Building A Threat Intelligence Program Growing The Program

Building A Threat Intelligence Program Growing The Program By thoughtfully investing in and harmonizing its people, processes, and technology, organizations can build a cti program that not only identifies cyber threats but delivers actionable security. This guide outlines the key steps to building an effective threat intelligence program, the essential components to include, and best practices for operationalizing threat intelligence across an organization.

Building Threat Intelligence Program Threat Intelligence Program In this comprehensive guide, we’ve covered the essential steps to build a threat intelligence program from scratch. if you’d like further details on any section or additional insights,. This white paper provides a practical blueprint for building or strengthening a modern threat intelligence program. Step by step guide to establishing an effective threat intelligence program. learn how to collect, analyze, and act on cyber threat data. Framework to design and launch a threat intelligence program: set requirements, choose tools, staff and train analysts, define workflows, and track kpis.
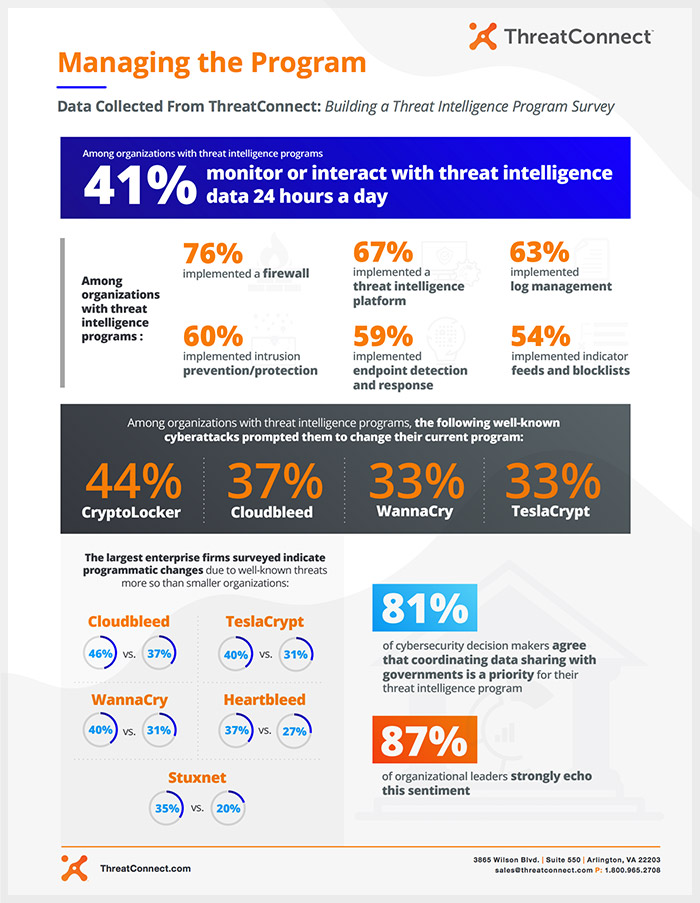
Building A Threat Intelligence Program Managing The Program Step by step guide to establishing an effective threat intelligence program. learn how to collect, analyze, and act on cyber threat data. Framework to design and launch a threat intelligence program: set requirements, choose tools, staff and train analysts, define workflows, and track kpis. This chapter will cover how to build and present the cti program to management and technical stakeholders by providing a starter kit, and it will also provide a guideline to check for how a threat intelligence program should evolve in phases and what is expected during each one of them. Learn how to build an effective cyber threat intelligence program to strengthen your cybersecurity defenses. understand key steps, tools, and best practices for success. Step by step guide for building a modern threat intelligence program for lean teams and mid market organizations. Those who describe their threat intelligence program as more mature than their competitors’ are often utilizing threat intelligence platforms to aggregate and monitor data in one place.
Building A Threat Intelligence Program New Paper Securosis This chapter will cover how to build and present the cti program to management and technical stakeholders by providing a starter kit, and it will also provide a guideline to check for how a threat intelligence program should evolve in phases and what is expected during each one of them. Learn how to build an effective cyber threat intelligence program to strengthen your cybersecurity defenses. understand key steps, tools, and best practices for success. Step by step guide for building a modern threat intelligence program for lean teams and mid market organizations. Those who describe their threat intelligence program as more mature than their competitors’ are often utilizing threat intelligence platforms to aggregate and monitor data in one place.

Solution Building A Threat Intelligence Program Studypool Step by step guide for building a modern threat intelligence program for lean teams and mid market organizations. Those who describe their threat intelligence program as more mature than their competitors’ are often utilizing threat intelligence platforms to aggregate and monitor data in one place.

Building Evaluating A Threat Intelligence Program Part 2
Comments are closed.