Chapter 15 Case Study 11 Data System Risk

Case Study Risk Analysis Pdf Crime Prevention Computer Security Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Caf 3 st (data systems & risk) free download as pdf file (.pdf), text file (.txt) or read online for free.
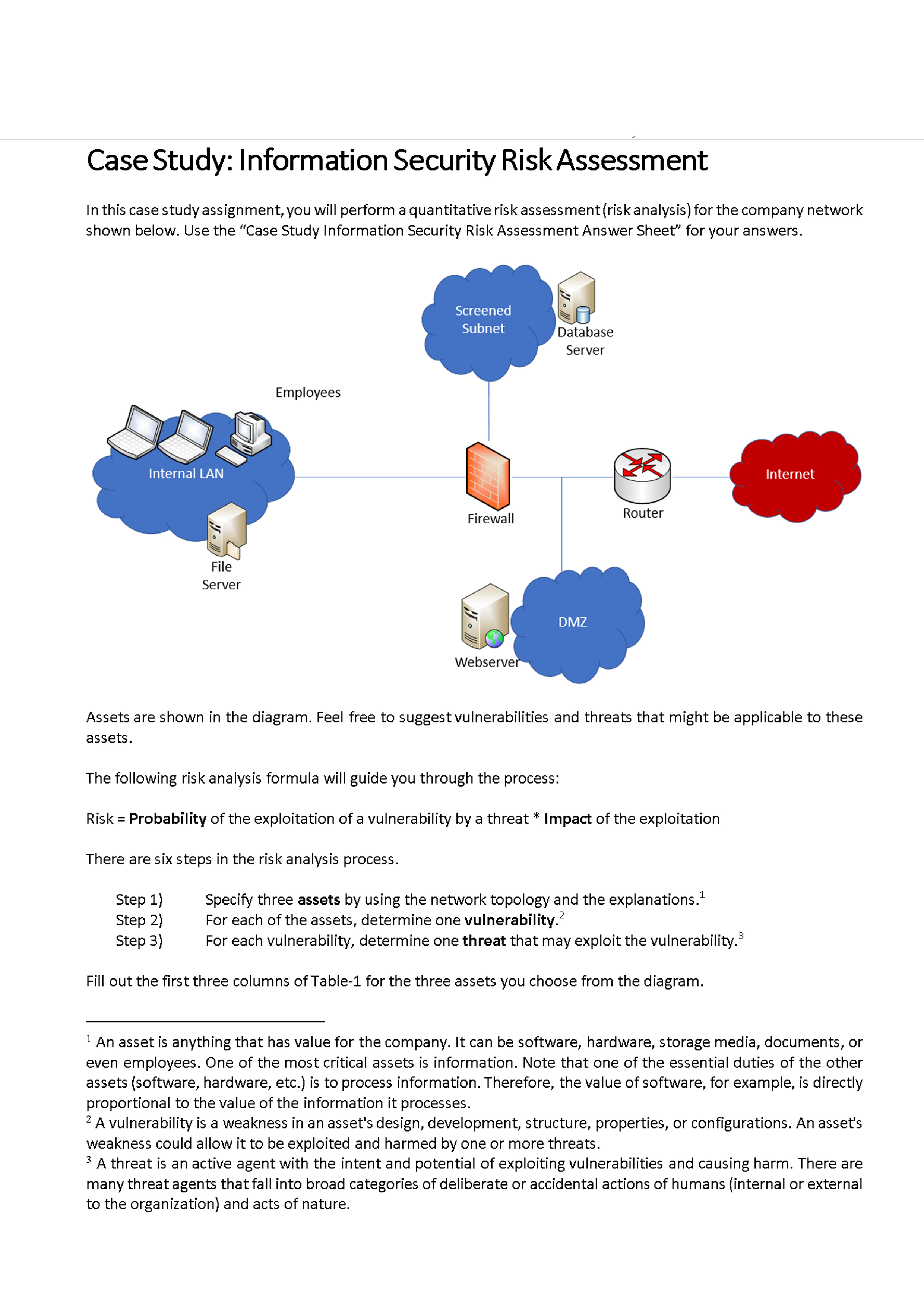
Solved Case Study Information Security Risk Assessment In Chegg The most cost effective control in this case would be risk assessment. using risk assessment, the organization would be able to identify, assess, and implements critical security controls in the systems where the customer and financial files are stored (wangen, 2017). This case study analysis will explore the facts and circumstances surrounding this damaging cyberattack, and critically analyze the factors concerning the case to draw conclusions about ways to. In this case study, we examine the 2013 breach of american retailer target, which led to the theft of personally identifiable information (pii) and credit card information belonging to over 70 million customers from target’s databases. This summary of findings and recommendations summarizes the case studies in cyber supply chain risk management series’ major findings and recommendations based on expert interviews.

Pdf An Information System Risk Assessment Model A Case Study In In this case study, we examine the 2013 breach of american retailer target, which led to the theft of personally identifiable information (pii) and credit card information belonging to over 70 million customers from target’s databases. This summary of findings and recommendations summarizes the case studies in cyber supply chain risk management series’ major findings and recommendations based on expert interviews. Urrounds cyber security investments. chief information officers (cios) operate with limited resources and typically do not know the relative risk of different cyber attack vectors, such as malicious ema. This incident was selected as a case study to understand the technical modus operandi of the attack, map out exploited vulnerabilities, and identify the related compliance requirements, that existed. Companies today specifically information technology based companies are increasingly concerned about almost their it uncertainties. the purpose of the present paper is to discuss the major critical challenges affecting an it project organization. This chapter is intended to assist in this process by providing information and case studies on the range of consequences of a breach and show that the business impact is so much more than just a fine.

Chapter 15mitigating Risk With A Computer Incident Response Te Pdf Urrounds cyber security investments. chief information officers (cios) operate with limited resources and typically do not know the relative risk of different cyber attack vectors, such as malicious ema. This incident was selected as a case study to understand the technical modus operandi of the attack, map out exploited vulnerabilities, and identify the related compliance requirements, that existed. Companies today specifically information technology based companies are increasingly concerned about almost their it uncertainties. the purpose of the present paper is to discuss the major critical challenges affecting an it project organization. This chapter is intended to assist in this process by providing information and case studies on the range of consequences of a breach and show that the business impact is so much more than just a fine.
Comments are closed.