Checklist For Web Application Security Developers Agencies

Checklist Web Application Security Pdf World Wide Web Internet Web This web application security checklist will help you to implement the best security practices & how you can protect your solution from any data leaks. Complete developer security checklist with 50 verification points for web applications. tagged with security, webdev, devops, tutorial.

Security Checklist For Developers Pdf Http Cookie Password It's a first step toward building a base of security knowledge around web application security. use this checklist to identify the minimum standard that is required to neutralize vulnerabilities in your critical applications. This assessment checklist focuses on evaluating and enhancing the application security aspect of your software development lifecycle, ensuring robust security measures, compliance with regulations, proactive threat mitigation, and fostering a culture of security awareness. Securing applications in 2025 is more critical than ever due to the growing sophistication of cyber threats. this checklist provides detailed steps for developers to build robust and secure applications while safeguarding sensitive data. In this list, we will cover a comprehensive (but not exhaustive!) list of practices and activities helping to build more secure web applications. these techniques are mostly independent of programming language because they refer to general mechanics of how web applications work.
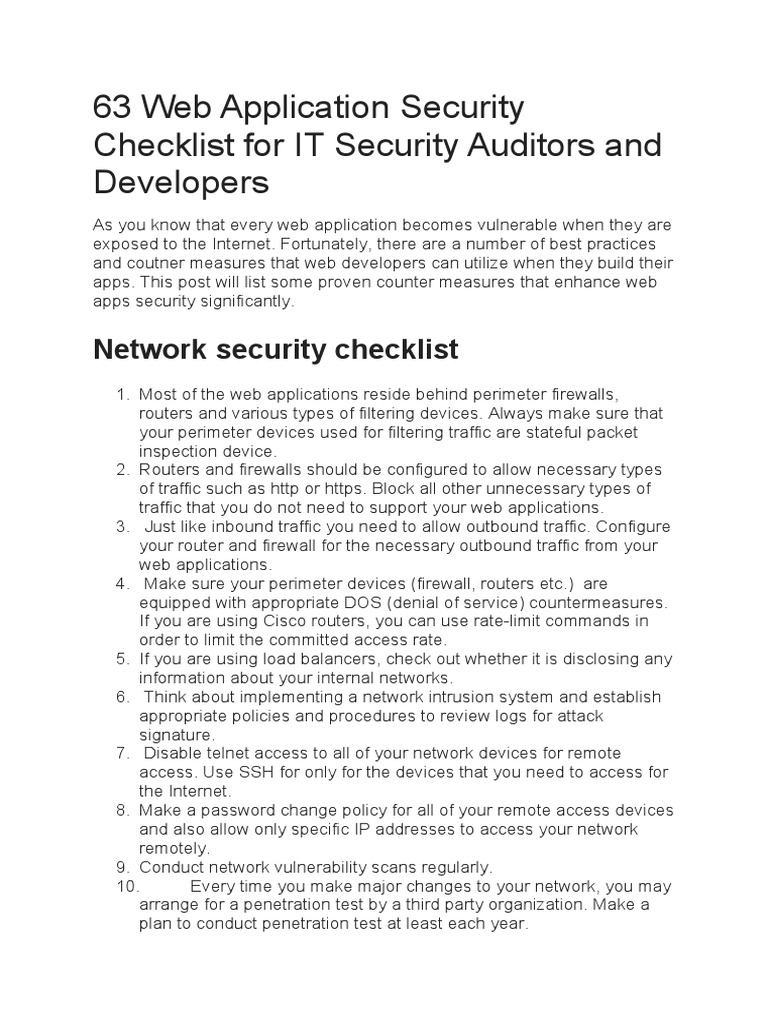
63 Web Application Security Checklist For It Security Auditors And Securing applications in 2025 is more critical than ever due to the growing sophistication of cyber threats. this checklist provides detailed steps for developers to build robust and secure applications while safeguarding sensitive data. In this list, we will cover a comprehensive (but not exhaustive!) list of practices and activities helping to build more secure web applications. these techniques are mostly independent of programming language because they refer to general mechanics of how web applications work. This guide presents a comprehensive application security checklist covering development practices, governance, proactive security measures, organizational readiness, and platform controls. Protect your web apps from cyber threats with this essential security checklist. learn best practices to safeguard data, prevent breaches, and stay secure. This checklist provides essential points for developers, testers, and security professionals to verify the security posture of a web application. use this checklist as a guide during development, testing phases (like qa and uat), and periodic security reviews. In this article, we’ll discuss the key considerations for securing modern web applications and apis. to make it as targeted as possible, we’ve built a checklist of ten improvements that can help improve the security of your applications in an ai accelerated development world.

Web Application Security Policy Pdf This guide presents a comprehensive application security checklist covering development practices, governance, proactive security measures, organizational readiness, and platform controls. Protect your web apps from cyber threats with this essential security checklist. learn best practices to safeguard data, prevent breaches, and stay secure. This checklist provides essential points for developers, testers, and security professionals to verify the security posture of a web application. use this checklist as a guide during development, testing phases (like qa and uat), and periodic security reviews. In this article, we’ll discuss the key considerations for securing modern web applications and apis. to make it as targeted as possible, we’ve built a checklist of ten improvements that can help improve the security of your applications in an ai accelerated development world.
Comments are closed.