Chapter 2 Web Security Pdf Transport Layer Security Public Key

Transport Layer Security Pdf Transport Layer Security Computer Https provides more secure communication than http by using ssl tls encryption. common web security threats can be mitigated using techniques like firewalls, encryption, and authentication. Chapter 1 introduces web security, the history of ssl and tls, and limitations of security protocols. chapter 2 discusses cryptography techniques like secret key cryptography, public key cryptography, and certificates.

Chapt2 Transport Level Security Ssl Tls Pdf Transport Layer This document discusses transport layer security protocols like ssl and tls. it begins by outlining the learning objectives which are to present techniques and protocols for transport level security, including ssl tls and https. The document discusses transport level security, focusing on protocols like tls and ssl, outlining their purpose in ensuring privacy and data integrity during internet communication. This abstract examines various security challenges in cloud environments and explores how distributed systems can provide solutions to enhance security posture. Key generation and exchange pre master secret after server’s certificate is verified, client generates random number, called pre master secret. client encrypts pre master secret using server’s public key and sends to the server. length of the key depends on the public key algorithm used.
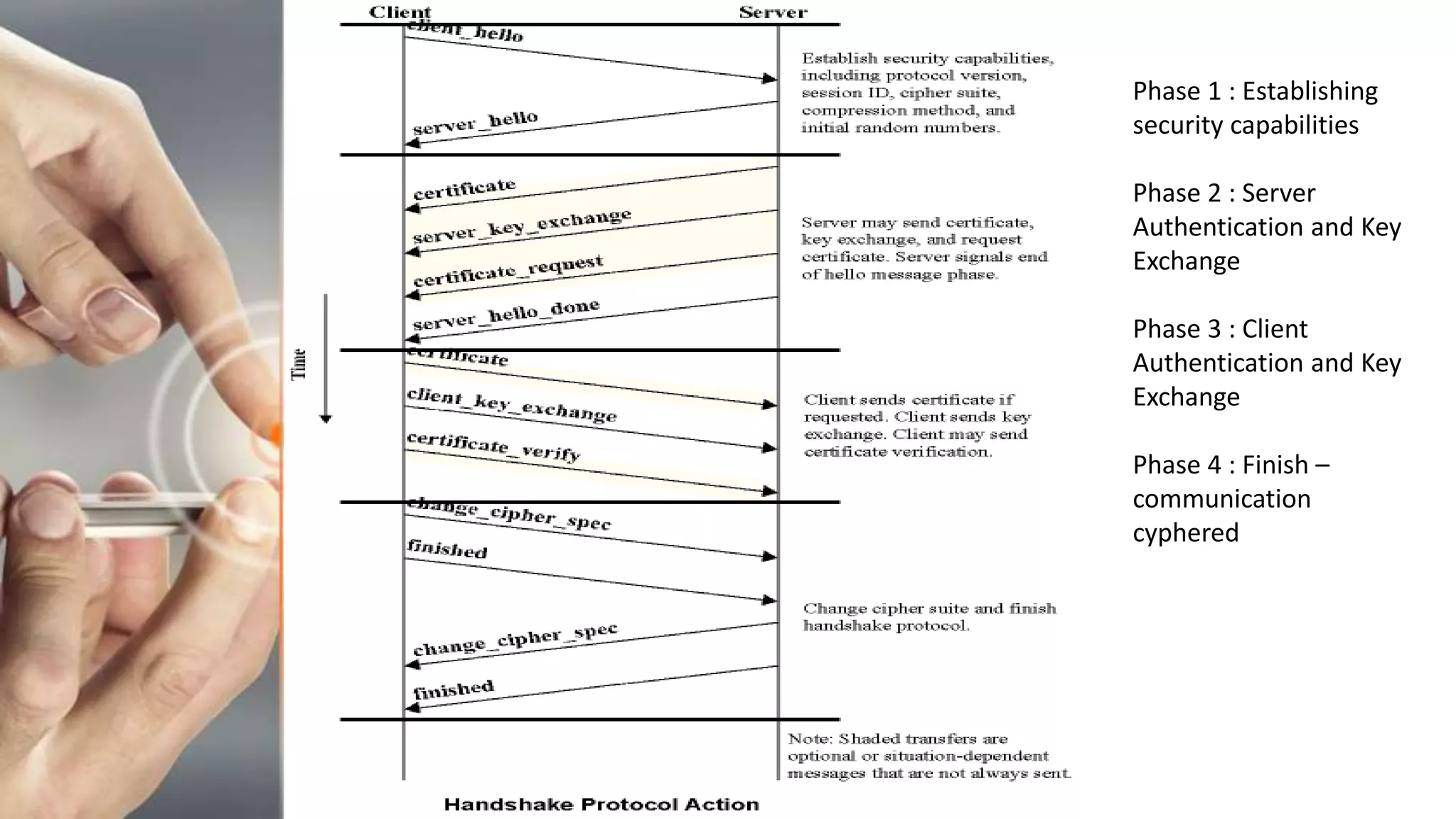
Transport Layer Security Pptx This abstract examines various security challenges in cloud environments and explores how distributed systems can provide solutions to enhance security posture. Key generation and exchange pre master secret after server’s certificate is verified, client generates random number, called pre master secret. client encrypts pre master secret using server’s public key and sends to the server. length of the key depends on the public key algorithm used. Transport layer security (tls) provides mechanisms to protect data during electronic dissemination across the internet. Transport layer security (tls) transport layer security (tls) provides a secure channel between two communicating peers. the connection is private, as data is encrypted with symmetric cryptography. the identity of the server can be verified using the public key infrastructure. Solution: bob sends different random nonce for each connection. this causes encryption keys to be different for each connection. In this chapter, we first discuss how transport layer security works. we specifically focus on the two most important aspects of tls: handshake and data transmission.

5 Network Security2 Rtd Pdf Transport Layer Security Firewall Transport layer security (tls) provides mechanisms to protect data during electronic dissemination across the internet. Transport layer security (tls) transport layer security (tls) provides a secure channel between two communicating peers. the connection is private, as data is encrypted with symmetric cryptography. the identity of the server can be verified using the public key infrastructure. Solution: bob sends different random nonce for each connection. this causes encryption keys to be different for each connection. In this chapter, we first discuss how transport layer security works. we specifically focus on the two most important aspects of tls: handshake and data transmission.

Transport Layer Security Pdf Transport Layer Security Public Key Solution: bob sends different random nonce for each connection. this causes encryption keys to be different for each connection. In this chapter, we first discuss how transport layer security works. we specifically focus on the two most important aspects of tls: handshake and data transmission.
Transport Layer Security Chapter 7 1 Socket Layer
Comments are closed.