Business Email Compromise

Business Email Compromise Rablowoods Learn about business email compromise (bec), what happens during a bec scam, and how to protect your organization from this email based fraud. Business email compromise (bec) or email account compromise (eac) is a common type of sophisticated fraud scheme that results in over $2 billion in loss every year. the bad actors gain unauthorized access to email accounts and use that access to coordinate payments or transfers of funds.
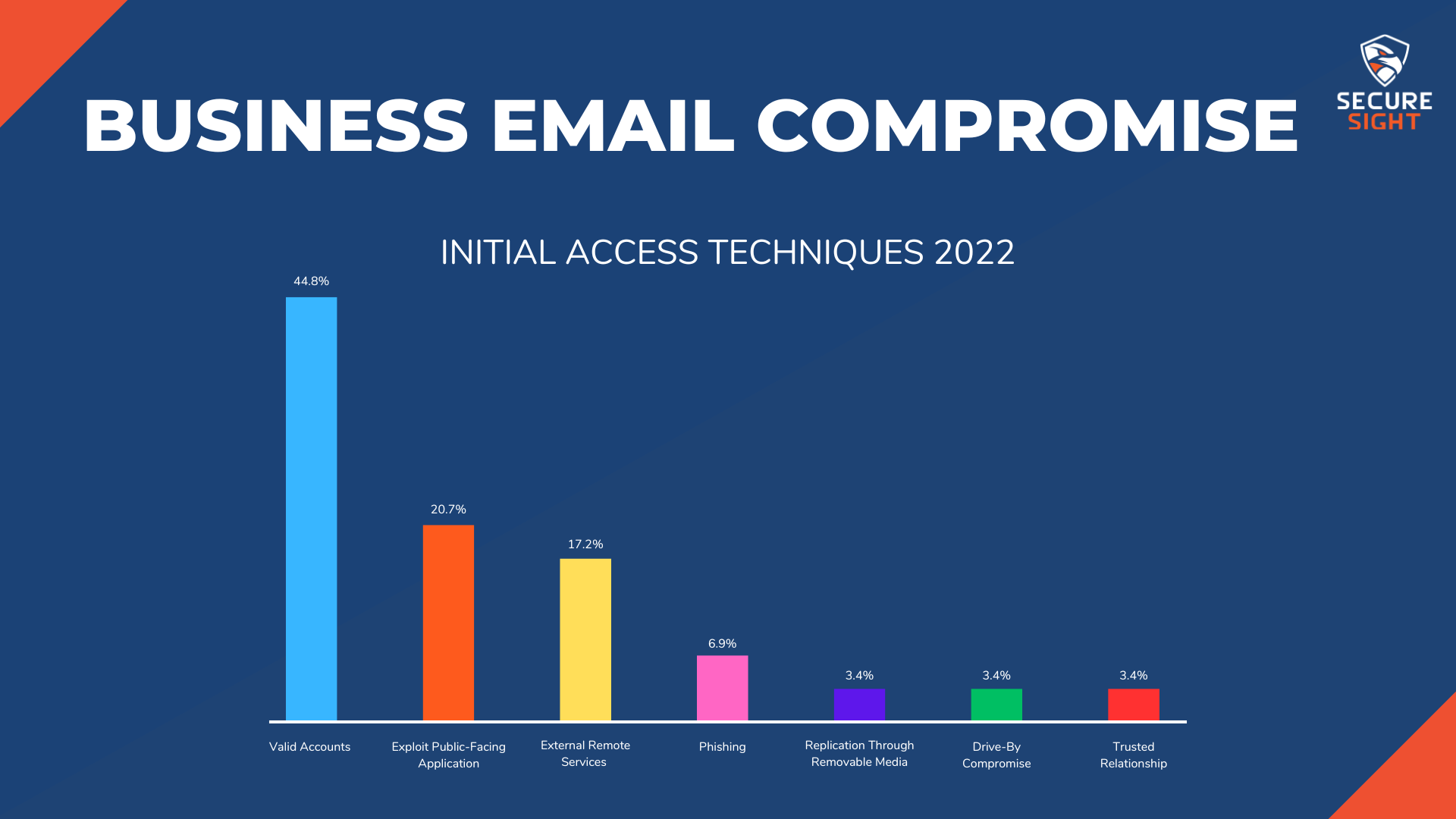
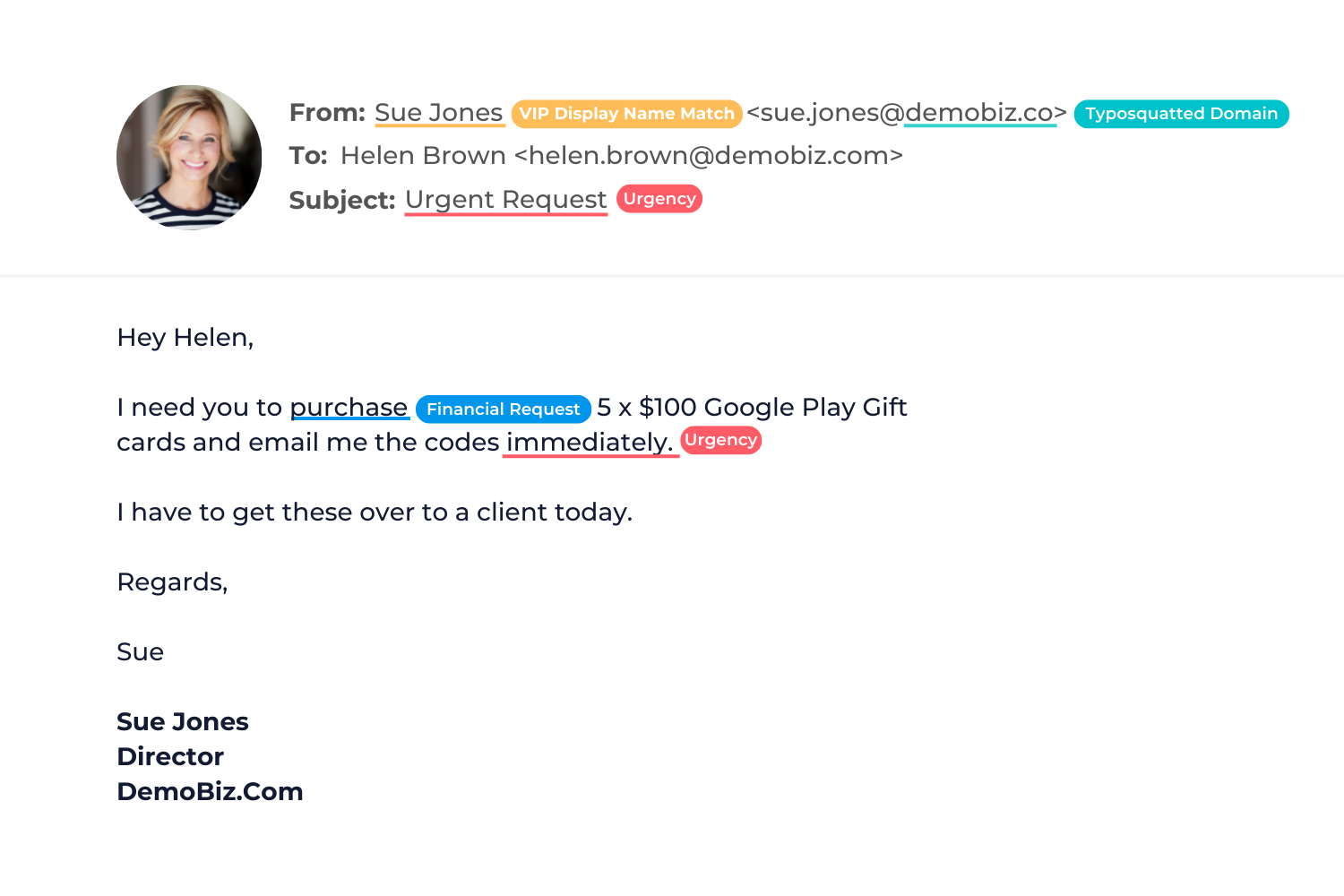
Business Risk Series Business Email Compromise Business email compromise (bec) scams rank among the most financially devastating cybercrimes facing organizations today. as digital communication becomes increasingly central to business operations, cybercriminals have honed their tactics to exploit vulnerabilities in email systems, targeting companies of all sizes. the sophisticated nature of bec attacks, which often involve impersonation. Learn how bec scams work and how to protect yourself from them. the fbi provides examples of common bec scenarios and tips to report and prevent them. Business email compromise (bec) is a type of social engineering attack that takes place over email. in a bec attack, an attacker falsifies an email message to trick the victim into performing some action — most often, transferring money to an account or location the attacker controls. Business email compromise is a targeted social engineering attack that uses email impersonation and trust exploitation to divert payments, steal sensitive data, or manipulate business processes.
.png)
What Is Business Email Compromise And How Do You Protect Against It Business email compromise (bec) is a type of social engineering attack that takes place over email. in a bec attack, an attacker falsifies an email message to trick the victim into performing some action — most often, transferring money to an account or location the attacker controls. Business email compromise is a targeted social engineering attack that uses email impersonation and trust exploitation to divert payments, steal sensitive data, or manipulate business processes. Learn what bec is, how it works, and how to prevent it. bec is a cyberattack technique whereby adversaries pose as trusted figures to trick victims into taking action, such as making payments or sharing data. Learn how to protect yourself from business email compromise (bec), a scam that targets transfers of funds. find out what to do in case of a bec incident and how to file a complaint with ic3. Learn about business email compromise (bec), how it works, and different types of threats. proofpoint shares how to identify and protect against a bec scam. Business email compromise (bec) is a targeted social engineering cyber attack that exploits trust in corporate email systems to manipulate employees into initiating unauthorized transactions or disclosing sensitive information.
Comments are closed.