Chapter 5 Scanning Basics

Module 2 Chapter 5 Internal Scanning Organizational Analysis Download Learn plc programming fundamentals: memory maps, i o addressing, ladder logic, and program scan cycles. focus on allen bradley plc 5 and slc 500. There are typical steps involved when wanting to know how to outline the sequence of events involved in a plc scan cycle. summary of the steps: closed input makes input bit 1, which triggers the processor to set the output bit, energizing the output (light) on the next scan, repeating in run mode.

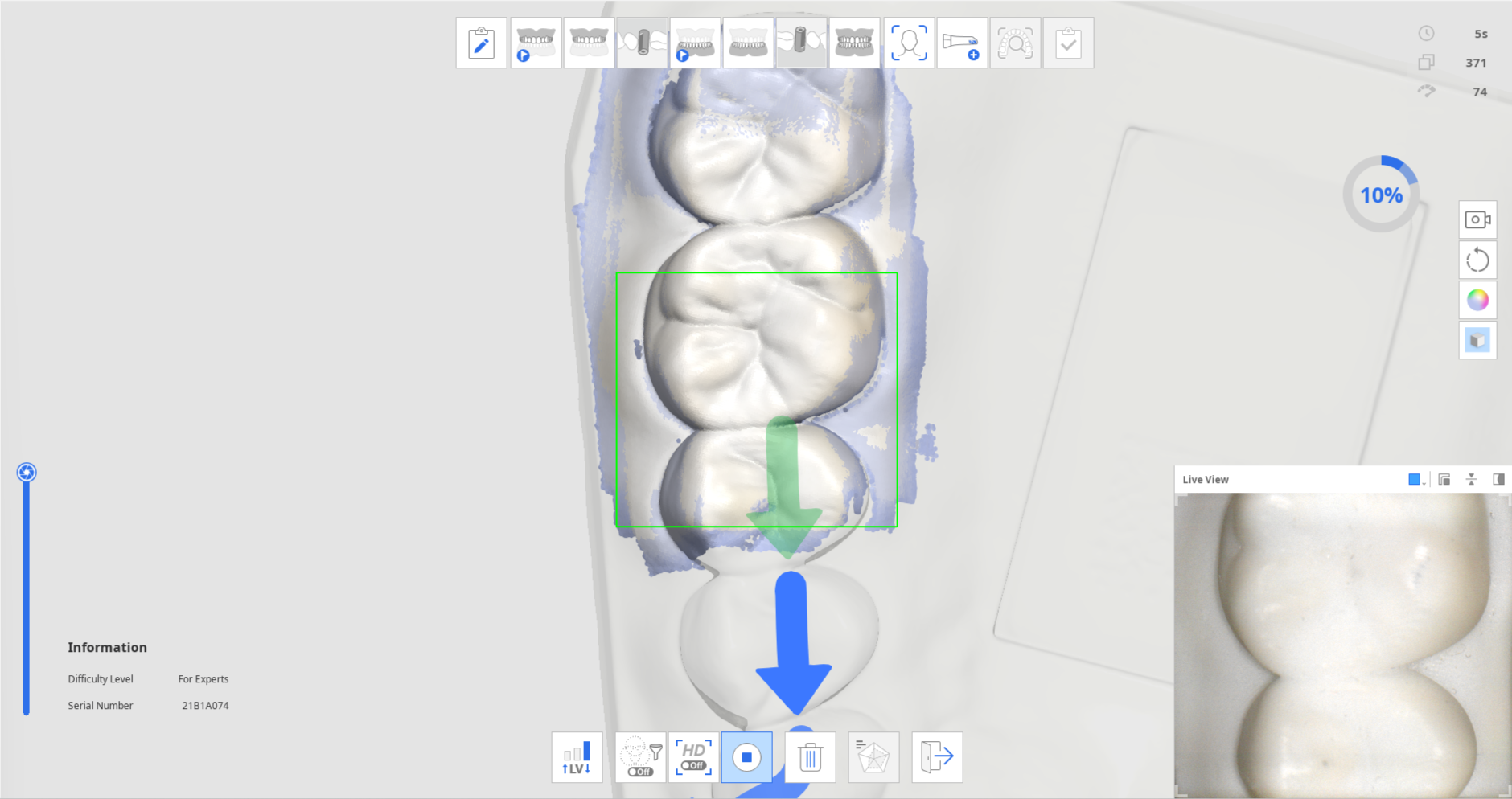
Chapter 5 Phy380 Pdf Scanning Electron Microscope X Ray Follow the instructions and directions of the arrows to scan the practice model. check the scan information and progress while acquiring data for your effective scanning practice. A (n) scan pattern examines instructions rung by rung. a) calculated and stored in the plc's memory. b) computed each time the end instruction is executed. c) the time taken to scan inputs and outputs and execute the user program. d) all of these. which of the following standard plc programming languages is a graphical language?. The task of scanning the source statement, recognizing and classifying the various tokens, is known as lexical analysis. the part of the compiler that performs this analytic function is commonly called the scanner. after the token scan, each statement in the program must be recognized as some language construct, such as a. Study with quizlet and memorize flashcards containing terms like what is scanning?, types of scans, checking for live systems and more.

Westbrook Chapter 1 Basics Of Scanning Procedures Flashcards Quizlet The task of scanning the source statement, recognizing and classifying the various tokens, is known as lexical analysis. the part of the compiler that performs this analytic function is commonly called the scanner. after the token scan, each statement in the program must be recognized as some language construct, such as a. Study with quizlet and memorize flashcards containing terms like what is scanning?, types of scans, checking for live systems and more. This document discusses port scanning and various port scanning tools. it describes different types of port scans like syn scans, connect scans, null scans and xmas scans. it also covers popular port scanning tools like nmap, nessus, openvas and how to use them. Network scanning discovering systems on the network (can be hosts, switches, servers, routers, firewalls and so on) and looking at what ports are open as well as applications services and their respective versions that may be running. This chapter identifies the scanner parts and gives you the basics for diagnosing and solving scanner problems. for solutions to common setup and software problems, see “problem solving” on page 54. This chapter introduces you to the two of the most important pre attack phases: footprinting and scanning. although these steps don’t constitute breaking in, they occur at the point which a hacker will start to get interactive.
Chapter 5 Scanning Basics This document discusses port scanning and various port scanning tools. it describes different types of port scans like syn scans, connect scans, null scans and xmas scans. it also covers popular port scanning tools like nmap, nessus, openvas and how to use them. Network scanning discovering systems on the network (can be hosts, switches, servers, routers, firewalls and so on) and looking at what ports are open as well as applications services and their respective versions that may be running. This chapter identifies the scanner parts and gives you the basics for diagnosing and solving scanner problems. for solutions to common setup and software problems, see “problem solving” on page 54. This chapter introduces you to the two of the most important pre attack phases: footprinting and scanning. although these steps don’t constitute breaking in, they occur at the point which a hacker will start to get interactive.
Comments are closed.