Building Trust Through Zero Trust

Building Trust Through Zero Trust Enter zero trust, a security framework built on the principle of "never trust, always verify." instead of assuming trust within the network perimeter, zero trust mandates verification at. This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security.

Exploring Building Trust Through Zero Trust In this blog, we'll walk through the fundamentals of zero trust as a primer for the realities of security beyond the perimeter. originally coined by jon kindervag while at forrester research, "zero trust" eliminates the assumption that anything inside your perimeter is safe. The zero trust assessment transforms this process with automation to test for hundreds of security configuration items aligned with the secure future initiative (sfi) and zero trust pillars, then guides you through remediation steps to help operationalize zero trust principles. these tests are drawn from trusted sources in cybersecurity, including:. Explains the zero trust security model ("never trust, always verify"), its key drivers like digital transformation and remote work, its benefits for compliance, and the cisa framework for implementation. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization.
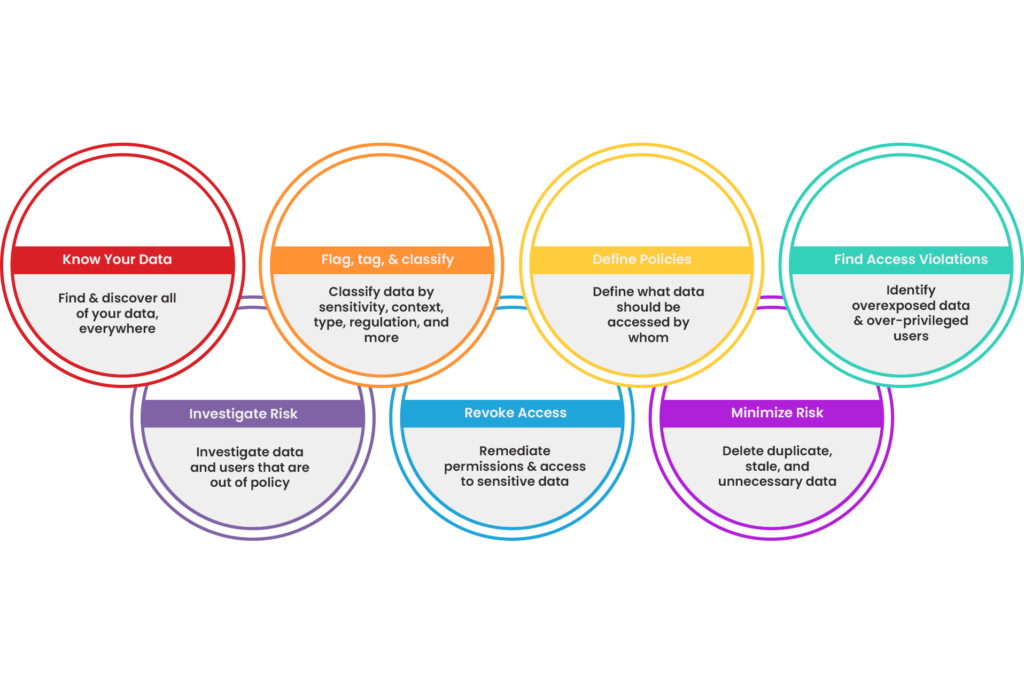
Enable Zero Trust Bigid Explains the zero trust security model ("never trust, always verify"), its key drivers like digital transformation and remote work, its benefits for compliance, and the cisa framework for implementation. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Inspired by the recent sans webinar i spoke at, zta unpacked: the critical technical components of zero trust architecture, this guide helps you strategically choose security solutions that build a zero trust fortress around your environment. To close the security gap, cios need to fully understand what zero trust is and gain strategic guidance and help on the best path forward, which includes a comprehensive, multi layer security approach with zero trust and innovative cyber solutions. In this comprehensive guide, we’ll explore the principles of zero trust, how it builds trust in the modern enterprise, and strategies for effective implementation. Zero trust has become the most misunderstood concept in cybersecurity — most organisations are buying “zero trust products” without building a zero trust architecture. this hub cuts through the vendor noise to deliver a real world implementation roadmap, from network segmentation and identity security to endpoint hardening and threat detection, built on dr. ozkaya’s hands on deployment.
Comments are closed.