Building A Responsible Ai Powered Threat Intelligence Framework

Ai Driven Threat Intelligence Leveraging Machine Learning To Empower A technically sound framework is essential for effective ai powered threat intelligence. this involves robust data acquisition, meticulous model training, secure deployment, and vigilant. But how do we translate these lofty ideals into concrete actions and build a truly responsible ai powered threat intelligence framework? the answer lies in a multifaceted approach that integrates ethical considerations into every stage of the ai lifecycle.
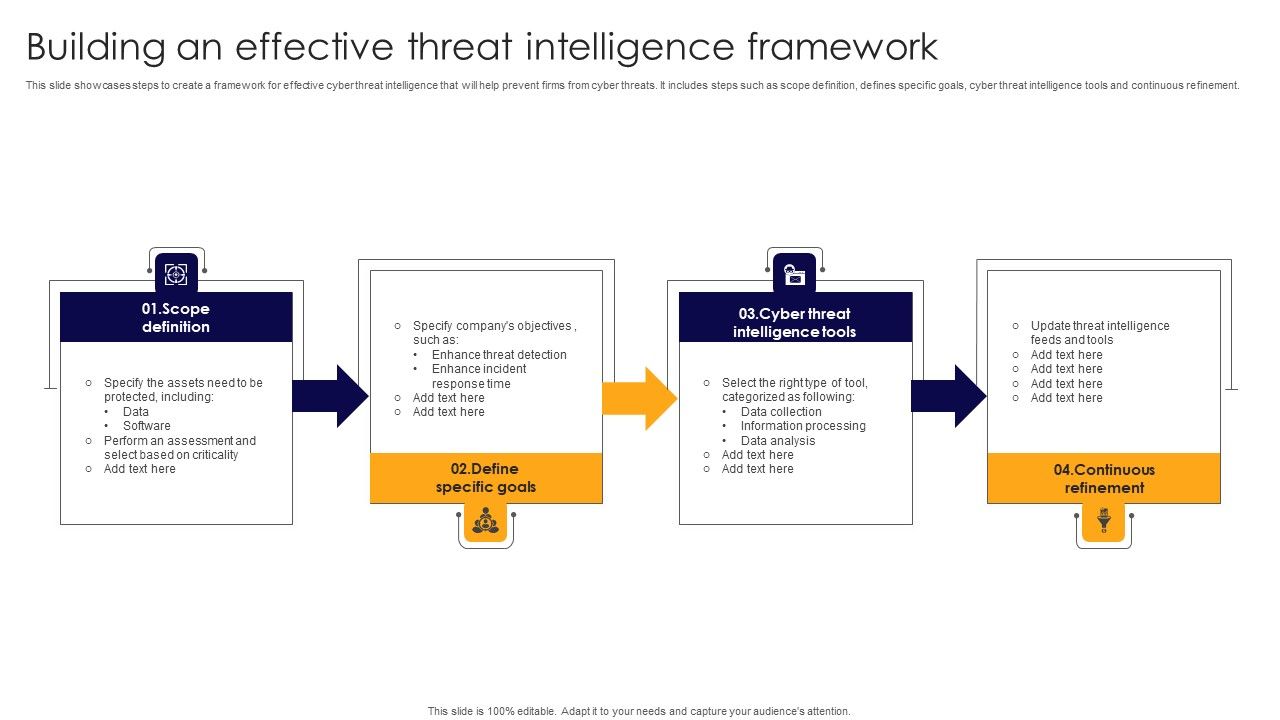
Building An Effective Threat Intelligence Framework Icons Pdf Abstract ai driven threat intelligence is transforming cybersecurity by enhancing real time threat detection, analysis, and response capabilities. Ai generated threat intelligence reports: by automating the analysis and classification of iocs, frontier ai can generate compre hensive threat reports in real time, enabling organizations to adjust their defensive measures proactively. In this blog, i will demonstrate how security teams can use agentic architecture and ai workflows to transform threat intelligence into timely detection and response at scale. From visibility into ai use cases to governance and compliance, our ai security services help cisos take control of emerging risks and implement responsible ai adoption across the enterprise.

Ai Powered Threat Intelligence Analysis For Modern Defense Network In this blog, i will demonstrate how security teams can use agentic architecture and ai workflows to transform threat intelligence into timely detection and response at scale. From visibility into ai use cases to governance and compliance, our ai security services help cisos take control of emerging risks and implement responsible ai adoption across the enterprise. Isaca’s new white paper provides a practical blueprint for building or strengthening a modern threat intelligence program and moving to a holistic threat led approach. This section presents the proposed threatwise ai framework providing a detailed description of the overall framework as well as the different novel tools, concerning cti gathering, extraction, enrichment and sharing. By releasing cai as an open source framework, we aim to empower security researchers, ethical hackers, and organizations to build and deploy powerful ai driven security tools, leveling the playing field in cybersecurity. This paper reviews state of the art ai frameworks, machine learning models, and tools that support threat intelligence, providing a survey of current research in the field and identifying challenges and future directions for real time cybersecurity.
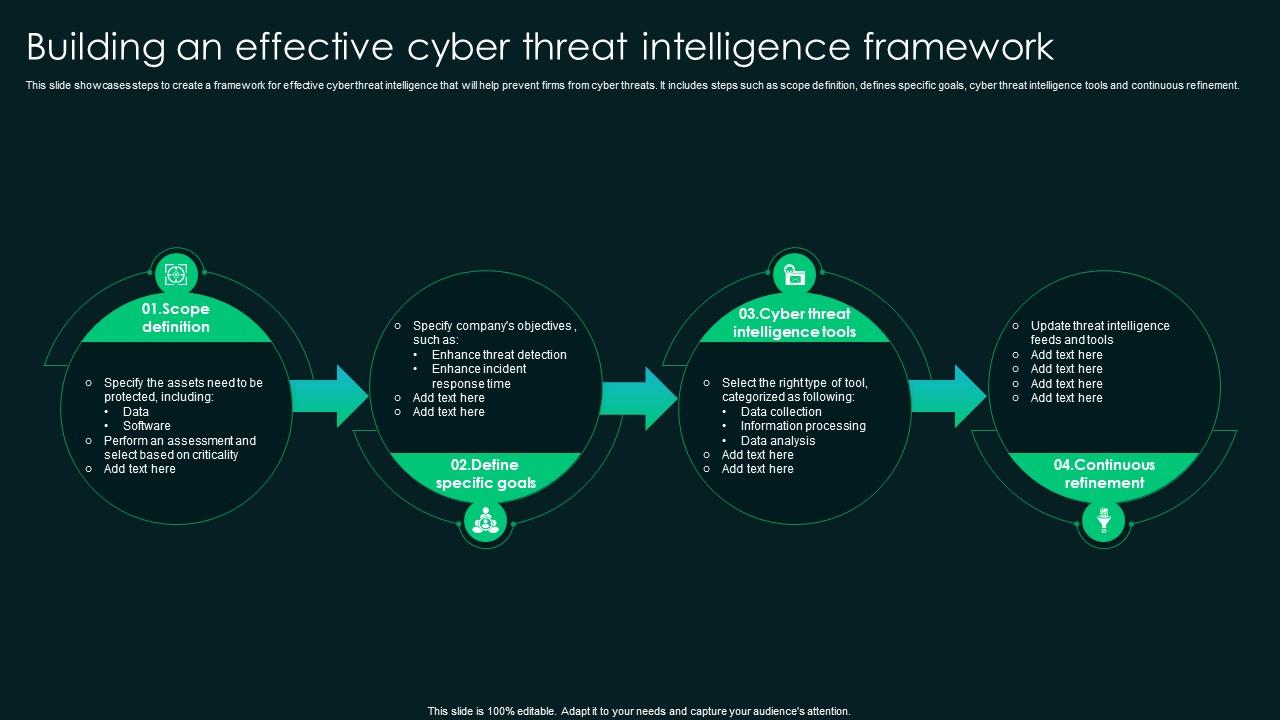
Building An Effective Cyber Threat Intelligence Framework Ppt Presentation Isaca’s new white paper provides a practical blueprint for building or strengthening a modern threat intelligence program and moving to a holistic threat led approach. This section presents the proposed threatwise ai framework providing a detailed description of the overall framework as well as the different novel tools, concerning cti gathering, extraction, enrichment and sharing. By releasing cai as an open source framework, we aim to empower security researchers, ethical hackers, and organizations to build and deploy powerful ai driven security tools, leveling the playing field in cybersecurity. This paper reviews state of the art ai frameworks, machine learning models, and tools that support threat intelligence, providing a survey of current research in the field and identifying challenges and future directions for real time cybersecurity.

Ai Threat Intelligence Initiative Owasp Gen Ai Security Project By releasing cai as an open source framework, we aim to empower security researchers, ethical hackers, and organizations to build and deploy powerful ai driven security tools, leveling the playing field in cybersecurity. This paper reviews state of the art ai frameworks, machine learning models, and tools that support threat intelligence, providing a survey of current research in the field and identifying challenges and future directions for real time cybersecurity.

6 Steps To Building A Cyber Threat Intelligence Framework
Comments are closed.