Build Your Own Cyber Threat Intelligence Program Netsecurity
Build Your Own Cyber Threat Intelligence Program Netsecurity Using threatresponder, you can automate the threat investigation process and get actionable intelligence and custom iocs specifically tailored to the threats encountered on your endpoints. want to try our threatresponder, cutting edge endpoint detection & response (edr) security solution in action?. By thoughtfully investing in and harmonizing its people, processes, and technology, organizations can build a cti program that not only identifies cyber threats but delivers actionable.
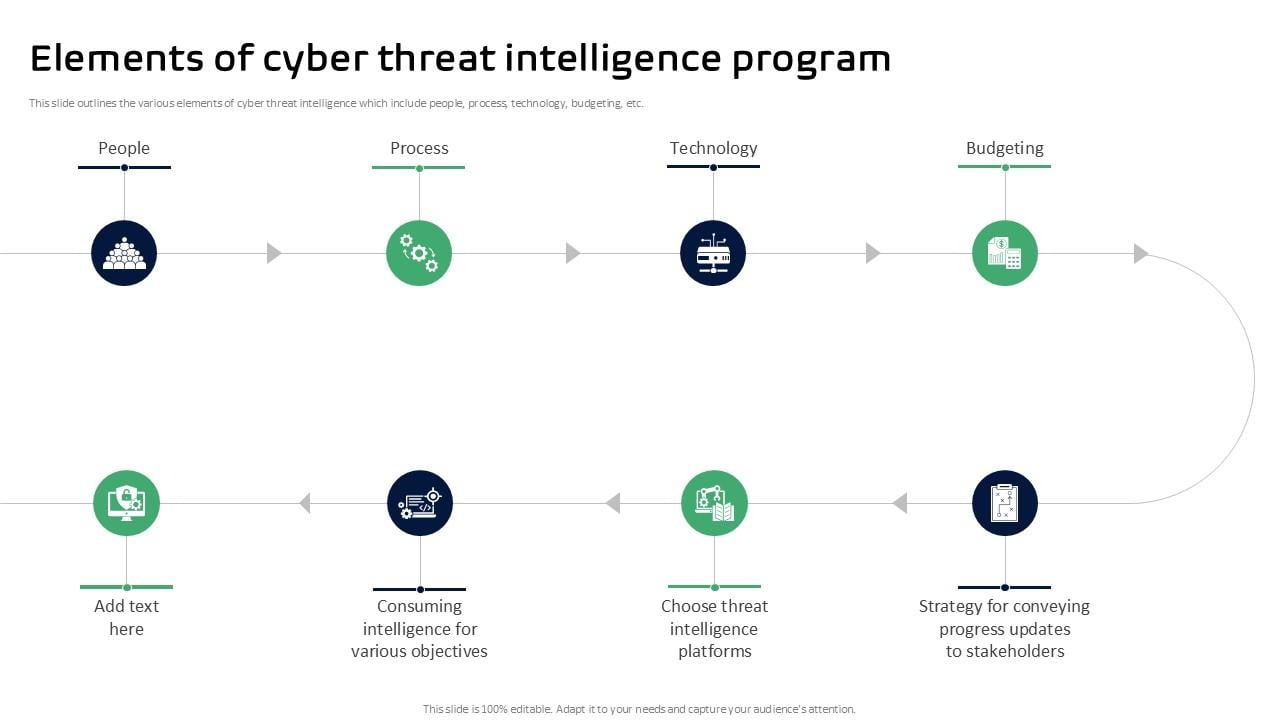
Elements Of Cyber Threat Intelligence Program Threat Intelligence Ppt Slide In this comprehensive guide, we’ve covered the essential steps to build a threat intelligence program from scratch. if you’d like further details on any section or additional insights, feel. This white paper provides a practical blueprint for building or strengthening a modern threat intelligence program. To protect your organization, you need to establish an effective cyber threat intelligence program. in this comprehensive guide, we will walk you through each step of creating a robust threat intelligence program, ensuring your digital assets and data remain secure. Building a proactive cyber threat intelligence program is crucial for staying ahead of potential threats. by gathering and analyzing data from diverse sources, we can better understand adversary tactics and enhance our cybersecurity defenses.

Maturing The Cyber Threat Intelligence Program To protect your organization, you need to establish an effective cyber threat intelligence program. in this comprehensive guide, we will walk you through each step of creating a robust threat intelligence program, ensuring your digital assets and data remain secure. Building a proactive cyber threat intelligence program is crucial for staying ahead of potential threats. by gathering and analyzing data from diverse sources, we can better understand adversary tactics and enhance our cybersecurity defenses. This project is intended to provide a set of guides, tools and resources to establish a cyber threat intelligence program from scratch when your starting budget is $0. In this chapter, we outline how to start a cyber threat intelligence (cti) program and establish a cti team in an organization focusing in particular on the problem cti solves and the value it brings. Learn how to build an effective cyber threat intelligence program to strengthen your cybersecurity defenses. understand key steps, tools, and best practices for success. Opencti is an open source platform allowing organizations to manage their cyber threat intelligence knowledge and observables. it has been created in order to structure, store, organize and visualize technical and non technical information about cyber threats.

Tryhackme Cyber Threat Intelligence This project is intended to provide a set of guides, tools and resources to establish a cyber threat intelligence program from scratch when your starting budget is $0. In this chapter, we outline how to start a cyber threat intelligence (cti) program and establish a cti team in an organization focusing in particular on the problem cti solves and the value it brings. Learn how to build an effective cyber threat intelligence program to strengthen your cybersecurity defenses. understand key steps, tools, and best practices for success. Opencti is an open source platform allowing organizations to manage their cyber threat intelligence knowledge and observables. it has been created in order to structure, store, organize and visualize technical and non technical information about cyber threats.
Comments are closed.