Caching Strategy Read Through Pattern
Caching Strategy Read Through Pattern Unlike cache aside pattern, which requires application logic to fetch and populate the cache, read through cache manages data retrieval from database on behalf of the application. The read through caching pattern allows your application to retrieve data directly from the cache. if the data isn't available in the cache, it fetches it from the database and stores it in the cache for future access.

Caching Strategies Overview Cats In Code In this strategy, the application is responsible for managing the cache. when data is requested, the application checks the cache first. if the data is not in the cache, it is retrieved from. In a read through pattern, applications request data directly from the caching system, and if the data exists in the cache, that data is returned to the application. if the data does not exist (a “cache miss”), then the system retrieves the data from the backend store. Effective caches must support both intensive read only and read write operations, and in the case of read write operations, the cache and database must be kept fully synchronized. to accomplish this, coherence supports read through, write through, refresh ahead and write behind caching. In the read through strategy, the cache acts as an intermediary between the application and the database. when the application requests data, it first looks in the cache. if data is available (cache hit), it’s returned to the application.
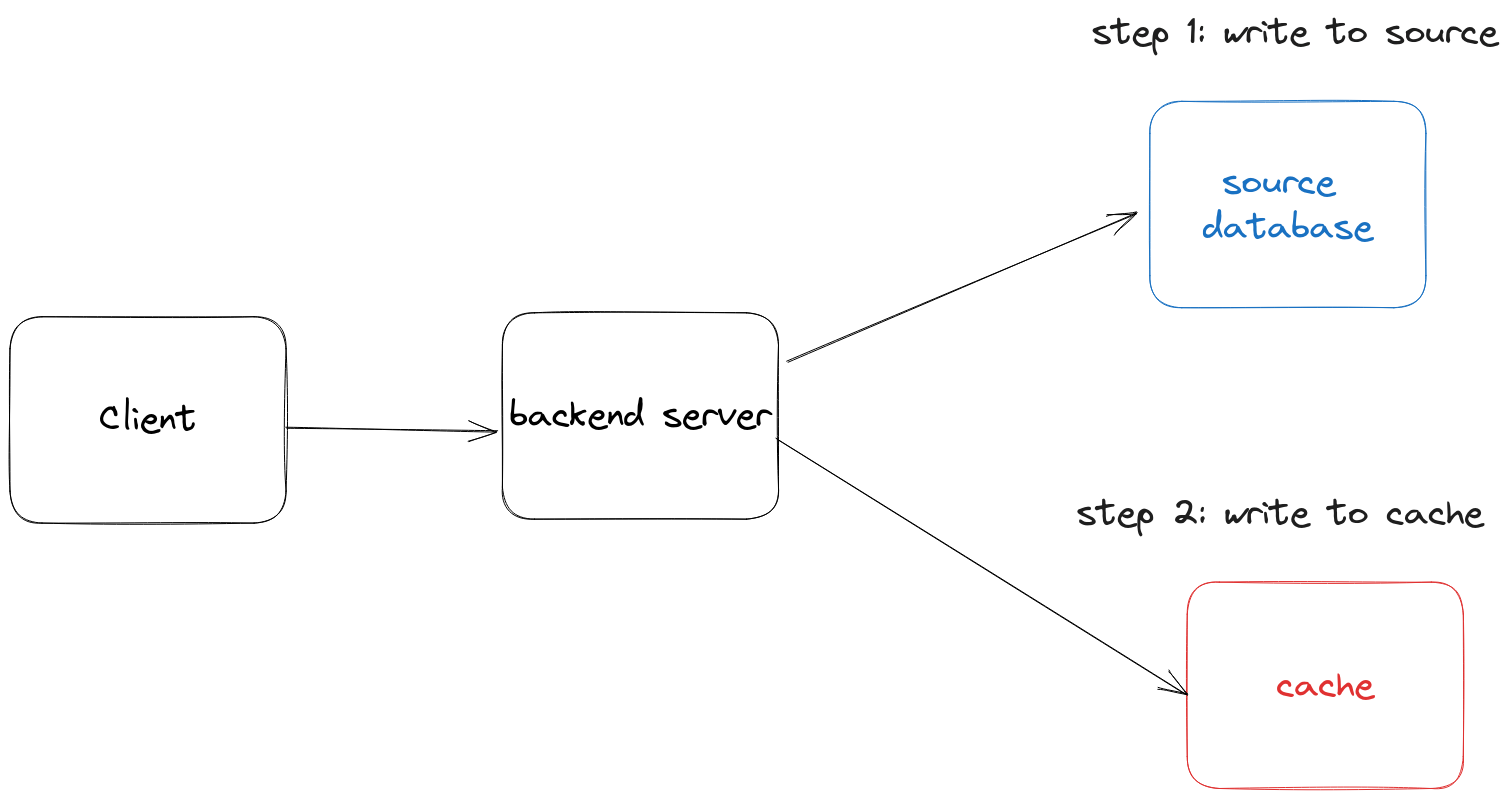
Distributed Caching Pattern Write Through Linisnil Effective caches must support both intensive read only and read write operations, and in the case of read write operations, the cache and database must be kept fully synchronized. to accomplish this, coherence supports read through, write through, refresh ahead and write behind caching. In the read through strategy, the cache acts as an intermediary between the application and the database. when the application requests data, it first looks in the cache. if data is available (cache hit), it’s returned to the application. Complete guide to caching strategies and patterns. learn cache aside, read through, write through, write behind patterns, redis caching techniques, database caching strategies, and cache invalidation strategies with real world examples. Read through: cache intercepts all reads and automatically fetches from database on miss, transparently loading and returning values. enables request coalescing where thousands of concurrent requests for the same missing key collapse into one backend query, preventing load spikes. When you are caching data from your database, there are caching patterns for redis and memcached that you can implement, including proactive and reactive approaches. In the read through caching approach, the cache is positioned between the application and the database. whenever the data requests come, the application goes to the cache first.
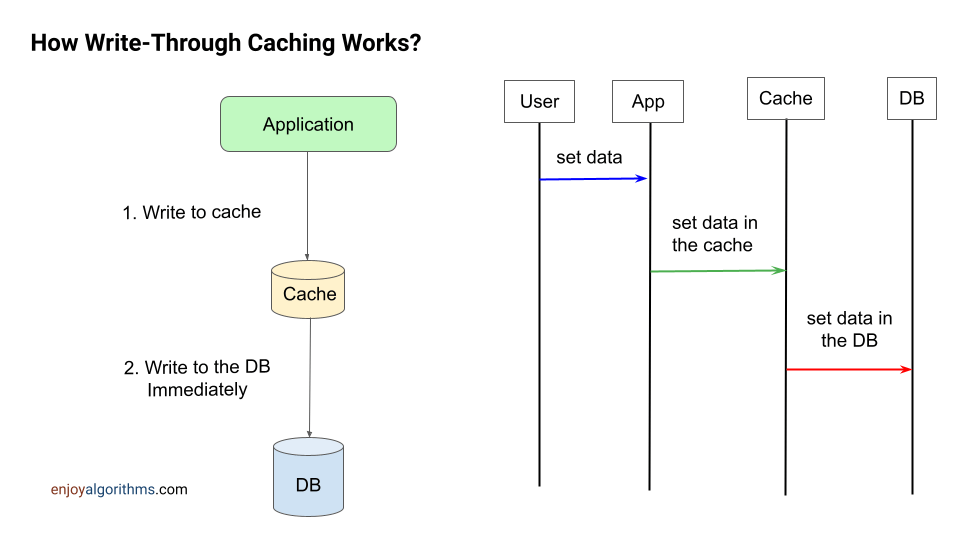
Write Through Caching Strategy Complete guide to caching strategies and patterns. learn cache aside, read through, write through, write behind patterns, redis caching techniques, database caching strategies, and cache invalidation strategies with real world examples. Read through: cache intercepts all reads and automatically fetches from database on miss, transparently loading and returning values. enables request coalescing where thousands of concurrent requests for the same missing key collapse into one backend query, preventing load spikes. When you are caching data from your database, there are caching patterns for redis and memcached that you can implement, including proactive and reactive approaches. In the read through caching approach, the cache is positioned between the application and the database. whenever the data requests come, the application goes to the cache first.

Caching Strategy Distribution Download Scientific Diagram When you are caching data from your database, there are caching patterns for redis and memcached that you can implement, including proactive and reactive approaches. In the read through caching approach, the cache is positioned between the application and the database. whenever the data requests come, the application goes to the cache first.
Comments are closed.