Catphish Cryeye Project
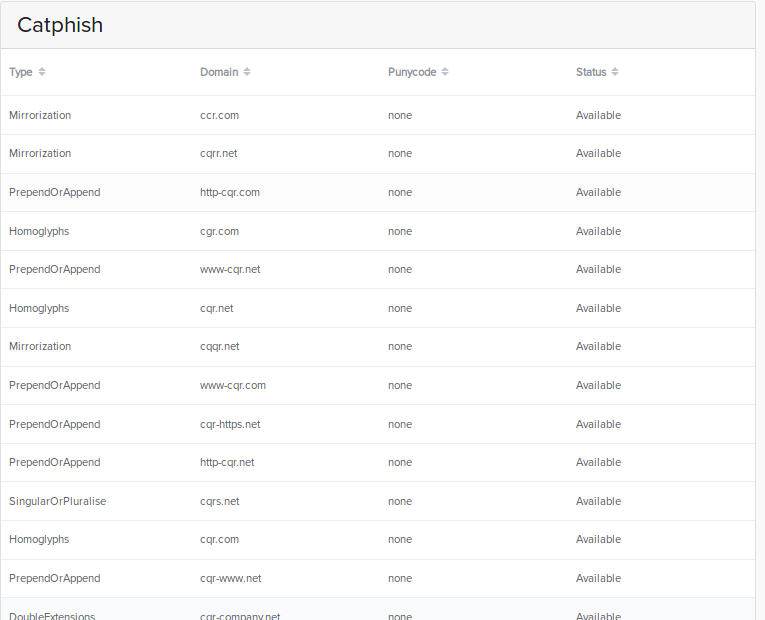
Catphish Cryeye Project ¶ flag: entrypoint ["sh","entrypoint.sh"] cmd="$@" ruby catphish.rb no logo d $ {cmd} generate a # ruby catphish.rb no logo d $ {cmd} expired. Catphish generate similar looking domains for phishing attacks. check expired domains and their categorized domain status to evade proxy categorization. whitelisted domains are perfect for your c2 servers. perfect for red team engagements.
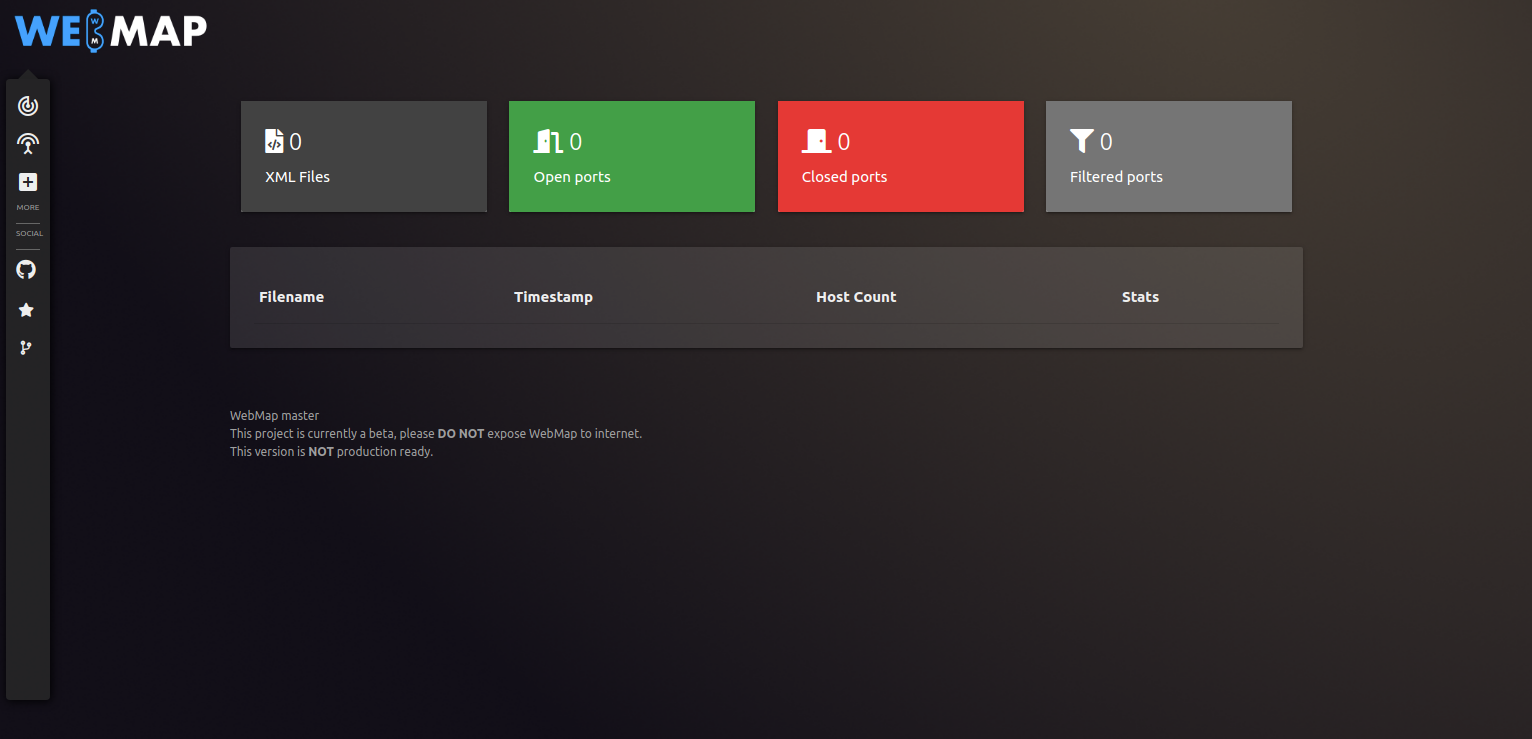
Manual Pentesting Tool Cryeye Project With this tool, you can see the domain name and exactly what changes have been made to make it look similar to yours, check for any dns records, obtain evidence that the domain is malicious or impersonating you, receive guidance on next steps, and even generate correspondence if required. Catphish about tool: generate similar looking domains for phishing attacks. check expired domains and their categorized domain status to evade proxy categorization. whitelisted domains are perfect for your c2 servers. perfect for red team engagements. website: github ring0lab catphish. Encounters are the distillation of the core format of 🐱phish. they are kind of like the "roguelike mode" while the regular missions represent the "campaign mode", with more elaborate set ups and multi step arcs. there are three encounters so far: luka, 24. Experience cryeye in action. pinpoint and mitigate critical vulnerabilities with cryeye’s precise and automated security validation. leverage cryeye’s all in one platform for continuous security assessments, eliminating the need for costly manual audits or external consultants.
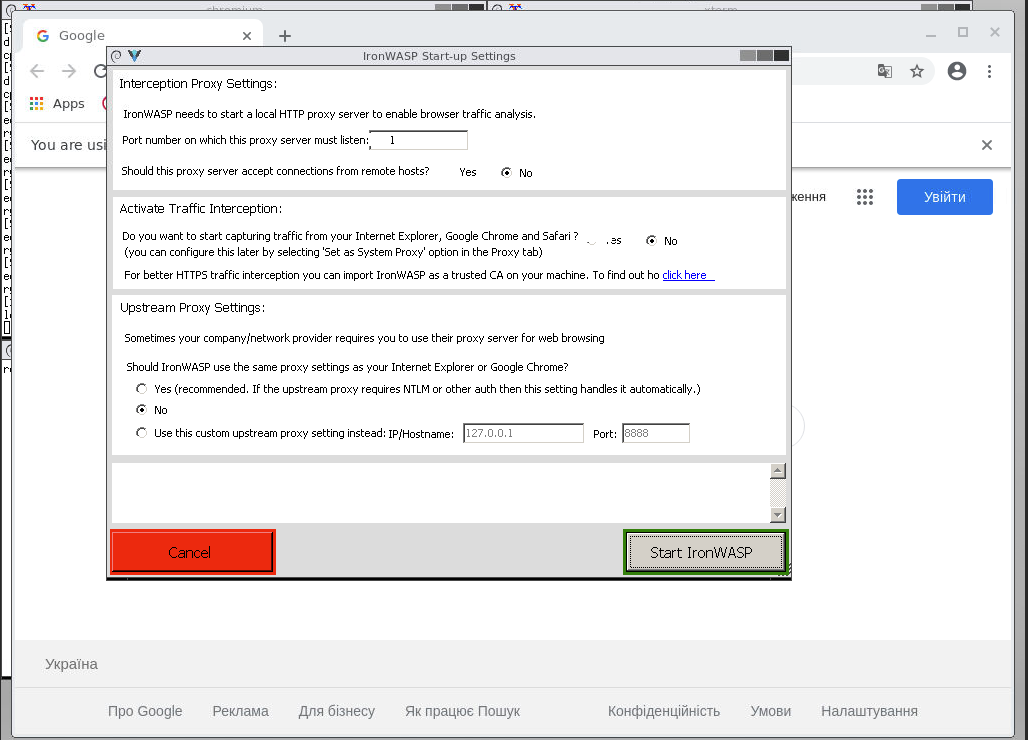
Manual Pentesting Tool Cryeye Project Encounters are the distillation of the core format of 🐱phish. they are kind of like the "roguelike mode" while the regular missions represent the "campaign mode", with more elaborate set ups and multi step arcs. there are three encounters so far: luka, 24. Experience cryeye in action. pinpoint and mitigate critical vulnerabilities with cryeye’s precise and automated security validation. leverage cryeye’s all in one platform for continuous security assessments, eliminating the need for costly manual audits or external consultants. That's why we're introducing #catphish – a tool that checks the status of all tlds and makes it easy to generate similar looking domains for phishing attacks. it also allows you to generate whitelisted domains that can be used as c&c servers or even as decoy websites. Catphish is an application that swiftly verifies whether a message is safe or if it is an attempt at data phishing (scam). paste the content or link, and our algorithms will assess the sender's credibility within seconds, protecting you from losing money and identity. When a suspicious domain is registered, catphish automatically collects whois data, dns records, and website screenshots. it generates a risk score and provides ai driven guidance on filing an abuse complaint with the domain registrar. We will be participating for online event at 17th of april with our cybersecurity project called cryeye which stands for deep and customisable cybersecurity controls integration and was.
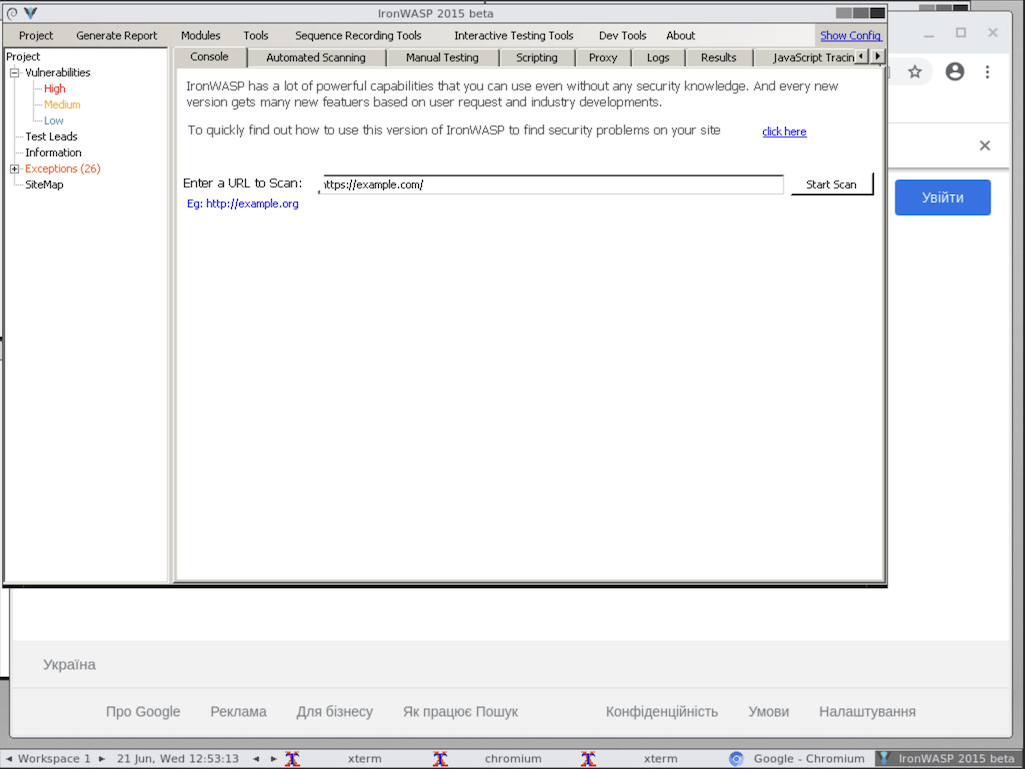
Manual Pentesting Tool Cryeye Project That's why we're introducing #catphish – a tool that checks the status of all tlds and makes it easy to generate similar looking domains for phishing attacks. it also allows you to generate whitelisted domains that can be used as c&c servers or even as decoy websites. Catphish is an application that swiftly verifies whether a message is safe or if it is an attempt at data phishing (scam). paste the content or link, and our algorithms will assess the sender's credibility within seconds, protecting you from losing money and identity. When a suspicious domain is registered, catphish automatically collects whois data, dns records, and website screenshots. it generates a risk score and provides ai driven guidance on filing an abuse complaint with the domain registrar. We will be participating for online event at 17th of april with our cybersecurity project called cryeye which stands for deep and customisable cybersecurity controls integration and was.
Comments are closed.