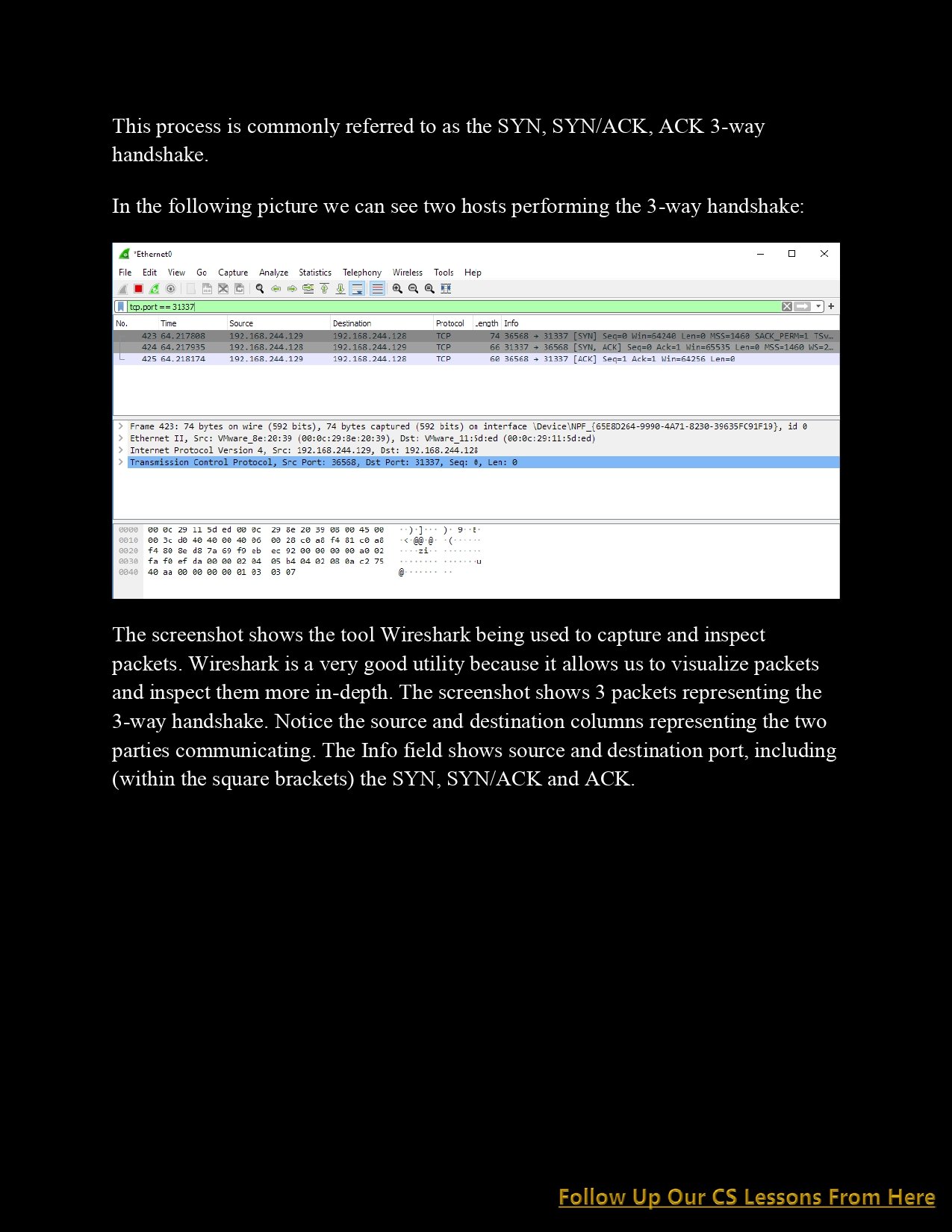
Lecture 22 32 Network Layer Computer Networks Part 4 Pdf Internet The transport layer provides transparent transfer of data between hosts. it provides end to end control and information transfer with the quality of service needed by the application program. it is the first true end to end layer, implemented in all end systems (es). Each transport and network layer protocol performs essentially the same functions, but each is incompatible with the others unless there is a special device to translate between them. Ict security requirements on http later on. its secure counterpart https wraps http using a security protocol at the transport layer (tls, see section 3.2.1), which can be used to provide confidentiality and integrity for the entire http communication. Chapter 2 application layer chapter 2: outline 2.1 principles of network applications 2.2 web and http.

Lecture 4 Computer Networks Layer 2 Mac Pdf Channel Access Method Ict security requirements on http later on. its secure counterpart https wraps http using a security protocol at the transport layer (tls, see section 3.2.1), which can be used to provide confidentiality and integrity for the entire http communication. Chapter 2 application layer chapter 2: outline 2.1 principles of network applications 2.2 web and http. At the data link layer, two routers communicate directly via a physical channel, whether wired or wireless, whereas at the transport layer, this physical channel is replaced by the entire network. The transport layer at the receiver end performs demultiplexing to separate the messages for different processes. after checking for errors, the headers of messages are dropped and each message is handed over to the respective processes based on their port numbers. The internet or tcp ip network provides two transport layer protocols that can be used by the application layer, namely transmission control protocol (tcp) and user datagram protocol (udp). Tunnel = a new channel over an existing channel (e.g. smtp over an http channel) tunneling operates at the transport layer. secure communication between client and firewall through tunnel; firewall forwards the communication to the nodes in the local network.
Cyber Security Network Transport Cs Lesson 4 Pdf Connect 4 Techs At the data link layer, two routers communicate directly via a physical channel, whether wired or wireless, whereas at the transport layer, this physical channel is replaced by the entire network. The transport layer at the receiver end performs demultiplexing to separate the messages for different processes. after checking for errors, the headers of messages are dropped and each message is handed over to the respective processes based on their port numbers. The internet or tcp ip network provides two transport layer protocols that can be used by the application layer, namely transmission control protocol (tcp) and user datagram protocol (udp). Tunnel = a new channel over an existing channel (e.g. smtp over an http channel) tunneling operates at the transport layer. secure communication between client and firewall through tunnel; firewall forwards the communication to the nodes in the local network.

A1263556640 23521 29 2019 16 Security At The Transport Layer The internet or tcp ip network provides two transport layer protocols that can be used by the application layer, namely transmission control protocol (tcp) and user datagram protocol (udp). Tunnel = a new channel over an existing channel (e.g. smtp over an http channel) tunneling operates at the transport layer. secure communication between client and firewall through tunnel; firewall forwards the communication to the nodes in the local network.
Comments are closed.