Chapter 3 Cyber Strategy Lfhspbc

Chapter 3 Cyberattacks And Cybersecurity Pdf Security Computer Chapter three: enduring challenges for cyber strategyone cyberspace norm that has emerged is that cyber operations do not lead to violent retaliation. anothe. Chapter three: the pandemic, the media, and restoring trust in science the american media is biased toward negative news reporting, which resulted in a distorted view of the actual risk of covid 19.

205b Cyber Security Unit 3 Pdf Chapter 3: cybersecurity from nation states to private partnerships jacquelyn schneider answers questions from students about us cybersecurity. This was followed by the sobering phase of cyber reality, where digital tools began to be used maliciously, causing disenfranchisement and concern for security. Chapter one: why do we need a cyber strategy?cybersecurity is important because it is involved in everything from infrastructure to nuclear weapons. implemen. Hoover fellow jacquelyn schneider describes a war game she has conducted that demonstrates the effectiveness of cyberattacks. the early findings of these war games show that the most devastating.
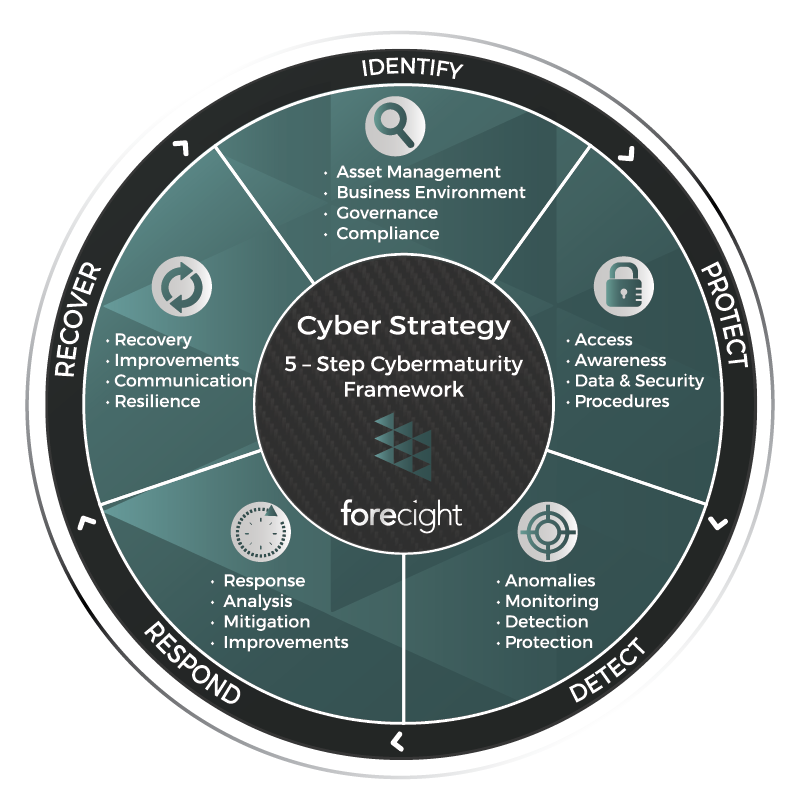
Cyber Strategy Forecight Chapter one: why do we need a cyber strategy?cybersecurity is important because it is involved in everything from infrastructure to nuclear weapons. implemen. Hoover fellow jacquelyn schneider describes a war game she has conducted that demonstrates the effectiveness of cyberattacks. the early findings of these war games show that the most devastating. Cyberattacks from china, russia, iran, north korea, and nonstate actors eat away at the infrastructure of our digitally enabled society. the us needs a cybersecurity policy to articulate its. Chapter 4: international cybersecurity and civilian cyber usejacquelyn schneider answers questions from students about us cybersecurity. will international c. Urgent questions remain concerning the united states’ readiness for the china cyber challenge, including the adequacy of resourcing for u.s. military cyber forces, the suficiency of existing protections for u.s. critical infrastructure, and the scope of public private cybersecurity cooperation. According to world health organization statistics, up to 3 million ukrainians are expected to leave their homes this winter. according to the new york times on november 22, due to russia's attack on infrastructure in various parts of ukraine, many ukrainian cities including khlso.

Module 3 Cyber Security Pdf Denial Of Service Attack Malware Cyberattacks from china, russia, iran, north korea, and nonstate actors eat away at the infrastructure of our digitally enabled society. the us needs a cybersecurity policy to articulate its. Chapter 4: international cybersecurity and civilian cyber usejacquelyn schneider answers questions from students about us cybersecurity. will international c. Urgent questions remain concerning the united states’ readiness for the china cyber challenge, including the adequacy of resourcing for u.s. military cyber forces, the suficiency of existing protections for u.s. critical infrastructure, and the scope of public private cybersecurity cooperation. According to world health organization statistics, up to 3 million ukrainians are expected to leave their homes this winter. according to the new york times on november 22, due to russia's attack on infrastructure in various parts of ukraine, many ukrainian cities including khlso.

Chapter 3 Lesson 6 Cybersecurity Pdf Security Computer Security Urgent questions remain concerning the united states’ readiness for the china cyber challenge, including the adequacy of resourcing for u.s. military cyber forces, the suficiency of existing protections for u.s. critical infrastructure, and the scope of public private cybersecurity cooperation. According to world health organization statistics, up to 3 million ukrainians are expected to leave their homes this winter. according to the new york times on november 22, due to russia's attack on infrastructure in various parts of ukraine, many ukrainian cities including khlso.

Cyber Strategy Roadmap 3cs Aquarah
Comments are closed.