Certmike Explains Role Based Access Control Rbac

Role Based Access Control Rbac Role Based Access Control Rbac By In this video, certification and cybersecurity expert mike chapple breaks down the basics of role based access control to help you prepare for your exam. Grants access based on a user’s responsibilities according to their position. defines roles and associated privileges, and assigns permissions to control access accordingly.
Role Based Access Control Rbac This complete guide explains what role based access control is, why it matters, how it works, its benefits, challenges, real examples, and how businesses across industries use it. Role based access control (rbac) is the access control model that assigns permissions based on job roles and responsibilities. it provides a straightforward, manageable method of managing access that is less susceptible to error than assigning separate privileges to users. Role based access control (rbac) is a method of restricting network access based on the roles of individual users within an enterprise. organizations use rbac also called role based security to parse levels of access based on an employee's roles and responsibilities. Find out what role based access control (rbac) is and how it increases security while saving time and resources. discover the best practices and advantages of rbac.
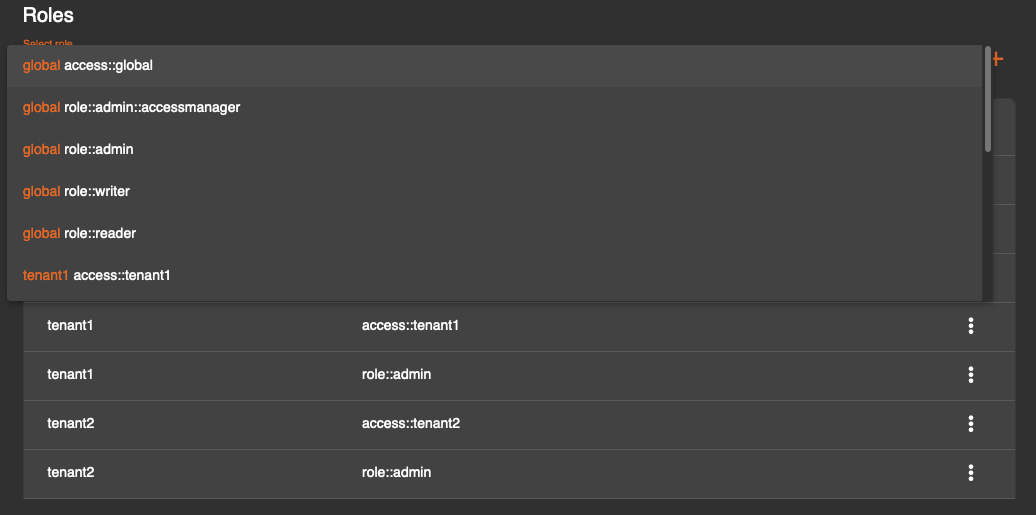
Role Based Access Control Simplifying Access Security Management Role based access control (rbac) is a method of restricting network access based on the roles of individual users within an enterprise. organizations use rbac also called role based security to parse levels of access based on an employee's roles and responsibilities. Find out what role based access control (rbac) is and how it increases security while saving time and resources. discover the best practices and advantages of rbac. What is role based access control (rbac)? role based access control (rbac) is a model for authorizing end user access to systems, applications and data based on a user’s predefined role. Role based access control (rbac) is a method for managing user permissions based on roles within an organization. this guide explores the principles of rbac, its benefits, and how it enhances security and efficiency. What is role based access control (rbac)? role based access control (rbac) is a method of regulating access to computer or network resources based on the roles of individual users within an organization. This article explains how microsoft sentinel assigns permissions to user roles for both microsoft sentinel siem and microsoft sentinel data lake, identifying the allowed actions for each role. microsoft sentinel uses azure role based access control (azure rbac) to provide built in and custom roles for microsoft sentinel siem, and microsoft entra id role based access control (microsoft entra id.

Role Based Access Control Rbac Avahi What is role based access control (rbac)? role based access control (rbac) is a model for authorizing end user access to systems, applications and data based on a user’s predefined role. Role based access control (rbac) is a method for managing user permissions based on roles within an organization. this guide explores the principles of rbac, its benefits, and how it enhances security and efficiency. What is role based access control (rbac)? role based access control (rbac) is a method of regulating access to computer or network resources based on the roles of individual users within an organization. This article explains how microsoft sentinel assigns permissions to user roles for both microsoft sentinel siem and microsoft sentinel data lake, identifying the allowed actions for each role. microsoft sentinel uses azure role based access control (azure rbac) to provide built in and custom roles for microsoft sentinel siem, and microsoft entra id role based access control (microsoft entra id.

Role Based Access Control Rbac What is role based access control (rbac)? role based access control (rbac) is a method of regulating access to computer or network resources based on the roles of individual users within an organization. This article explains how microsoft sentinel assigns permissions to user roles for both microsoft sentinel siem and microsoft sentinel data lake, identifying the allowed actions for each role. microsoft sentinel uses azure role based access control (azure rbac) to provide built in and custom roles for microsoft sentinel siem, and microsoft entra id role based access control (microsoft entra id.
What Is Role Based Access Control Rbac
Comments are closed.