Check Out This Graphql Hack For Code Change Impact Visibility
Api Series Hacking Graphql Bramfitt Tech Labs Hi everyone, in this episode, i am gonna show you a little hack to expose the impact your code change has to the public api right in your pull request. Learn how to find vulnerabilities in this popular, versatile query language via practical techniques that include introspection, query, mutation and batching attacks.
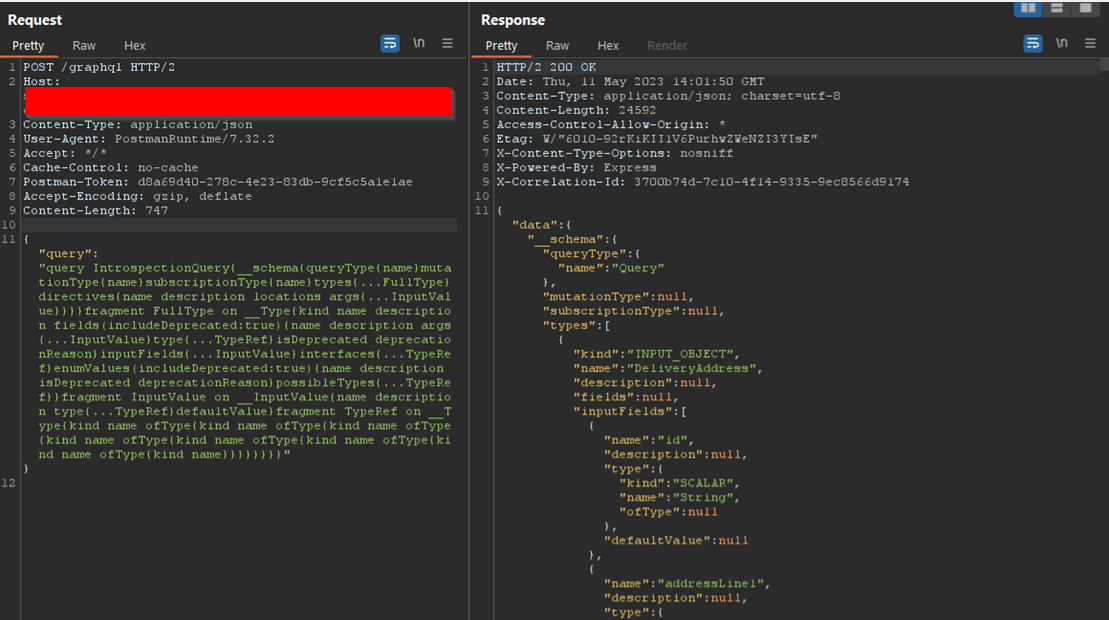
Find Graphql Api Vulnerabilities With Burp Suite Professional Blog Pointfive needed to expose parts of their internal graphql api publicly without compromising security. here is how custom directives and schema filtering solved the problem with minimal code changes. But when left enabled in production, it offers attackers a blueprint of your internal api design — often more revealing than source code. in this post, we’ll walk through how to weaponize graphql introspection for offensive security assessments. Want to inspect a graphql request? here is how! first look at hot chocolate fusion with aspire. check out the new query conventions in hot chocolate 14. simplify your graphql api testing flow. Graphql voyager allows to access a graphql endpoint and visually explore the available types, queries, mutation etc. through an interactive graph by simply pasting the introspection results.

Hacking Graphql Endpoints In Bug Bounty Programs Yeswehack Want to inspect a graphql request? here is how! first look at hot chocolate fusion with aspire. check out the new query conventions in hot chocolate 14. simplify your graphql api testing flow. Graphql voyager allows to access a graphql endpoint and visually explore the available types, queries, mutation etc. through an interactive graph by simply pasting the introspection results. Adhering to the actionable suggestions laid out in the graphql cheat sheet provided by owasp can close the attack vectors that threat actors can exploit. to add additional defensive layers to your graphql api, plugins such as graphql armor can be used. In this post, we’ll go through some of the most common security vulnerabilities found in graphql in detail. this will help you test for these vulnerabilities on your targets or company! what’s graphql? graphql is a strongly typed query language used by developers to easily retrieve data. Graphql is a query language for apis, designed to make data fetching more efficient and flexible compared to traditional rest apis. developed by facebook in 2012 and open sourced in 2015,. Authentication through graphql api with simultaneously sending many queries with different credentials to check it. it’s a classic brute force attack, but now it’s possible to send more than one login password pair per http request because of the graphql batching feature.

How To Discover Graphql Vulnerabilities Cobalt Adhering to the actionable suggestions laid out in the graphql cheat sheet provided by owasp can close the attack vectors that threat actors can exploit. to add additional defensive layers to your graphql api, plugins such as graphql armor can be used. In this post, we’ll go through some of the most common security vulnerabilities found in graphql in detail. this will help you test for these vulnerabilities on your targets or company! what’s graphql? graphql is a strongly typed query language used by developers to easily retrieve data. Graphql is a query language for apis, designed to make data fetching more efficient and flexible compared to traditional rest apis. developed by facebook in 2012 and open sourced in 2015,. Authentication through graphql api with simultaneously sending many queries with different credentials to check it. it’s a classic brute force attack, but now it’s possible to send more than one login password pair per http request because of the graphql batching feature.

Graphql Api Query Introspection Graphql is a query language for apis, designed to make data fetching more efficient and flexible compared to traditional rest apis. developed by facebook in 2012 and open sourced in 2015,. Authentication through graphql api with simultaneously sending many queries with different credentials to check it. it’s a classic brute force attack, but now it’s possible to send more than one login password pair per http request because of the graphql batching feature.
Comments are closed.