Build An African Cyberpunk Scanner That Detects Renamed Malware Python Tutorial
Github Cytechport Python Malware Scanner This Project Implements A In this tutorial, i'll show you how to build and use grae x magic eye an african cyberpunk scanner that detects renamed malicious files using magic byte analysis. 🌍 african cyberpunk scanner real time malware disguise detection that protects you from renamed malicious files (.exe disguised as .pdf, , etc.) python mit license updated feb 17, 2026.
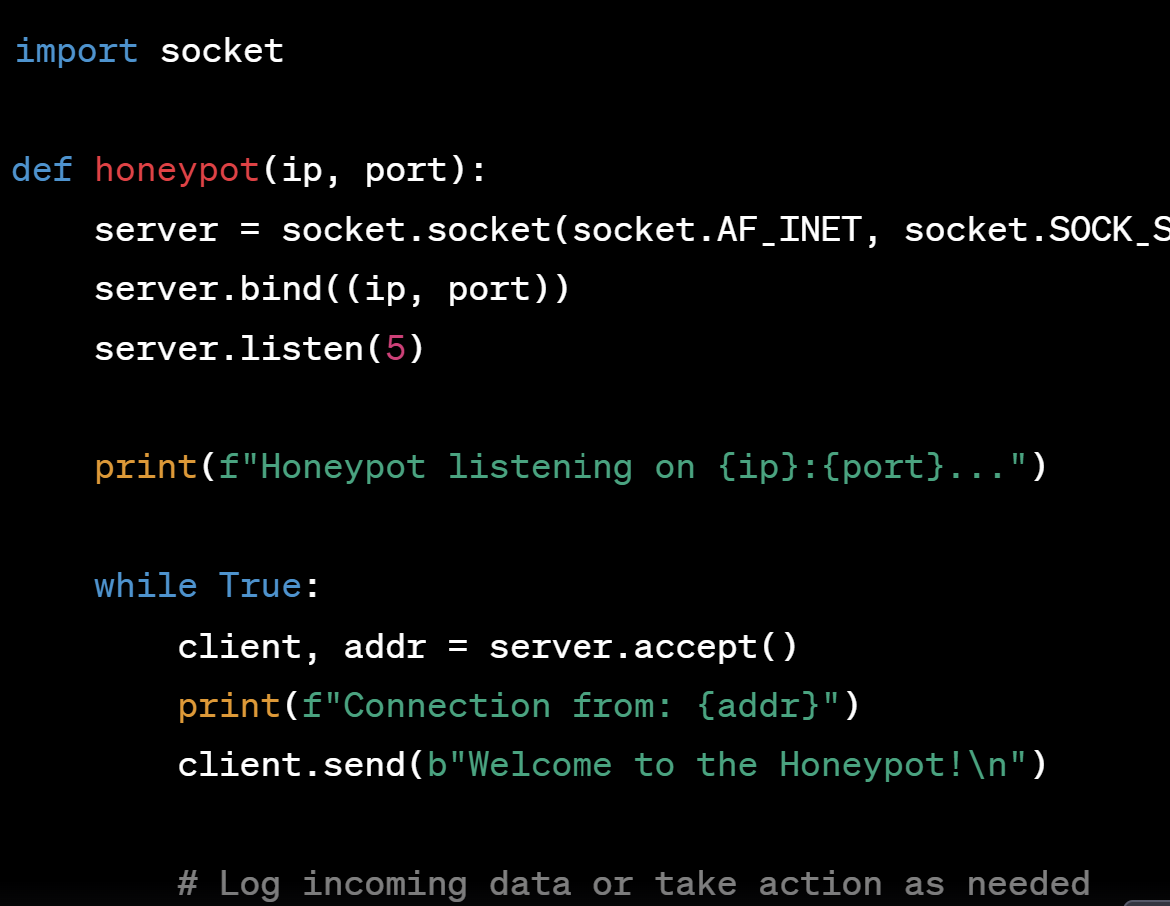
Github Dizthamann Malware Python Project Intro To Cybersecurity Ultimate malware detection guide: learn detection methods, build python security systems, and protect against cyber threats with practical examples. This is a conceptual starting point. a full scale antivirus system would involve a variety of other techniques such as real time scanning, heuristic analysis, sandbox execution, and much more. Developing cyber security projects with python is crucial not only for reinforcing theoretical knowledge but also for gaining practical experience that can be applied in real world situations. through these projects, users can:. Automate repetitive scanning tasks using python’s networking and http libraries and integrate the results with reporting tools. example: create a tool that scans web applications for common vulnerabilities like sql injection or cross site scripting (xss) by sending crafted http requests.

Python Extracting Malware Configuration Cyber Security Architect Developing cyber security projects with python is crucial not only for reinforcing theoretical knowledge but also for gaining practical experience that can be applied in real world situations. through these projects, users can:. Automate repetitive scanning tasks using python’s networking and http libraries and integrate the results with reporting tools. example: create a tool that scans web applications for common vulnerabilities like sql injection or cross site scripting (xss) by sending crafted http requests. A simple python script can calculate and store cryptographic hashes for critical files and alert you if the hash ever changes. this teaches you about hashing functions, file access, and real time alerting. In this article, we will review ten very useful python libraries for malware analysis as well as reverse engineering with sample code that you can easily reuse. In today’s post we’re going to cover using python to apply a standard naming methodology to all our malware samples. depending on where you curate your samples from, they could be named by their hash, or as they were identified during investigation, like invoice.exe. This python script offers a basic blueprint for executing commands with minimal detection risk in authorized red team engagements. by combining base64 obfuscation, random delays, and a clean environment, you can significantly lower the chances of triggering simple alarms or leaving obvious traces.
Ring Zero Labs Analyzing Python Malware A simple python script can calculate and store cryptographic hashes for critical files and alert you if the hash ever changes. this teaches you about hashing functions, file access, and real time alerting. In this article, we will review ten very useful python libraries for malware analysis as well as reverse engineering with sample code that you can easily reuse. In today’s post we’re going to cover using python to apply a standard naming methodology to all our malware samples. depending on where you curate your samples from, they could be named by their hash, or as they were identified during investigation, like invoice.exe. This python script offers a basic blueprint for executing commands with minimal detection risk in authorized red team engagements. by combining base64 obfuscation, random delays, and a clean environment, you can significantly lower the chances of triggering simple alarms or leaving obvious traces.

Analyzing Python Malware A Guide To Malware Analysis In today’s post we’re going to cover using python to apply a standard naming methodology to all our malware samples. depending on where you curate your samples from, they could be named by their hash, or as they were identified during investigation, like invoice.exe. This python script offers a basic blueprint for executing commands with minimal detection risk in authorized red team engagements. by combining base64 obfuscation, random delays, and a clean environment, you can significantly lower the chances of triggering simple alarms or leaving obvious traces.
Building A Python Powered Anti Malware Scanner By Paritosh Medium
Comments are closed.